Hacking websites using Directory Traversal Attacks: Developers nowadays focus on OWASP’s (open web application security project) top ten vulnerabilities. Since hackers use these vulnerabilities to hack websites, developers’ focus has made a hacker’s job more difficult. Hackingloops has developed this tutorial Directory Traversal Attacks (focusing on some of the top ten vulnerabilities).
A directory is basically a folder where web designer’s store their website files (with respect to server). By “directory traversal attack,” I simply mean that the hacker is able to navigate between the directories and the files stored in those directories – like the root, which contains all confi files, htaccess files, ini files, and xquery files. These files are sensible for any website, if their security is not handled properly then a hacker will easily dominate the site.
In short, by using a directory traversal attack, a hacker’s main goal is to get access to any of the sensible files mentioned above.
Attackers can also use directory traversal attacks to view arbitrary files on web servers like SSL private keys and password files.
Directory traversal is also known as the ../ (dot dot slash) attack, directory climbing, and backtracking.
What does ../ or .. (dot dot slash) mean?
The “..” instructs the system to go one directory (or folder) up.
For example, we are at this location C:HackingHacking ToolsBugtraq. Now on typing “..”, we would reach C:HackingHacking Tools.
Again on typing “..”, we would reach C:Hacking and so on.
Let’s again go to location C:HackingHacking ToolsBugtraq. Now suppose we want to access a file named abcfile.txt placed in the folder “Hacking.” We need to type “….abcfile.txt”. Typing “..” twice takes us two directories up (that is to directory Hacking) where “abcfile.txt” is stored.
I hope you understand the dot dot slash concept. Now let’s proceed further.
At this point, we have a complete understanding of what “directory” and “dot dot slash” mean. Now let’s clearly understand what directory traversal attack means.
Directory Traversal attacks is an HTTP exploit or vulnerability which allows attackers or hackers to access restricted directories (most hackers are interested in root directory access) and execute commands outside of the web server’s root directory. The goal of this attack is to access sensitive files placed on a web server by stepping inside the root directory using the dot dot slash technique. By exploiting a directory traversal vulnerability, an attacker can access files in directories other than the root directory. This can be harmful, since access to restricted files containing passwords or other private information may compromise the web server.
For example, by typing the following URL:
The attacker or hacker causes sample.php to retrieve the file “../../../../web-config.php” and display it in the attacker’s or hacker’s web browser. As mentioned above, the character sequence “../” stands for “one directory up.” So the string “../../../../web-config.php” therefore means “go four directories up, then down into the root directory and retrieve the file ‘web-config.php’ from there.”
The attacker needs to guess how many directories to climb in order to get to the desired directory, but this can be done easily via trial and error.
I have set up a live example on my system to explain this vulnerability to users using a tomcat server.
Say I am browsing this page:

Directory Traversal Attacks Screen 1
Now changed “test1/about.jsp” with “../product.jsp” and press enter:
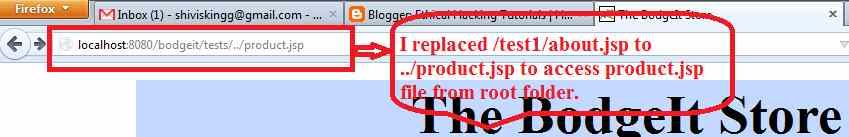
Directory Traversal Attacks Screen 2
Here is the result of the above step. We are able to access product.jsp in the root folder because this sample was vulnerable to a directory traversal attack.

Directory Traversal Attack Screen 3
Note:
Some web applications scan query strings for dangerous characters such as:
- ..
- ..
- ../
to prevent directory traversal attacks.
However, the query string is usually URI decoded before use. Therefore these applications are vulnerable to percent encoded directory traversals such as:
- %2e%2e%2f which translates to ../
- %2e%2e/ which translates to ../
- ..%2f which translates to ../
- %2e%2e%5c which translates to ..
Additionally, in windows Internet Explorer, Microsoft added Unicode characters support, which introduced a new way of encoding “../”, causing their attempts at directory traversal prevention to be bypassed.
Multiple percent encoding, such as
- %c1%1c
- %c0%af
are translated into / or characters.
As a good ethical hacker, we must know how to protect these loopholes while designing or securing a new or existing website. So I will also explain the measures for protecting our website from directory traversal attacks in my next article.

ThuNong says
could you please write another post about IIS Unicode Directory Traversal and Barracuda Local Directory Traversal.
Many thanks