
How To Use Hydra with Burp Suite – Step-by-Step Guide
Overview The massive global community and security enthusiasts practice website password cracking regularly. Most of the time, it is to

Overview The massive global community and security enthusiasts practice website password cracking regularly. Most of the time, it is to

Hey all, in this walkthrough we will take billu box which is hosted on vulnhub.com and show you exactly how to
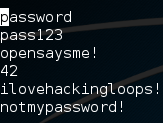
Welcome back my fellow hackers! Today we’re going to discuss the concept of brute force attacks by building our very

Welcome back everyone! This is the first in a new series we’re launching that will walk you through various capture the