Despite spending millions on cyber-security, organizations face data loss and breaches every year. There can be many reasons for this. One obvious reason is not having enough or right defenses against the evolving cyber-threats. Organizations need to understand the gaps in their defense strategies to overcome cyber-threats. But how do organizations know if they have done enough against the existing and evolving cyber-risks? There must be some reference models to compare the deployed cyber-security defenses with the recommended ones by the trusted reference models. These reference models are often termed as cyber-security capability maturity models. These maturity models assess the organizations’ efforts to deal with the undesired cyber-security challenges in various domains including risk, threat and vulnerabilities, incident response, access management, identity management, and operations continuity. The organizations can compare their current cyber-security capabilities with the baseline cyber-security measures defined in these models to cover gaps and enhance their efficacy. There are various cyber-security capability maturity models that organizations can use as references. Following is a brief overview of the three most referred and trusted models that can greatly improve the security posture of any organization dealing with cyber-security challenges.
NIST Cyber Security Framework (NIST CSF)
The National Institute of Standards and Technology (NIST) published the Cyber-Security Framework (CSF) in 2014. The initial goal of the framework was to provide guidelines for critical infrastructure cyber-security. Today, the framework is used as a cyber-security reference model by many organizations, improving their overall security posture by comparing their existing cyber-security plans with the NIST CSF recommendations. There is no need for organizations to replace their existing cyber-security policies with the CSF. The organizations can overlay the framework with their current approach to identify security gaps in their existing strategies.
NIST CSF Model Architecture
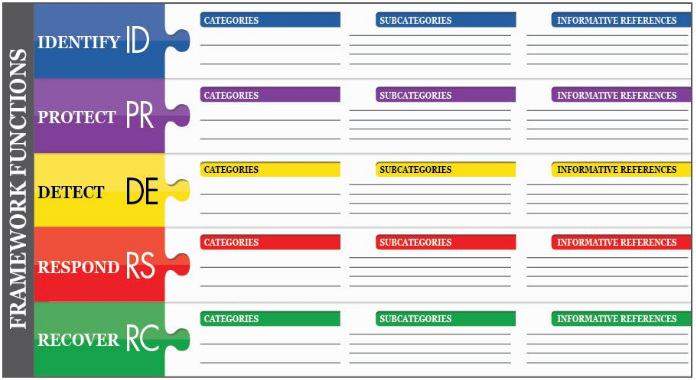
The NIST CSF can be divided into the following elements.
1) Functions
There are five core functions defined by the NIST Cyber Security Framework. These functions act as guidelines for organizations to follow in order to address cyber-security threats, manage risks, make appropriate decisions, and learn from the past cyber-security activities. The functions are defined below.
- Identify
Every organization has business goals. The organizations work on different strategies to accomplish their goals. However, there can be some risks involved in the strategies. The Identify element helps organizations in prioritizing the risk management strategies aligned with business requirements. The function helps organizations in understanding the requirements for better cyber-security risk management for data, assets, systems, people, and organizational capabilities. The main categories influenced by Identify function include Risk Assessment; Risk Management; Governance; Business Environment; and Asset Management Strategies.
- Protect
The protect function helps organizations in developing and implementing the appropriate safeguards so that the critical services of an organization should not be disturbed by adversaries.
- Detect
Following the Detect function approach, the organizations can better develop and implement the functions like anomalies and events, continuous monitoring, and detection processes in order to timely detect the cyber-security events.
- Respond
The function guides the organizations about how to give an appropriate response to the findings in Detect function. Analysis; Response planning; Communication; Mitigation; and Improvements are the main categories influenced by Respond function.
- Recover
The last function is the Recover function that shows organizations how to develop and implement appropriate activities to maintain/restore the services and functions that are halted by any cyber-security incident.
2) Categories
Categories are outcomes of particular activities performed in the aforementioned functions. Asset management; Detection process; and Risk management are few example Categories of CSF functions.
3) Sub-Categories
Sub-categories are subdivisions of categories into specific outcomes of technical/management activities. For example, the detection category can have a sub-category like this: “detection system notifications are investigated”.
4) Framework Implementation Tiers
NIST CSF Tiers are the metrics showing the organization’s view about cyber-security risks and strategies in place to manage the risks. There are four CSF Tiers listed below.
