Ready To Hack Your Way Into Cyber Security But Unsure Where To Start?
Learn Real-World Cybersecurity Skills —Without Coding, Certifications, or a Degree
Most Effective Cyber Security Career Switch Blueprint To Get You Hired.
0
+
Student Worked With
0
+
Year Of Experience
0
+
Social Media Following
0
Previous Experience Required
The Most Effective Way to Learn Cybersecurity—Period.
If you’re serious about breaking into cybersecurity, you don’t need another cert or theory-heavy course. You need a blueprint. A step-by-step guide that shows you exactly what to do—what to learn, how to practice, and how to get hired. That’s exactly what you’ll find here.
This isn’t lecture-based learning or recycled content. It’s hands-on, real-world training designed to make you think—and work—like a cybersecurity pro from day one. You’ll build the skills employers actually care about by solving real problems and navigating real threats—just like you’d do on the job. We designed this to cut out the fluff so you can flatten your learning curve and get this done quicker by not spending countless hours learning stuff that doesn’t matter.
Think you need a degree or endless certifications to get into cybersecurity? You don’t. We’ve helped people with no prior experience land cybersecurity roles without a single cert or coding background. Why? Because what matters most isn’t your credentials—it’s your ability to solve problems and think like a security professional.
This program builds exactly that. You’ll be learning, practicing, and building a portfolio of real-world skills—without wasting time on expensive, outdated credential-chasing. If you’re ready to stop guessing and start executing a proven plan, you are in the right place.
Focus On Exactly What Matters To Make It In Cybersecurity
Ethical Hacking and Penetration Testing
Learn Cybersecurity a fun way, through hands-on Ethical Hacking and Penetration Testing techniques.
Master Cybersecurity Foundations
Go from zero experience to having an excellent cybersecurity foundation to lean on o matter what specialization you are looking to enter.
Hands on Real-World Training
Study and read all you want, but if you can’t perform on the job day one it is meaningless. That is the reason our philosophy is to practice real scenarios.
Build a Portfolio
The truth is communication is most valuable skill in any profession. You need to be building towards something and create a body of work to prove you can do the job.
Feeling Stuck and Wondering if Cybersecurity is even for you?
You’ve probably seen the job listings—“5+ years experience required”—and thought, How am I supposed to get that if no one will give me a chance? Maybe you’ve racked up a few certifications, but they haven’t moved the needle. The truth is, what you’re missing isn’t more theory or another certification—it’s hands-on, real-world experience that proves you can actually do the job. That’s where we come in. If you’re tired of wasting time and staying stuck, there’s a smarter way forward—and it starts here.
What Other Students Say
I work as a system administrator in charge of the security of the entire network and saw a great opportunity with the membership to learn more about hacking and understanding more about ways to improve our security at work. The community was helpful with up to date news, practice tests and labs that helped me. Thanks a lot for your support.

I purchased this membership because it seems like a great place for beginners like myself to learn how to set up labs an run tests on our own without much equipment. Also the language is one that is understandable there isn’t a lot of what I like to call “jargon” its very clearly explained and that’s what I liked the most simple explanations for tasks that can be complex.
The information available on the site is easy to understand and train yourself in the ways of the ethical hacker.

Wow you guys are amazing thanks so much, ethical hacking has always been something I was interested in….thank you so very much for the lessons and knowledge to make my dreams possible

