The IP address has many functionalities. Ping sweep is a term related to it. Scanning ping is one of the most efficient ways to find network vulnerabilities and tackle network-related discoveries. It also saves lots of time because the procedure related to ping sweep is pretty simple. Pinging a simple service similar to google.com gives back many results and we can learn our situation depending on the result we get back.Pinging a network or system allows us to determine if a host is alive or dead. This network-based utility can ping one simple IP or brute check a list of IPs in a single or continuous scan. In response to pinging a host, we get back data as an echo. By calling it alive, we can identify if the system is active and what is the network-based status around it. And dead means the host is either inactive or non-responsive or in shutdown mode. Hosts can be the network servers, computers, websites, printers, or any remote network device.
Ping Sweep is an information-gathering technique used to identify live hosts by pinging them. In more technical terms it is also known as Ping scan, or Internet Control Message Protocol (ICMP). One host like the user requests data and the receiver host accepts it, furthermore sends back packets of information in bytes. In between these packets they get validated and a response comes back to the sender host. For this reason, ping sweep or ping scan is also known as a two-way handshake protocol.
Ping and Ping Sweep are not the same
The use of ping system first began with sonar technology. There are numerous numbers of submarines that go deep into the ocean and visibility is zero there. No light can pass, but the sound waves can. As water is a great conductor of sound. What sonar technology does is, sends signals in all directions. The sonar signal bounces back from obstacles on all sides, making it possible to map live data from around the area. The system was called pinging and thus we got the name, but in computing, it is used as an IP network utility tool and called pinging.
Network administrators have the capability to ping devices connected to a specific network. Of course, that has to be on a network. On the other hand, as we’ve talked about ICMP, ping sweep, we can help diagnose a network issue quickly and find what’s going on with the host. Even remote devices on different IPs can be accessed by sweeping ping.
Purpose of Ping Sweep
Ping sweep is used to gain various information over the host. It has the potential to address a range of IPs for live mapping. In regular pinging, we have echo request and echo-response functions. It’s a way of data request and gaining sufficient knowledge on a network device. It can also map a range of IPs. Echo request reveals information regarding the IP we ping. Local pinging directs via local DNS server and input has a round-trip time (RTT). But ping sweep uses ICMP echo request. It can send packets of data to reveal in-depth information about a host or range of hosts. Finding out live and dead Ips, detecting bad traffic and rogue network devices, and matching only permitted IPs on the network are a few results that can be documented by ping sweeping. Regular pinging can be done on console command on admin devices but ICMP echoing requires advanced software packages. Same reason they can be manipulated any way the admin wants to achieve live mapping a DHCP environment.
Generally, we can either conduct a Normal Ping Sweep or Flood Pinging. Once we have the target IP address of the host, we can ping that IP address and determine whether the host is alive or not. Once packets are received correctly, then we can confirm host stats. The data will help in conducting further work on the host. This is a normal ping sweep.
On the other hand, flood pinging is quite like a denial-of-service attack. It occurs when a website or host is flooded with lots of pings. The result of it is pretty serious. Regular legitimate users may not use the service or host at the time of flood pinging moment. Every website or victim network has a maximum capacity and when flood pinging crosses that limit, it jams the network and the host stops responding. Automated scripts or flood pinging software are used for this kind of experiment. Flood pinging is sometimes called a “Ping of Death” as it makes the host behave like a dead host. Flood pinging is mostly used for session hijacking.
