How to Use Ligolo-ng: Beginner’s Guide to Tunneling and Pivoting
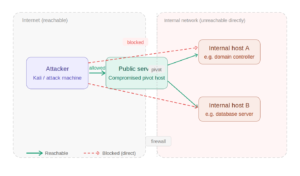
Imagine you are doing a pentest engagement on a network and luckily you gain initial access. Next step you would
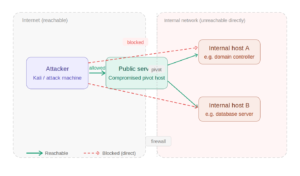
Imagine you are doing a pentest engagement on a network and luckily you gain initial access. Next step you would

This NetExec Cheat Sheet introduced a network security tool that helps you test the safety of Windows networks. It has

Introduction to Kali Linux Kali Linux is a Debian-based Linux distribution designed for penetration testing, forensics and security auditing. It
Introduction: Connecting the Dots in a Digital World In our interconnected digital universe, information is everywhere. A single email address,