Gain Real-World Skills Designed To Get You Hired
At HackingLoops, our blueprint offers real-world training that gives you the practical, hands-on experience employers demand on day 1 upon hire. All without without needing to code, chase expensive certifications, or go back for a degree.
By applying your knowledge in real-world scenarios, you’ll bridge the gap that has been keeping you from getting started — mastering core cybersecurity skills faster, more effectively, and with confidence.
Essentials Windows Command Line Cheat Sheet for Cybersecurity Pros
Every second counts during a cybersecurity incident. Knowing your way around the Windows Command Line can be the difference between containing a breach, and watching
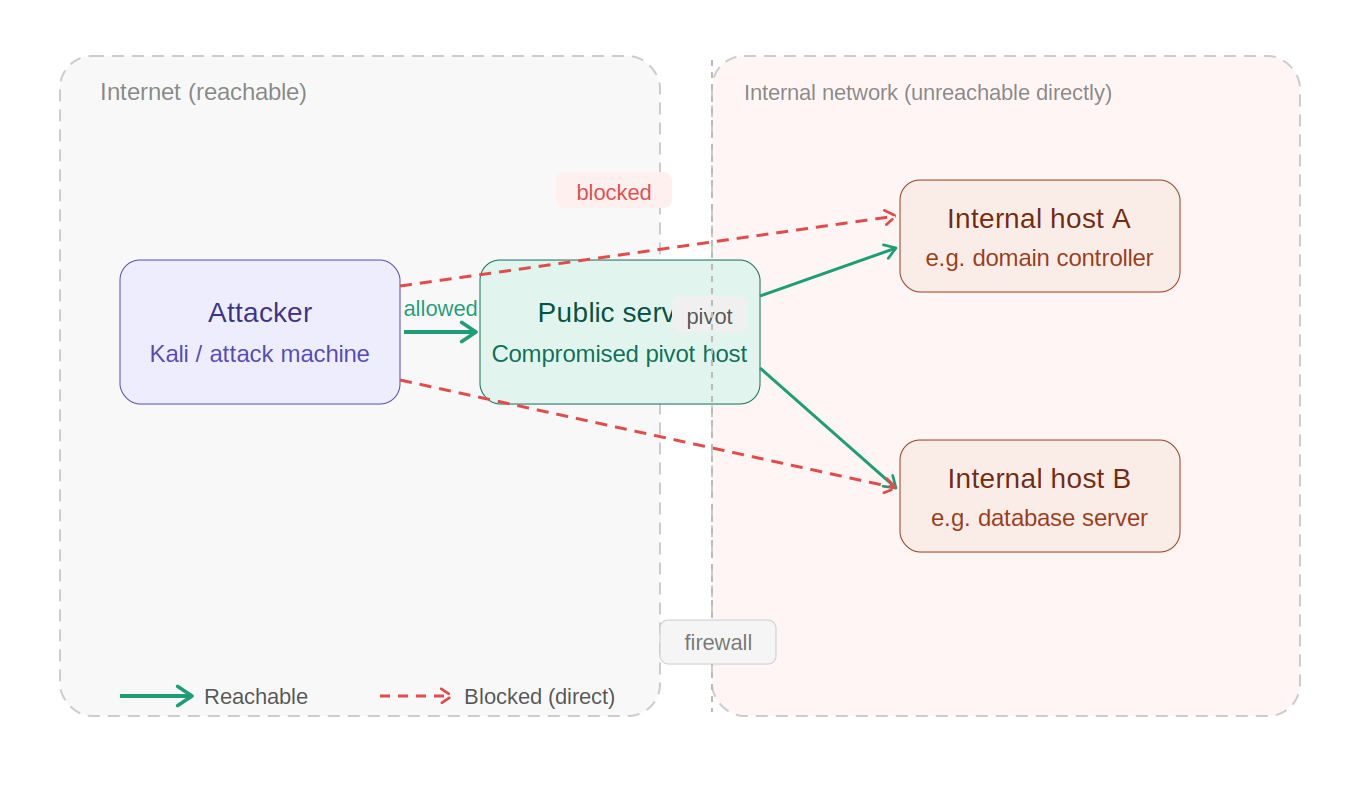
How to Use Ligolo-ng: Beginner’s Guide to Tunneling and Pivoting
Imagine you are doing a pentest engagement on a network and luckily you gain initial access. Next step you would do is trying to pivot
Gobuster & ffuf Cheat Sheet Ultimate Guide
1. What Are Gobuster & Ffuf? (And When to Use Each) You’ve mapped a target web application, intercepted some traffic in Burp Suite, and found