Best tools for Ping Sweep
Since there are many tools to map Ping Sweep, we are only highlighting the best ones. They are simple to use and can perform all the advanced tasks easily that an admin may require. As ping sweep requires packages and special features, it is important to use tools. It saves time and the display systems in tolls are well thought out. Reveling and going through data becomes easier for anyone looking to find a situation of network or finding vulnerabilities. Our top pick consists of:
2. SolarWinds IP Address Manager (IPAM)
3. SolarWinds Engineer’s Toolset (ETS)
4. ManageEngine OpManager
5. Advanced IP Scanner
6. Paessler PRTG Network Monitor
SolarWinds IP Address Manager (IPAM)
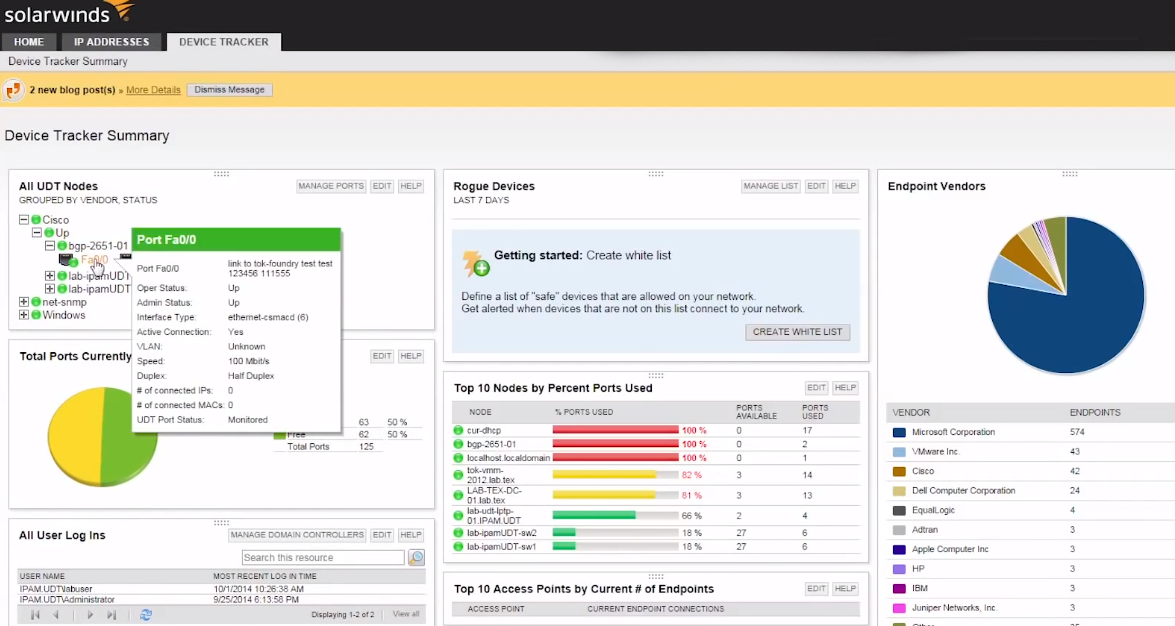
SolarWinds IP Address Manager (IPAM) is one of the best software solutions for ping sweep. A wide variety of functionalities can be achieved under a single package. DHCP, DNS, IP subnets and IP address can be managed simply by one software. It is possible for network admins to manage and configure DNS and DHCP services, troubleshoot IP-related problems with IPAM. IPAM is a standalone software solution that can be used on the system quickly without dependency on special hardware.
On the other hand, having duplicated or faulty IPs can be troublesome for network admins, IPAM can easily track these errors and let the admin guide toward fixing the issue. Simply defining the default gateway will get IPAM started on its task. Smart tracking and prompting notification errors are great add-ons with the app. It is also possible via IPAM to update IPV4 and IPV6 subnets with manual configuration. IPAM works together with SolarWinds Network Performance Monitor (NPM), Server, and Application Monitor (SAM) in a single console.
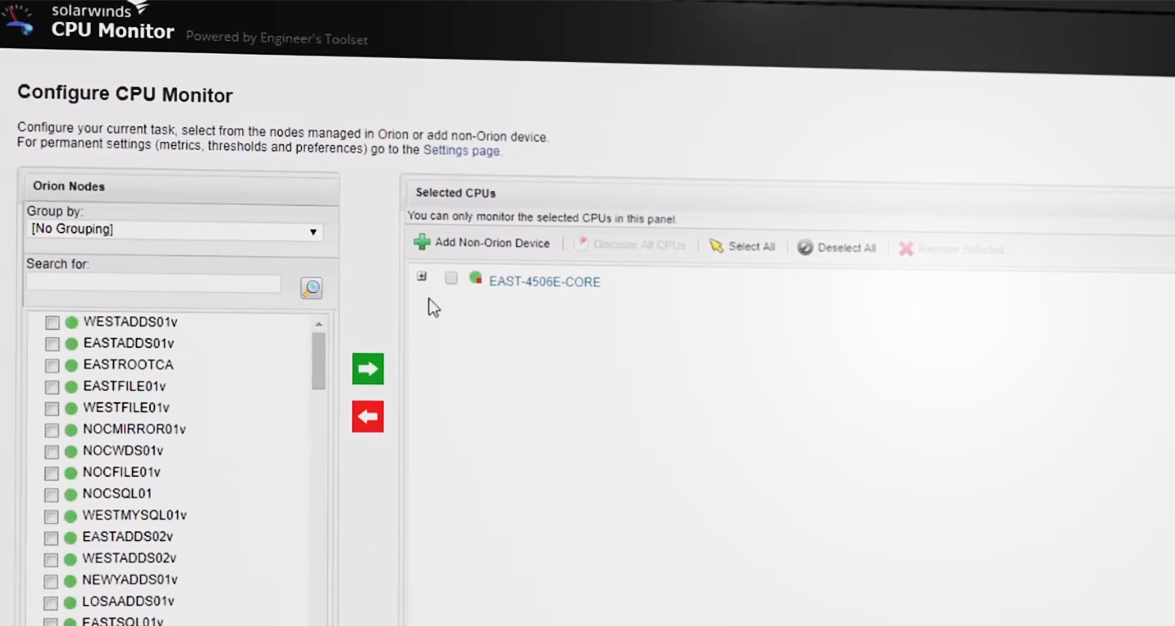
SolarWinds Engineer’s Toolset (ETS)
SolarWinds Engineer’s Toolset (ETS) has a list of interesting and essential tools at its disposal. Ping sweep is one of the primary ones amongst IP Address management, Switch Port Mapper, and 60 others. ETS scans IP addresses that are on use and which ones are free on the get-go. ETS can output data into a spreadsheet, Excel, HTML, TXT, and CSV format. Inputting a range of IP or subnet will provide ETS enough information to get the scan running with a ping sweep.
