Cyber range is a virtual set up that mimics the real-world infrastructure of an IT industry to practice the Cybersecurity skills in a live but controlled environment. It gives the feel of real networks, systems, tools, and applications to the Cybersecurity professionals to gain hands-on experience without affecting the operational infrastructure of the organization. The concept of cyber ranges is new but it is gaining popularity among defense and corporate sectors mainly because of the high-level practice environments and the capacity to train a large number of professionals at the same time. In this article, we explain different types of Cyber range technologies, the essential capabilities of a true Cyber range service, and different Cyber range use cases.
CYBER RANGE TECHNOLOGIES
Cyber range technologies can broadly be classified into traditional and advanced ranges.
Traditional Cyber Ranges:
The traditional Cyber ranges are also known as the conventional Cyber ranges. Although the concept of virtualization is also involved in traditional Cyber ranges, they are mainly based on the physical hardware, networks, applications, and tools to exercise different Cyber-attack scenarios. The traditional Cyber ranges are helpful in finding the security flaws in a dedicated IT infrastructure. The experts are able to find the weaknesses and strengths of a specific infrastructure to further enhance the security posture of the respective organizations.
Advanced Cyber Ranges:
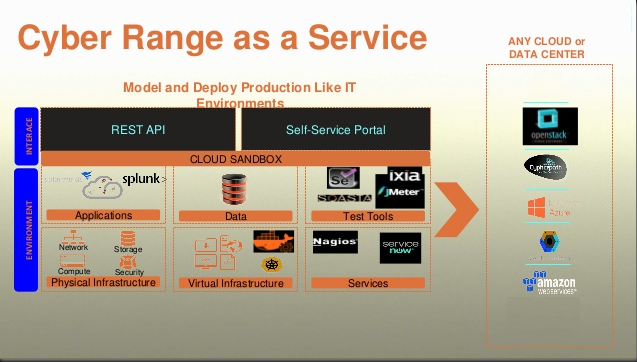
Although the conventional Cyber ranges are helpful in finding the security gaps within an IT infrastructure, they are not very helpful in situations like defensive or proactive modification in the attack scenarios, such as responding to the attack and remediating the damages. For that purpose, we have advanced level Cyber ranges based on Cloud services. The Cloud virtualization of Cyber ranges not only enhances the range of services but also reduces the extra cost of buying the physical hardware just like in the case of traditional Cyber ranges.
Cyber range technologies can be availed as a service or as a platform. The service may include a physical Cyber range at the vicinity of the Cyber range service provider or a remotely Cyber range accessible through the online setup. The Cyber range as a platform is the on-premise Cyber range deployed at the organization. The on-premise Cyber range is an expensive setup that emulates the organization’s IT infrastructure to carry out Cybersecurity training, testing, and development tasks.
CYBER RANGE FEATURES
The Cyber range features are different functions supported by a Cyber range. Beyond technology, it is the features or functions that distinguish a high-level Cyber range from an ordinary one. A brief overview of some important Cyber range characteristics is presented below.
Scalability:
As the technology evolves, the number and nature of Cyber-attacks change with time. Therefore, Cyber range must be capable of incorporating more resources as per requirement or modification in the IT infrastructure of an organization.
Accessibility:
Accessibility is another important feature of a Cyber range. As discussed above, there are two main categories of Cyber ranges that can be accessed as a service or platform. The Cyber range accessibility as a remote service must be secure. The connections between the Cyber range and the users must be free from disruption or downtime issues during the access time. The Cyber range provider must inform the users about the unavailability of the Cyber range for tasks like maintenance or up-gradation of the services.
Orchestration:
The orchestration features make a Cyber range more efficient by automatically handling the configuration and management tasks. In computing technology, orchestration is the automation of configurations, management, and coordination between computing machines, tools, applications, and related services. In the Cyber range, the concept of orchestration is related to the automated configuration of virtual machines, components, systems, and any other hardware that is used in the training or testing environments. A Cyber range must be able to automatically manage the scenarios, virtual setups, and coordinate between the hardware and software used in the Cyber range operations.
Simulations:
While simulation is present in almost every facility, it is the level of simulation that decides the effectiveness of a Cyber range. Some Cyber ranges are capable to simulate only sandboxed technologies while others are able to simulate internet services like social media platforms as well. The attack simulations, benign activities, and malicious traffic emulations are different metrics that tell us the range and capability of a Cyber range to provide a learning environment to the users.
Monitoring and Data Collection:
A well-equipped Cyber range offers live monitoring of the ongoing Cyber range operations and collection of related data. The data can be a user interaction record with the Cyber range systems, log files, attack details, and information about the successful and failed Cyber attempts of each Cyber range participant.
Evaluation and Reporting:
The scoring and reporting system in a Cyber range helps the organizations in evaluating the performance and capabilities of the users. Some Cyber ranges offer only fail/pass scoring system based on the failed and successful attempts of the participants. The advanced-level Cyber ranges monitor each activity of the users and rate them on the basis of different parameters, such as interaction with the systems, handling the tools, time consumption over a task, individual efforts, team determinations, completion of tasks, and achievement of mission objectives.
CYBER RANGE USE CASES
The Cyber range evolution not only changed the dynamics of the concept but also its uses. The following are some frequent uses of Cyber ranges available to a variety of users like the corporate sector, national defense institutes, security professionals, educators, researchers, and students.
Security Assessment
This is probably the very basic and fundamental use of any Cyber range. Different attack simulations are created to evaluate the security of a system, network, or infrastructure as a pre-deployment test or an ongoing security assessment practice.
Skills Assessment
Finding the right talent for a sensitive job is one of the difficult tasks in Cybersecurity. The traditional ways of assessing the capabilities of professionals involve the written exams, interview questions, and scrutiny of educational records and certifications. The Cyber ranges provide a more advanced way of finding the proficiency of the persons by testing their hands-on skills and experience required by the organizations.
Skills Development
With the growing number of Cyber-attacks and data breaches, the well-trained staff has become obligatory for the organizations. Cyber range training sessions are conducted in this regard to train non-technical employees and enhance the skills of Cybersecurity professionals.
Joint Cyber Exercises
International level Cybersecurity events and competitions are organized with the help of Cyber ranges to help people from different countries collaborate and share the experience with each other.
Research and Development
Many Cybersecurity research and development projects originate from Cyber ranges. The security experts use the Cyber ranges to explore different types of malware and zero-days, vulnerability detection methods, and mitigation processes.
CONCLUSION
The term ‘Cyber range’ has gained a lot of hype and popularity over the years. Security experts are predicting the Cyber ranges as the future training grounds for organizations and security professionals. However, there are certain problems that need to be addressed to fully embrace the evolving concept of Cyber Ranges. For example, the traditional Cyber range technology is quite expensive for small businesses and individuals. Not many organizations can afford to have their own Cyber range services offered as the on-premises facilities. The remote Cyber range as a service is low cost but it requires a lot of safety to provide an uninterrupted and secure environment to the users. There is no global compliance or standard for Cyber ranges to operate in the Cyber industry.