MITRE ATT&CK will literally change your life if you are in cybersecurity in any type of capacity. Finally the industry has finally gotten on the same page and we now have something where we can understand how attacks happen and are broken down in a way we can all understand. You literally can look up any popular attack and see all the steps that attack took to become successful.
MITRE is a non-profit organization established in 1958, with a goal to “solve problems for a safer world”. ATT&CK is one of the many ways the company is fulfilling this goal. It is a meticulously maintained, frequently updated, and globally accessible knowledge base of tactics and techniques, employed by hackers/adversaries before, during, and after infiltrating a system. The knowledge base extracts its insight from real-world observations, and is used to develop threat and network defense models by private companies, government agencies, and the cybersecurity community.
At a broad level, the MITRE ATT&CK comprises of three main matrices: Pre-ATT&CK, Enterprise ATT&CK, and mobile. These matrices combine to give a holistic overview of the complete attack lifecycle (from recon to exfiltration), enabling security analysts to catalyze the process of discovery and recovery.
Pre-ATT&CK
This matrix contains an exhaustive list of tactics and methodologies pertinent to the adversary behavior before the attack. It focuses on the different steps adversaries take during recon, and how they utilize the gathered intel to identify weaknesses to exploit. Some of the covered topics in this matrix are:
- Priority detection planning
- Target selection
- People information gathering
- Technical weakness identification
- Establish and maintain infrastructure
- Persona development
- Build capabilities
- Test and stage capabilities
All aforementioned techniques have various sub-categories which go to various lengths to shed light on the way adversaries think, move, and operate. For example, the target selection topic covers everything from attack vector determination to strategic target determination. A complete list of Pre-ATT&CK techniques are mentioned here.
Enterprise ATT&CK