With this tool, we can separately ping sweep IPs that we only want to be categorized by the IPs currently in use, responding and non-responding. ETS is beginner-friendly means using it is very simple. Each portion of data is separated nicely and it’s good for the eyes when going through multiple data lists. ETS extracts data from the DHCP server and can compare results in any way the admin desire.
ManageEngine OpManager
ManageEngine OpManager is a great tool with visually stunning UI compared to the rest of our listings. According to the company data, more than 1 million IT Admins use ManageEngine OpManager and it has been their go-to tool for over 15 years. If pie charts, fancy notification buttons intrigue admins, it will be an easy pick with lots of built-in tools to perform several actions like ping sweep, collecting IP data. The ping monitor can easily track and send live notifications to admins which is great for putting up a fast solution.
ManageEngine OpManager is a reliable tool that can fetch hostname, response time, packet data amongst many others. The application can allocate tasks over the network, server, firewalls, applications, user logs, and local configurations. ManageEngine OpManager has a multi-level threshold for crucial performance monitoring with customizable dashboards that can be set up according to frequently used windows. ManageEngine OpManager can measure and monitor jitter, RTT with a quick-fix solution.
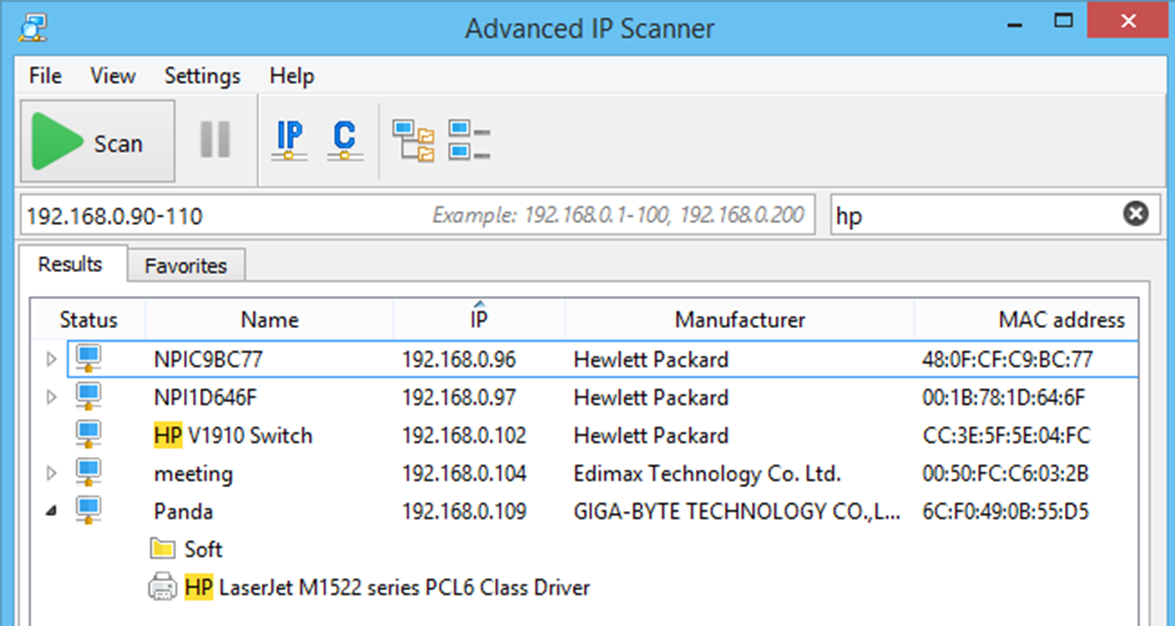
Advanced IP Scanner
Advanced IP Scanner works similarly as its name suggests and it is one of the simplest ones for ping sweep in our list. Not every admin is looking for fancy and additional features and a simple interface is the way to do it for most of them. To those who like to keep things simple, the Advanced IP Scanner is a breath of fresh air. The tool is a standalone product with no need for installation on a local machine and is trusted by over 30 million users.
