
Windows Penetration Testing Tools: Top Picks for Ethical Hackers
Pentesting is a huge field, and security audits often require massive investments of time and effort. Performing a complete security

Pentesting is a huge field, and security audits often require massive investments of time and effort. Performing a complete security
How To Install The Amnesic Incognito Live System (Tails) It is pretty easy to install a Debian-based Linux distro like
Welcome back my fellow hackers! I was thinking recently, and came to the realization that we haven’t really been cooking
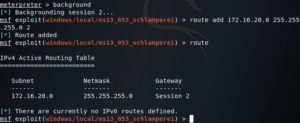
Today we’re going to be going over something I’ve been working on for a while, pivoting. First, we’ll discuss what