When you are done with this tutorial you will be able to Make and Use a keylogger that is close to fully undetectable, without the victim getting suspicious. You will be able to keylog just about anyone.This Guide will be split into 2 parts:1. Writing your own undetectable keylogger- The language- Logging and storing- Uploading logs2. Setting it up to be un-suspicious and trustworthy- Binding with other files- Making sure its existence is hiddenBefore we begin I want to point out that this keylogger is NOT perfect.It will be unable to record some symbolsIt will occasionally rearrange a letter with one another if … [Read More...]
Featured Articles
Editorial Picks
Latest Blog Updates
 Loading...
Loading...Hack Windows Vista : Five Basic But Important Hacks and Tutorials
Originally Posted by DarkSoulHack the Windows Explorer Shortcut MenuThe right-click menu in Windows Explorer is quite useful; right-click a file and a menu appears, letting you take a variety of actions, such as opening the file, printing it, deleting it, copying it, creating a shortcut to it, and so on. Figure 1 shows you the screen you'll see. (Note that the "Scan with…" option is only available if you install antivirus software, such as avast! Anti-virus.)Figure 1. The normal menu that appears when you right-click a file in Windows ExplorerBut there's a way to power up the menu. Hold down the Shift key as you … [Read More...]
How to Hack Orkut : All Possible Ways Explained Along With Solutions to Protect from them
How To Hack Orkut ??? In this Tutorial I will Try to Explain All the Methods that Any Hacker Can Use To Hack your Orkut account along with Their Prevention Measures.. So Read It Carefully .. Its really a Worth Article and Also very Informative .So Enjoy Reading....Google uses a 4 Level Orkut login which makes it difficult to hack Orkut using brute force attack. First Level - Security-SSL or 128 bit secured connectionSecond Level – Google account checks for cookie in the sytem of user Third Level – Google provides a redirection to the entered User information Fourth Level – Google doesn’t use conventional … [Read More...]
Tips on Buying a Cheap Laptop
Most of Us Always Thinks Which Laptop is To Buy ? Why this laptop Only? How to Save urself From the Lollypops Provided by companies and choose the Best Laptop that will Suits you. For this you Have To consider various Parameter that will help you to buy a new Laptop. Let's Start The Discussion...Today as Every body Knows technology changing quickly, it almost seems that as soon as a new product is purchased, it is considered obsolete. Finding the best deals on laptop computers isn't very difficult if you know what you want, and where to look for it.First, determine the main characteristics that you want or need … [Read More...]
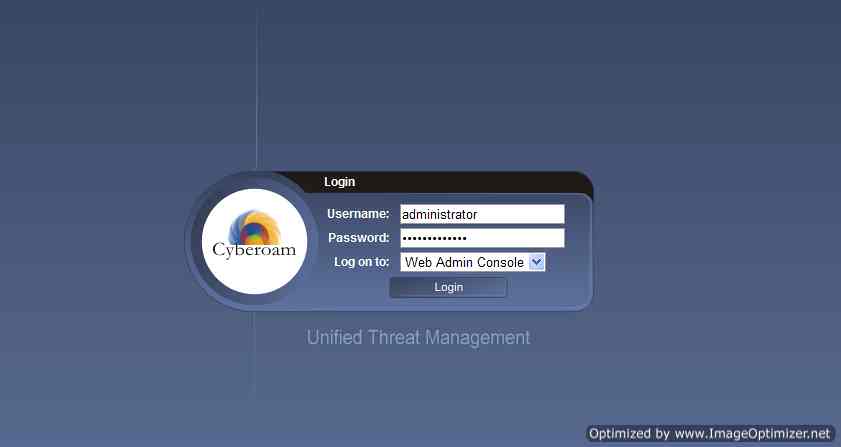
How To Unblock Or Hack Cyberoam To Access The Blocked Sites
Recently, our college opted to upload the Cyberoam client onto their server, and now we can't access 90% of the internet. When we try to go to websites like opera, through Firefox, we get a message saying "Blocked By Your Administrator." Because of this, I am going to give you a detailed hack for Cyberoam, a site used by many colleges. WHAT IS CYBEROAM ?? Cyberoam’s all-inclusive UTM solution offers a well-coordinated defense through tightly integrated best-of-breed security solutions over a single interface -Stateful inspection firewall, VPN, gateway anti-virus, gateway anti-spam, gateway … [Read More...]