Advanced IP Scanner is a free tool with simple functionality like ping sweep. Addressing a range of IP on its input will reveal information from ping sweep. Output data can be saved based on categories like hostname, RTT, MAC address, network vendor data, etc. It is recommended to use Remote Desktop Protocol (RDP) to get the best result while using the Advanced IP Scanner. Being a free tool, it can perform simple tasks to reveal the information we mentioned and that’s all of it. People looking for more advanced features have the option to choose anything else on this list.
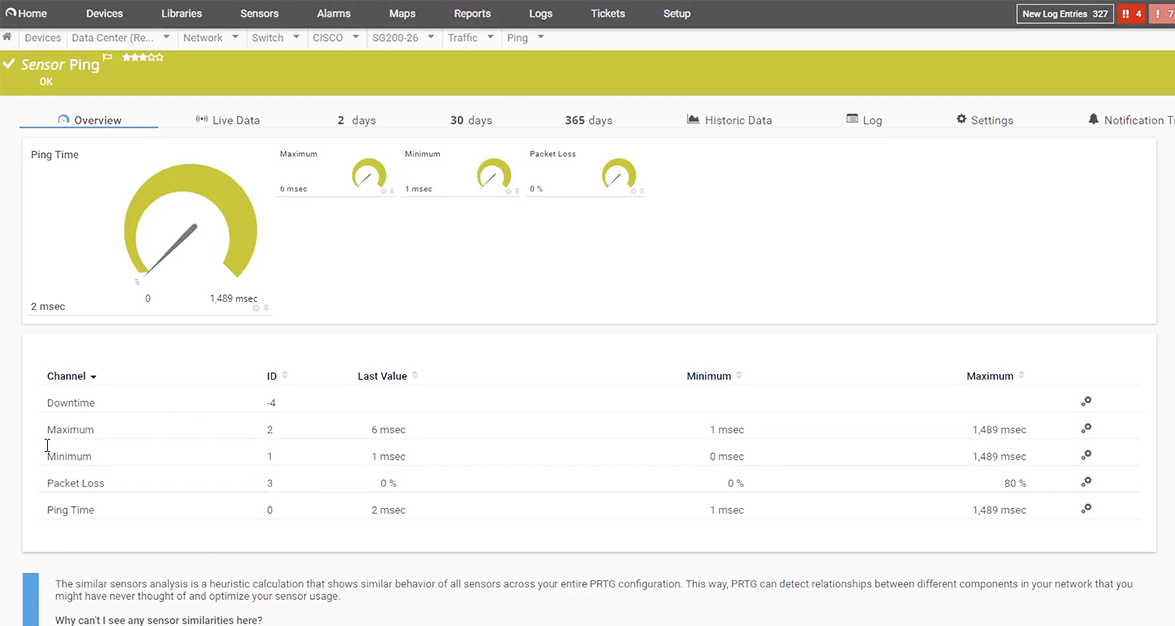
Paessler PRTG Network Monitor
Paessler PRTG Network Monitor is suitable to monitor an entire infrastructure flawlessly. PRTG doesn’t depend on an agent similar to Advanced IP Scanner, which means it can run as a standalone program without any installation on an actual system. SNMP or WMI protocols are used to talk to devices and get a range of IPs with PRTG. The app has built-in data sets that can be used in all situations removing the hassle for admins to prepare spreadsheets beforehand. With simple and smart charts that disclose IP down and upstate, known and unknown state conflicted or malicious IPs.
Using Paessler PRTG Network Monitor will allow admins to ping sweep real-time with the host state properly. They will contain enough data to take further action. PRTG has web service performance capabilities and logs whole system network devices in a register. This data can be used later for more ping sweep actions. Paessler PRTG Network Monitor can be used on regular computers and even as a cloud-based application. Subscription will allow admin up to 100 sensors to work with a ping sweep.
Choosing the right Ping Sweep tool
We listed a handful of the best ping sweep tools available to us. In fact, there are plenty. Mentioned options are trusted and used by numerous amounts of users and admins around the globe. Some people may still prefer command-line tools but today technologies became so advanced that we need as much data as we can gaze on. And for this, we need tools that are being constantly updated to meet the demand of users. Troubleshooting IP-related issues, DNS, DHCP, integrated management are few perks that come with ping sweep tools.