More people than ever are relying on systems like Signal and Urbit to provide seamless, reliable end-to-end-encryption … [Read More...]


Learn ethical hacking, penetration testing, cyber security, best security and web penetration testing techniques from best ethical hackers in security field.




More people than ever are relying on systems like Signal and Urbit to provide seamless, reliable end-to-end-encryption … [Read More...]
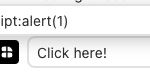
Finding XSS exploits in CTFs is fun, but nothing can match the exhilaration of discovering a vulnerability in a real, … [Read More...]
Hacking Jupyter notebooks is easy and fun, thanks to the lack of any protections by default when you run a notebook. So … [Read More...]
 Loading...
Loading...
Learn how to create your own social media keylogger and by extension how to defend yourself from this kind of invasion of privacy. … [Read More...]

What are zero-click compromises? How can hackers get my credentials through a file share? Do these questions come into your mind and you wonder how this can be possible? Attackers come up with new techniques to compromise users and get hold of credentials for further exploitation. One of the aims is to have the least user interaction to accomplish the goal. One such technique is a URL File Attack. URL File A file with .url extension is a special file containing internet shortcuts that are used by web browsers. This file contains the information for a website's URL address and may also contain the reference … [Read More...]

The previous article was all about how to perform Kerberoasting. This blog will cover one of the interesting attacks. The GPP/cPassword attack was a result of the encryption key leak. We will look into what are GPP and cPassword, and how easier it is to perform the attack. This attack is assigned the CVE-2014–1812. GPP GPP also known as Group Policy Preferences is a collection of Group Policy client-side extensions that deliver preference settings to domain-joined computers running Microsoft Windows desktop and server operating systems. It allowed admins to create domain policies using embedded … [Read More...]

When starting this Active Directory Exploitation series, we talked about abusing windows features. This post will cover Kerberos (an authentication protocol) and how we can abuse it to gain elevated privileges. The procedure followed for abusing the Kerberos feature is termed Kerberoasting. Kerberos Kerberos is a computer network security protocol that authenticates service requests between two or more trusted hosts across an untrusted network, like the internet. It uses secret-key cryptography and a trusted third party (Key Distribution Center; KDC) for authenticating client-server applications and … [Read More...]

We have been doing the Pass The Hash/Password attack in the previous article. This article will focus on tokens and how we can perform token impersonation to gain access to the resources. Tokens For ease of understanding, you can think of tokens as cookies for the computer. These temporary keys allow you access to a system, a network, or a resource without providing the credentials. A web pentester can think of them as cookies or tokens (JWT etc) for accessing credential-protected resources. Types of Tokens There are two types of tokens Delegate TokenThese tokens are for the interactive logons, … [Read More...]