
Mobile Application Penetration Testing Basics
Mobile application penetration testing is like a security check for your phone and apps. It helps find and fix any

Mobile application penetration testing is like a security check for your phone and apps. It helps find and fix any
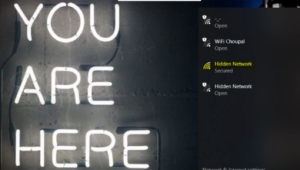
In this article we are going to demonstrate how to find ssids that are hidden over the network. People believe

Cuckoo sandbox is an open-source malware analysis system that can perform the dynamic and static analysis of PC files in

There are millions of mobile applications available for Android and iOS users. The download statistics of many of these applications