You may be wondering what access control certifications you can go after to further your career and it can get a bit confusing. We put together what we think are the best certifications when it comes to identity and access management that will also get you noticed.
In Information Security, access control methods are applied to restrict the availability of data (and resources) to those who comply with the security policy. Two general Access control models are: (1) Role-Based Access Control (RoBAC) and (2) Rule-Based Access Control (RuBAC) models. In RoBAC model, the users are granted access to the data and other resources on the basis of their role in the organization. For example, each university student may be granted access to only educational stuff through online university portal, however, the administration block may be granted access to the whole university database. In RuBAC, rules are attached to the data or resources. For example, there can be a rule for employees to access office data through only office IP address.
The goal of access control is to prevent unauthorized access. However, the restriction of resources to the complied entities requires vast domain knowledge and expertise because the attackers work against all those measures that prevent them from accessing sensitive data or access privileges. Despite the fact that Access control management plays an important role in preventing unauthorized access and mitigating the risk of a data breach, there are only few organizations that offer access control training and certifications. Following is a brief overview of these access control certifications currently available in the industry. The individuals can benefit from these certifications while pursuing a career in access control management field.
GIAC Critical Controls Certification (GCCC)
GIAC (Global Information Assurance Certification) offers GCCC certification aligned with the security controls recommended by CIS (Center for Internet Security, Inc.). CIS is a non-profit entity working against global cyber threats by harnessing the efforts of the global IT community. CIS has defined 20 security controls divided into Basic, Foundational, and Organizational security controls.
Who Should Avail GCCC
The main objective of GCCC is to master the access control domain. Therefore, it is a recommended certification for those who want to excel in this specific domain. People working or preparing themselves for the following job positions are encouraged to pursue GIAC Critical Controls Certification.
- Security auditors
- System administrators
- IT administrators
- Network security engineers
- Federal agencies personnel
- Security vendors
GCCC Exam Requirements
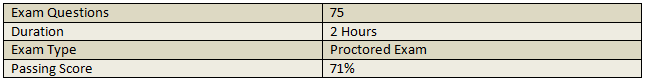
There is no practical experience required to take GCCC exam. The interested candidates must register online for the exam. The exam must be scheduled in advance and taken through GIAC proctored test centers. The exam outlines are mentioned below.
GCCC Exam Focused Areas
GIAC offers GCCC training to prepare the candidates for the exam. The important Access control management areas covered in GCCC exam are listed below.
Controlled Use of Administrative Privileges: The topic covers the processes and tools required to control the administrative privileges on networks, computers, and applications.
Controlled Access (Based on Need to Know Principle): Familiarity with the processes and tools required to control access to the information on the basis of the need to know and right to access principle.
Inventory and Control of Hardware Assets: Familiarity with the processes and tools used for controlling the devices’ access to the networks based on asset inventory i-e which devise are allowed to connect with the network.
Inventory and Control of Software Assets: Knowledge of tools and processes required for installation and execution of approved software on computers.
Limitation and Control of Network Ports: The candidate must know how to limit or control the ports, network protocols, and services.
Wireless Access Control: Knowledge of processes and tools used to manage the security of Wireless networks.
Account Monitoring and Control: Ability to use tools and processes to control/track/prevent the use of application and system accounts.
Continuous Vulnerability Management: The individuals interested in GCCC exam must be familiar with the tools and processes required for the continued monitoring of vulnerabilities that can breach the access control protocols.
Data Protection and Recovery: The candidate must have a strong knowledge and skills to secure the data resources and ability to recover the data in case of the security breach.
GCCC Renewal Requirements
GCCC certification is valid for a period of 4 years. Candidates can renew their GCCC credentials through any of the following two options.
1) Retake the current version of GCCC exam
2) Earn Continuing Professional Education credits (CPEs)
More details about GCCC exam and certification renewal policy can be found here: https://www.giac.org/certification/critical-controls-certification-gccc
Certified Identity and Access Manager (CIAM)
CIAM is a vendor-neutral access control certification offered by Identity Management Institute (IMI). IMI is an international organization that offers training and certifications in different identity and access management areas, such as operations, management, compliance, and governance. CIAM certification validates the candidates’ access management abilities while dealing with resources including enterprise data.