The hardest nut to crack in cybersecurity isn’t preventing infiltration; it’s defending your system after you have been compromised. Your barricades have been breached and if you don’t act promptly and smartly, you are only adding to your loss. The chances of panic are manifold. This is why MITRE came up with the Enterprise ATT&CK matrix. It covers all the possible ways an adversary can act post-penetration. The matrix covers the exploit, maintain, execute, and aggravate stages of an attack via topics like the following:
- Initial access
- Execution
- Persistence
- Defense evasion
- Discovery
- Lateral movement
- Command control
- Exfiltration
- Impact
Once again, all the above-mentioned techniques have various sub-categories of their own. For example, in the discovery topic, there is a huge list of relevant sections including (but not limited to) application window discovery, cloud service dashboard, network service scanning, password policy discovery, and virtualization/sandbox evasion.
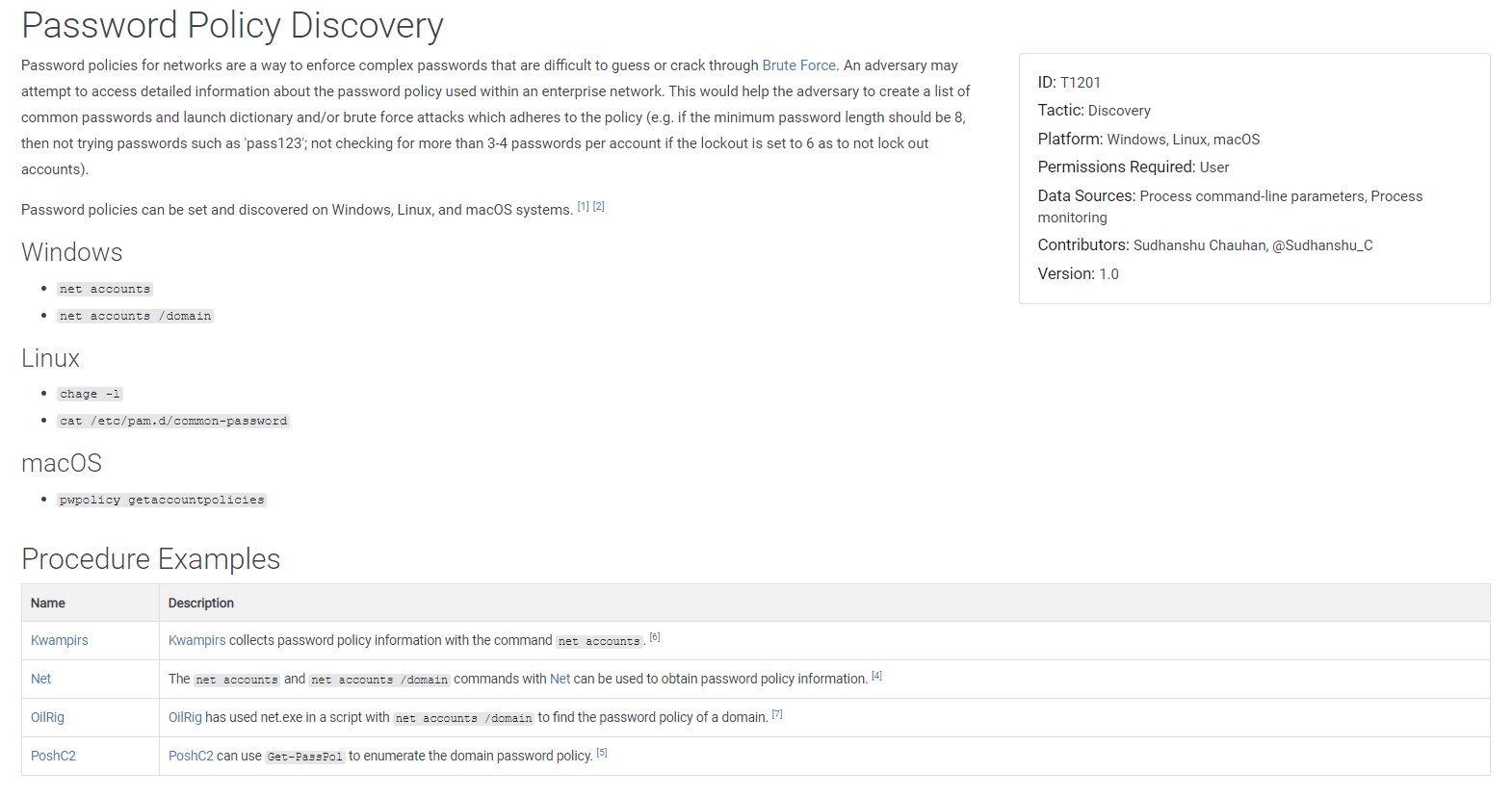
The Enterprise matrix has separate lists of techniques for Windows, MacOS, Linux, and cloud platforms. Find the complete list of covered techniques here.
Mobile ATT&CK
The mobile matrix also covers the tactics and techniques in play post-infiltration, but for mobile devices. There are two different matrices; one each for Android and IOS platforms. The matrices also describe some of the device access and network compromising approaches that can be used by hackers without having direct access to the devices. Some of the covered tactics are as follows:
- Initial access
- Persistence
- Privilege escalation
- Credential access
- Defense evasion
- Collection
- Exfiltration
- Command and control
- Network and remote service effects
The matrix is very comprehensive; it breaks down all the various potential steps that could be taken in all of the aforementioned categories. From downgrading to insecure protocols and rogue Wi-Fi access points in Network Effects, to obtain device cloud backups and remotely wiping data without authorization in Remote Service Effects; from application discovery and network service scanning in Discovery, to capturing audio and capturing SMS messages in Collection; all relevant bases are covered.
