SQL Injection Union Based Exploitation : Part 2 The Injection This is the second part of the Union Based SQL injection Tutorial for web application penetration testing . If you have missed the first part of the Tutorial , I would suggest you to visit the this Link . The previous part ended with finding the number of Columns in the database . In this part we will actually exploit the Web Application and inject the SQL queries . Here are a few standard SQL functions/queries which will help you in web application penetration testing with the injection . You can consider this a a mini Cheat sheet . If you can … [Read More...]
Featured Articles
Editorial Picks
Latest Blog Updates
 Loading...
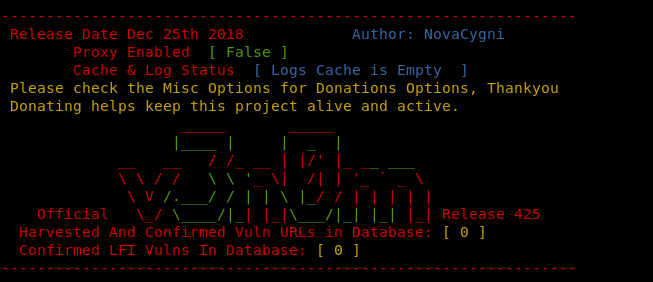
Loading...SQL Injection Union Based Exploitation : Part 1
SQL Injection Union Based Exploitation : Part 1 We have posted a lot on SQL injection . There are various techniques and ways of exploiting the SQL injection loopholes in the Web Application . Many of us exploit SQL Injection holes without knowing what is actually happening on the backend. It might be possible to penetration test a few easy sites by following tutorials exactly as they are. But to actually master the art of SQL Injection, you need to know what is happening and how to alter the way it works. I truly believe that knowing how something works and how to alter the way it works is what differentiates a … [Read More...]
Creating Malicious Word Macros Tutorial : AutoRun Stub via Word Document
Creating Malicious Word Macros Tutorial : AutoRun Stub via Word Document Free Give Away Penetration testers often need to use social engineering attacks . What is more better than creating a Microsoft Office Word document that contains the payload and exploit in form of a Macro . That is easy ... might be common now .... What if the Word Macro would Auto start and execute the payload instantly ? This pen testing tutorial explains exactly how to do that . We will start by creating a Word Macro . Creating Malicious Word Macros Tutorial Step 1: Create a payload. Macros use VBS for macros, so it's not hard to make … [Read More...]
How to be Anonymous Online : BlackHat Method
How to be Anonymous Online : BlackHat Method The Anonymity over the internet has become a challenge after NSA being in the news lately for spying on the citizens . The privacy over the internet has been compromised . Everyone on Internet has a unique IP Address and if someone wants to track you down or research you on the internet , then this IP address reveals a lot of valuable information about you . Though there are many programs and software available on the internet that claim to provide you 100% anonymity over the internet , but being a professional #Pentester for 3 years now , I believe every software / … [Read More...]
Skype Resolver : Get Skype IP’s behind VPN Tutorial
Skype Resolver : Get Skype IP's behind VPN Skype is being used lot in the corporate environments as well as for personal use . Many think behind the VPN the IP and identity can be hidden . Well I came across this awesome tool that resolves your IP using your Skype name . The tool is web based and accessible for free . To use the Skype Resolver all you need is the Skype name of the Target . The Ip behind the VPN is resolved in minutes . This is very useful in certain penetration testing scenarios where the target might be sitting behind a VPN , and we desperately need the IP address . Using Skype Resolver , … [Read More...]