The job market is fierce these days in just about every industry. Even though statisticians and economists have forecasted long term growth for the I.T. and security industries, it’s not as easy to find a job as you might think. After all, you can’t simply hope to earn a few entry level certifications and be instantly gratified and rewarded with a six figure security salary!
So, that begs the question: how on earth are you supposed to get your foot in the door? Well, it may not be as easy as you think. There are a lot of pitfalls and traps on the way to becoming a full-time penetration tester and security professional Today, we’re going to take a closer look at what it takes to succeed – but first, let’s look at some job market statistics.
Job Market Statistics
Just about everyone seems to be saying the same thing: there is a massive shortage of qualified and competent cybersecurity professionals. And this is a massive problem, because cyber attacks can cost organizations millions of dollars in damage, harm their brand, and cause a business to lose the trust of its customers.
In fact, Cybersecurity Ventures estimates that the globe will spend roughly 1 trillion dollars on cybersecurity within the next four years. And Benchmark Executive Search estimates that the shortage of qualified candidates will be as high as 1.5 million by 2019. To put things bluntly, the world desperately needs more security professionals, and there’s a lot of money flowing through this job market.
And according to Peninsula Press, there were approximately 209,000 cybersecurity jobs in 2015 that were vacant. Not surprisingly, they also estimated that the average pay increase between other I.T. professionals and cybersecurity professionals was about $12,000. CSO also reported that the cybersecurity job market is expected to grow by as much as 6 million by 2019.
No matter who you talk to, everyone seems to agree that not only is the cybersecurity job market expanding, but there is also a workforce gap that leaves many positions unfilled. Gee, it’s starting to sound pretty darn easy to get a cybersecurity job, doesn’t it? After all, if the demand is so high, you could easily get your foot in the door with a degree, a few years of experience, and even a few security-centric certifications under your belt, right?
Well, as many have discovered, it’s not as easy as it sounds to land a good security job, and I’ll tell you why.
Security Is Not an Entry Level Job (Usually)
While it’s true that having the right qualifications certainly help, you need to understand that a lot of cybersecurity jobs are high-octane, stressful, gargantuan commitments of your time, energy, and life. Sure, there are entry level jobs (but they’re pretty rare), mid-range jobs, and even expert level positions. But you must understand that, on the whole, cybersecurity isn’t an entry level trade or profession.
Think about it. Would a business really want to put their faith, trust, and future of their company in the hands of a green young intern who doesn’t even know the difference between active and passive FTP? Not a chance! The failure to secure a single security flaw or the failure to properly secure network access could have massive repercussions that cost the business time, money, headaches, and could damage its future earnings potential.
Furthermore, there is a trust factor at play as well. It’s quite a professionally intimate act to give a ‘new guy’ the keys to your digital kingdom. We live in the information age, and one wrong keystroke from an incompetent professional could spell disaster for the business. Okay, perhaps I’m blowing things out of proportion a little, but I think you see my point.
Furthermore, to succeed in a security-centric role, you’re going to need to know a lot more than simply how to secure a system. You’re going to need to have a solid understanding of how computer systems and networks operate, a proven track record of professionalism and competency, and the skills to back it up. If you’re fresh out of college or achieved the almighty Security+ certification after 1 year at a help desk, don’t expect to land a great cybersecurity job.
But what about the folks with a lot of experience and a few entry level security certifications? Should they expect to find a security job with a little more ease? My feelings are that entry level security certifications help you stand out from the crowd, and serve as a way for you to get your foot in the door. Then, after you finally break through and have a few years of experience in a low to mid-range security position, you can start to chase the real security jobs. However, some people get stuck in their current position.
Getting Stuck in Your Current Position
A lot of people find that after serving their business faithfully and diligently for a long period of time, it’s awfully hard to transition to a security role within the same firm. It’s pretty easy to get pigeon-holed, especially if you’re so good at your job that you’re nearly irreplaceable. I’ve heard of some guys that have worked with dying technologies and systems that are on their way out for years – decades even – that can’t break free from the inescapable black hole of their current position.
The case may be that they’re working with a system that’s so old it isn’t taught in school anymore, making it even more imperative to the company to keep that I.T. professional in their current role. For instance, COBOL and Fortran have been dying for decades now, though there are a few businesses that still use those technologies (for whatever reason). Some companies fail to allocate enough resources to their I.T. systems, and use older technologies such as antiquated database systems.
Their philosophy is ‘if it ain’t broke, don’t fix it,’ and fail to see the value in updating their staff, training, and hardware. If that’s the case for you, things look pretty bleak. Chances are they’re going to bring in new blood to fill vacant security positions since replacing your knowledge and skillset is extremely unlikely. I can really only see three possibilities if I were stuck in that situation, and none are very attractive.
The first option is to try to wait it out, either waiting for the old system to finally die out or be replaced, freeing you from your station. Though it’s unlikely, you can still try to pivot towards a security position within the same firm. But the grim reality is that your firm may never give you the opportunity to spread your wings and build a cybersecurity career, which brings us to the second option – and it’s pretty darn risky.
The second option is to seek employment elsewhere, but it’s problematic as well. First of all, there’s issues of loyalty and the feeling that you’re doing your business an injustice. It might even be ethically irresponsible to seek employment elsewhere behind your employer’s back. What if they caught wind of your job hunt, and decided to drop you like a hot potato? What if you quit your job first out of moral principles, but then the job hunt goes poorly?