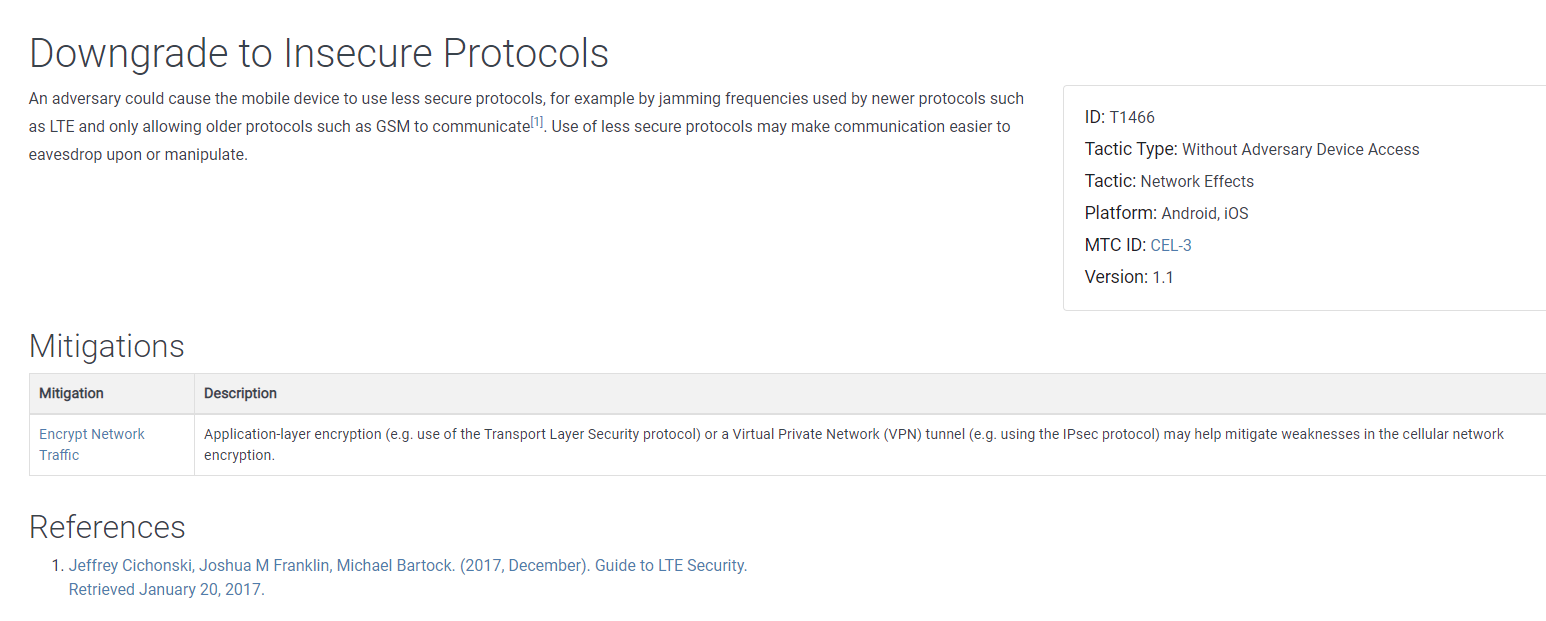
You can find the non-exhaustive list of mobile matrix techniques here.
What Makes MITRE ATT&CK so Useful?
Aside from the obvious benefits of information aggregation, MITRE ATT&CK can be useful in many other ways:
- Study and structure the various ways attackers can challenge your defenses. This involves the famous tools, tactics, and techniques used by adversaries historically. Knowing what to expect is the obvious first step in building a safe cyber infrastructure.
- Think like the adversary. ATT&CK is a knowledge base compiled from the vantage point of an adversary. By studying the material, you are able to understand how some of the best cyber attackers think.
- Learn how to simulate real-world cyberattacks by going through a database of the most famous historical breaches.
- Build your very own red/blue/purple teams that will be responsible for handling different aspects of your defense against adversaries.
- Don’t leave anything to chance. Using MITRE ATT&CK, security analysts and architects can know everything they need to design and build a network/system that can withstand even the most sophisticated of adversary attacks.
Practical Use-cases for ATT&CK
MITRE ATT&CK has helped hundreds of thousands of companies to build strong and sophisticated cyber defenses. Here are some use-cases for the framework:
- Build a defense manifesto using the most readily used infiltration techniques. This will help in prioritizing what to look for in chaotic situations.
- Performing audits and gap analysis of deployed systems and networks with an attempt to enhance levels of security.
- Using ATT&CK as a reference/standard when sharing information across security teams or third-party vendors.
- Correlating the documented techniques and tactics to relevant data within the local environment to have better chances at hunting threats.
- Keeping tabs on the evolution of techniques, tools, and methodologies to update adversary personas periodically.
- Persona building/emulation of adversaries during simulated red and blue team exercises.
- Achieving different cybersecurity compliances (HIPPA, PCI-DSS, FERPA etc.) by finding out the cybersecurity best practices and standards.
Final Word
Every 30 seconds, a new cyberattack takes place. In such a world, resting on your laurels when it comes to cybersecurity, just isn’t an option. MITRE ATT&CK is a great framework to leverage for building a strong cyber defense. However, it’s much more than that. It helps security experts to build in their mind, a thorough understanding of how an adversary thinks, making it possible for them to give adversaries a run for their money.
