In this article, we will be going through how rendering engines can be vulnerable and give access to the system. There … [Read More...]


Learn ethical hacking, penetration testing, cyber security, best security and web penetration testing techniques from best ethical hackers in security field.




In this article, we will be going through how rendering engines can be vulnerable and give access to the system. There … [Read More...]

After gaining initial access to the systems, many attackers face the problem of having low privileges over the system. … [Read More...]

Have you ever been browsing the internet and then all of sudden a file downloads into your system? And all that without … [Read More...]
 Loading...
Loading...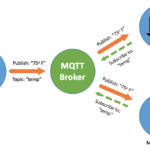
In the previous article, we had gone through IoT Security as an overview. Now is the time to learn about the protocols that IoT uses for communications. In this article, we will talk about pentesting IoT protocol MQTT by walking through the Pentester Academy labs. MQTT MQTT stands for MQ Telemetry Transport. It is an OASIS standard messaging protocol for the Internet of Things (IoT). By design, it is an extremely lightweight publish/subscribe messaging transport. This characteristic makes it ideal for connecting remote devices with a small code footprint and minimal network bandwidth. This protocol is a … [Read More...]
The past several years have seen an explosion of hype about Rust. For 6 years in a row, devs have voted Rust as the most loved programming language. And it's no surprise. Rust adds real innovation to systems programming, a field that was stagnant for decades. So of course, there's growing interest in the benefits of Rust for security engineers. So what do we, as security engineers, need to know about Rust? In this article we'll explain exactly that. First, we'll give you a small taste of how Rust makes low-level coding safer. Then we'll look at common vulnerabilities that affect Rust software. Finally, we'll … [Read More...]

Before diving into IoT Security, it is important to know what is IoT and why we need it. IoT stands for Internet of Things. It is a system of interrelated computing devices assigned unique identifiers (UIDs) and the ability to transfer data over the network. This transfer is not dependent on any interaction (human-human or human-computer) rather it is completely automatic. Adoption With the speedy adoption of technology and involvement of the internet in our daily lives, we feel comfortable automating things and instructing/controlling them remotely. IoT provides an ecosystem in which each appliance is … [Read More...]
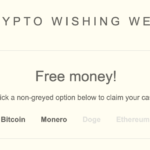
Most people believe that their browsing history is private. However, trackers on websites have clever ways of uncloaking other sites you've visited. When sites use such tricks to invade your privacy, security engineers call it "history sniffing". There are a few ways that sites can make this happen: Using the :visibility psuedo-class in CSS. Browsers try to stop this, but it still works.Shared cookies across sites, like Google's Adsense. However, this requires multiple sites to cooperate, and only gives you anonymized metadata, not the history of specific individual users.Measure the speed at which a user … [Read More...]

Nowadays, most of the user base has shifted to mobile phones. People are not only using their smartphones for calls, and sending SMS but also beyond that. Other activities include web browsing, socializing, photography, and much more. Android hacking using msfvenom is one of the simplest methods to hack android phones. Android Market Coverage Most of the users choose Android phones compared to other ones. Android has been so successful that it already captures 80% of the market share. This figure will rise to 90% by 2022 as per the expectation. Having a huge user base obviously attracts the hackers and … [Read More...]