Who Should Avail CIAM
The main focus of CIAM is identity and access management. The certification is highly recommended to experts who want to manage, design, improve, or implement access management programs, tools, and processes in businesses, technology companies, and various public & private organizations.
CIAM Exam Requirements
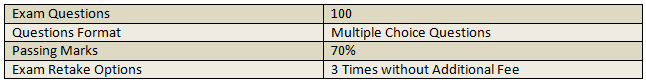
CIAM-interested candidates must be a member of IMI to apply for the online examination. Candidates who apply for CIAM exam online receive a study guide for exam preparation. IMI also offers video training for exam preparation. The exam details are listed below.
CIAM Critical Risk Domains
Identity Management Institute uses the following Critical Risk Domains (CRDs) for CIAM certification. Candidates must have a good grasp of these domains in order to pass the CIAM exam.
- Access Management Tools
- Lifecycle and Transformation
- Access Review and Certification
- Access Request and Approval
- Provisioning and De-Provisioning
- Program Management
- Auditing and Reporting
- Enforcement
- Account Reconciliation
- Strategy and Governance
CIAM Renewal Requirements
CIAM certification is valid for a period of 3 years. Candidates can earn and present CPEs at random audits by IMI to maintain the certification. CPEs equivalent to 60 hours are required to be submitted over a period of 3 years. The candidate must submit at least 15 hours of CPEs each year to maintain the certification.
More information about CIAM exam and certification maintenance can be found here: https://www.identitymanagementinstitute.org/ciam/
Certified Access Management Specialist (CAMS)
CAMS certification is another access management certification offered by IMI that focuses on users’ interaction policies and accounts management skills. CAMS certification evaluates the users’ ability to demonstrate the knowledge and skills required to maintain access control, mitigate access risk, and implement the access control policies that should comply with the legal and contractual requirements of organizations.
Who Should Avail CAMS
CAMS certification can be beneficial for professionals who are performing the following job tasks while serving at different security positions.
- Receiving and verifying users access request
- Granting, revoking, or modifying access rights
- Monitoring users access activities
- Following up, investigating, and resolving access rights
CAMS Exam Requirements
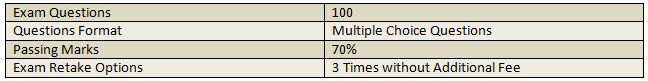
Exams requirements for CAMS are similar to CIAM exam. Candidates must register online to become and member of IMI. The following exam format is followed for CAMS certification.
CAMS Critical Risk Domains
The CRDs required to be studied for CAMS exam include the following.
- Security Threats
- Threats Objectives
- Access Controls
- Access Control Matrix
- Rights Management
- Event Management
- Identification
- Authorization
- Authentication
- Logging and Monitoring
CAMS Renewal Requirements
CAMS certification is valid for a period of 3 years. CAMS holders must submit 60 hours of CPE, of which at least 15 hours each year to be submitted to maintain the certification.
For exam registration and more information on CAMS, visit the official IMI website here: https://www.identitymanagementinstitute.org/cams/
Certified Information Systems Security Professional (CISSP)
CISSP is a renowned certification that validates the technical and managerial expertise of the professionals in designing, engineering, and managing the overall security posture of organizations. We have already discussed CISSP domains and certification in detail. CISSP holders are fully capable of working in any access control environment due to the Identity and Access Management domain included in CISSP exam. The Identity and Access Management domain contributes 13% in candidates’ evaluation process. The CISSP exam validates the following Identity and Access Management knowledge and skills of professionals.
- Physical and logical access Control of assets
- Identification and authentication of devices, people, and services
- Integration of identity as a third-party-service
- Implementation and management of authorization mechanism
- Identity management and provisioning of access lifecycle