If you want to learn hacking, there's no way around it: you need to learn networking. Maybe you needn't master the … [Read More...]

Learn ethical hacking, penetration testing, cyber security, best security and web penetration testing techniques from best ethical hackers in security field.



If you want to learn hacking, there's no way around it: you need to learn networking. Maybe you needn't master the … [Read More...]

Hello everyone, we have already set up the lab environment. In this article, we will discuss about the static analysis … [Read More...]

Linux controls 97% of the server market. As such, any budding hacker ought to know the basic defenses of a modern Linux … [Read More...]
 Loading...
Loading...
Keyloggers make it possible for attackers to see passwords, credit card data, and other private info that users type while browsing the internet and using normal apps. Some keyloggers go even further, taking periodic screenshots or even recording the screen. Although many people think of Linux as a secure alternative to other desktop operating systems like Windows and Mac, there are many ways in which Linux's security leaves much to be desired. In this article, we'll explore how Linux makes it easy (I'd argue, too easy!) to deploy keyloggers to spy on users, and how you can exploit these weaknesses to create your … [Read More...]
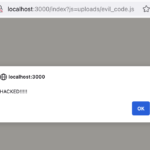
When it comes to web security, XSS is one of the most common vulnerabilities to find. It packs a big punch, making it possible for hackers to deface web pages, steal cookies, and more. A classic attack, XSS has done far better than its peers, such as SQLi, in terms of remaining popular and easy to perform. Of course, web browsers have done everything they can to make this attack harder. And the top technique for preventing XSS is something called a Content Security Policy, or CSP. As the XSS vs CSP battle rages on, this guide will give you a practical, hands on view of how CSPs fight XSS, and how hackers get … [Read More...]

Cybersecurity is an in-demand skillset. At the same time, the market is competitive. One of the best ways to set yourself apart from the crowd is by building a polished, beautiful portfolio. While portfolios are commonplace in artistic fields like photography and design, tech workers are less likely to have one. In this article, I'll guide you through the best strategies for creating an attractive, unique cybersecurity portfolio from scratch. Instead of just dishing out advice, I'll walk the path with you by showing examples by performing each task as well, so you can see how it might look in the real … [Read More...]

Cybersecurity is becoming as one of the hottest job paths in tech. Demand is ever-increasing, but so is competition, as more and more IT workers look toward this attractive option. But, the cybersecurity career market can look like a maze with all kinds of rare niches. How do you choose the right cybersecurity specialization for you? For this reason, we've made this brief guide to give you an idea of the main types of cybersecurity specialization, and how to know which is the best for you. Red team: the crown of cybersecurity specializations Of all the cybersecurity fields, pentesting is the most … [Read More...]
In this booming IT economy the opportunities are out-numbering candidates for those who are applying for cyber security. The covid 19 pandemic has added fuel to this accelerated demand. The report says that these jobs will increase by more than 30 percent in the coming 10 years. Entering into the world of cyber security demands continuous technology awareness and dedication. Here is the comprehensive guide for the beginner’s entry to cyber security. Image Reference: linkedin Understanding the process To unlock a six-figure career in the ever-evolving landscape of technology, a strategic approach … [Read More...]