Lastly, there is a third option. You can simply bide your time and seek to improve your security skills. For example, you can always get more training, or seek higher level certifications. If you’ve already got a few entry level security certifications under your belt and have a background in networking, why not try for a more advanced certification like the CCNP Security exams? Doing so would make you a lot more attractive to employers, and even put you in position to undertake the immense task of sitting the CCIE Security exam years down the road. Furthermore, vendor certifications will make you more attractive to a channel partner or consulting firm (as we’ll discuss next).
In summary, I can really only see three possibilities if you’re having trouble obtaining a security position at your current firm:
-
Keep trying to get your foot in the door in the security department of your current employer
-
Seek a security career elsewhere
-
Bide your time and enhance your skills and qualifications
The Wide World of Consulting
I think one of the best places a young, green, wanna-be security professional start is in a consulting firm – and I speak from personal experience. When I started, I had a degree, a handful of entry level certifications, and some pretty average experience (maybe I’m underselling myself, but it wasn’t exactly jaw-droppingly impressive experience).
Luckily, I found employment with a Cisco channel-partner. If you don’t know how channel partner programs work with hardware vendors, I won’t get into specific details. But I will paint a fairly accurate picture as briefly as possible. Basically, the owner of the business (which shall go unnamed, though I can tell you they partnered with several different hardware vendors) entered into an agreement with the hardware manufacturer.
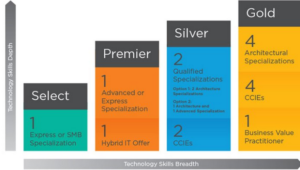
In these situations, the channel partner is essentially a reseller. The hardware vendor is happy because the channel partner is selling their equipment. And the channel partner can sometimes mark up the cost (depending on the sales program, vendor, and their legal agreements) and add a service and installation charge. It’s a win-win, and there is an endless number of sales opportunities when new lines of products come out, and plenty of different kickback programs as well. One reason that consulting firms and channel partners love employees with certifications (apart from the obvious benefit of validating skills and knowledge) is because they increase their ‘partner level.’
What’s this have to do with security and penetration testing, you ask? I’ll tell you. Working for a channel-partner means you’re going to have a lot more opportunities to be exposed to hardware appliances, technologies, and applications than you would working in a firm where I.T. plays a supportive or ancillary role to the company. Sometimes, channel partners will even incentive their employees to obtain higher level certifications, and may even help pay for or offset the cost of training and certification exams.
There were so many different hardware appliances flowing through that consulting firm that I got exposure to technologies that may not have have even been applicable in other roles. For example, I had the opportunity (well, some say opportunity, and some say pain in the neck – it really depends on the quality of the hardware appliances) to configure just about every make and model of business-class firewalls under the sun (Cisco ASA’s, Watchguard, Fortigate, the list goes on…). I would troubleshoot VPNs, firewalls, and security technologies until my eyes nearly bled, and that kind of real world experience is invaluable for anyone pursuing a career in cybersecurity.
For me, those opportunities weren’t really hard to come by. I had a great chance to add more tools to my troubleshooting toolbelt, such as running various network scans, testing wireless networks for vulnerabilities, understanding network architecture, running packet captures to verify different traffic types were permitted/denied on different firewall interfaces, the list goes on.
Can I claim to be a CCIE or penetration tester extraordinaire? Perhaps not, but I definitely had the valuable opportunity and experience of running various security audits, and I had the chance to flex my security muscles. I also had the opportunity to install, configure, and maintain IPS and IDS devices, and react to various threats and attacks in real time.
So, my advice would be to try to get your foot in the door at a consulting firm, especially if you’re just starting out. If you’ve already got decades of experience, transitioning to a consulting firm may still be a valid option. Bear in mind, however, that you’ll need to consider if it’s financially feasible, and whether or not you’re going to take a pay cut.
After all, who do you think stands a better chance of getting a job offer for a security position? Someone who’s worked with security hardware and technologies for years with a consulting firm, or someone who doesn’t have real-world experience using security technologies at their current firm (despite training, certifications, and initiative)?
Take Every Opportunity and Training Advantage
Certification exams are big business, and a vendor’s certification program is an integral part of their overall business. After all, what good is the latest and greatest software or hardware technology if no one can configure and implement the stinkin’ thing? But the exams are expensive. Even the entry level exams can cost a few hundred dollars each, and if you fail, sorry Charlie – you lose your money!
For that reason, I would offer the advice to never miss out on free training. If your employer has an incentive program to help offset the cost of certifications, don’t sit there twiddling your thumbs. But take things one step further, and be as proactive as possible. It should come as no surprise that if you want to be a penetration tester, you’re going to need to learn how use penetration tools.
The background knowledge and skills learned in entry level security exams are just the beginning – merely foundational knowledge. Nevertheless, you can start building a knowledge of penetration tools absolutely free. My advice would be to download and install Kali Linux, because it’s free and chock full of penetration testing tools. If you’re Linux skills are lacking, start learning basic Linux commands and get comfortable working from the command line.
You’d be surprised how simple some of the tools are to use once you get the hang of it.
Final Thoughts
I don’t really think there is any magic solution to breaking into the world of penetration testing. The jobs are out there, clearly, but you need to hold the right qualifications, experience, and skillsets. It just takes a lot of hard work, time, energy, commitment, and discipline. I honestly think that if you’re an intelligent human being who really applies yourself (i.e. genuinely studies, puts in the time and hard work, etc.) that you can succeed in becoming a penetration tester.
Last but not least, I’d like to advise you to start off in a consulting role if at all possible. I know that might not be possible for some of you, especially if you don’t have a degree, certifications, or you haven’t paid your dues at a help desk. Still, it’s harder to get pigeon-holed in a consulting environment.
If you have any questions, comments, or concerns, feel free to post a comment below to let your voice be heard. Last but not least, as with any other career advice, remember that your mileage may vary.