- Partial
- Risk-Informed
- Repeatable
- Adaptive
The Partial is the lowest Tier in CSF framework while Adaptive is the highest. Risk Management Process; Integrated Risk Management Program; and External Participation are the core Tier elements. For example; Risk Management Process in Partial Tier means there is no formalized risk management process and organizations manage risk ad hoc or reactive way. Similarly, the Integrated Risk Management Program in Adaptive Tier means the organizations are using the risk-informed policies, procedures, and processes to manage the potential cyber-security risks.
Reference: https://www.nist.gov/system/files/documents/2018/05/14/framework_v1.1_with_markup.pdf
MITRE ATT&CK Framework
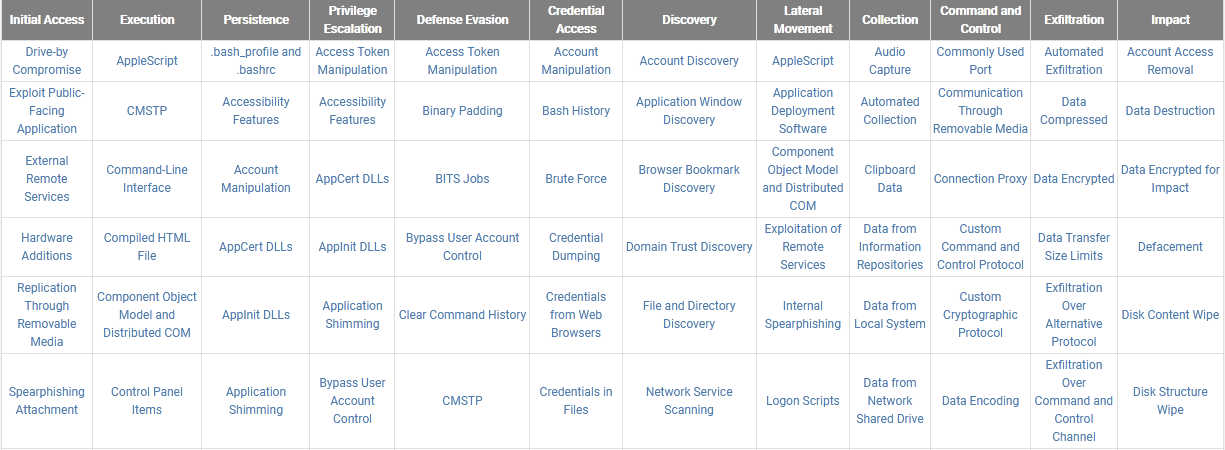
MITRE ATT&CK framework is perhaps the most pertinent cyber-security reference model. The ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge. The tactics and techniques show why and how adversaries can compromise their targets. The common knowledge represents the procedures adopted by the adversaries while performing attacks. The overall concept of MITRE ATT&CK framework is to make organizations aware of different techniques the attackers can use to compromise their cyber-security. Organizations can improve their cyber-defense system by comparing their cyber-security defense with the attack simulations covered by the ATT&CK framework.
ATT&CK Model Architecture
The main objective of the ATT&CK model is to make people aware of tactics and techniques that can be used to compromise the organizations. The summary of these tactics and techniques is displayed in a matrix (tabular) format. The tactics are displayed at the top while attack techniques are mentioned under each tactics column. Currently, there are following attack tactics mentioned in the ATT&CK matrix.
(From Left to Right)
1) Initial Access
2) Execution
3) Persistence
4) Privilege Escalation
5) Defense Evasion
6) Credential Access
7) Discovery
8) Lateral Movement
9) Collection
10) Command and Control
11) Exfiltration
12) Impact (The impact of aforementioned tactics and techniques)
Each tactic has one or more attack techniques that can be adopted by an attacker to compromise the targets. For example, the Privilege Escalation tactic column shows Access Token Manipulation, Application Shimming, Memory Injection, Hooking, and several other techniques that an attacker can apply in an attempt to escalate privileges. From a defense point of view, organizations can review the ATT&CK matrix to test their cyber-defense against documented attack techniques to enhance their security posture.
Reference: https://attack.mitre.org/
Cybersecurity Capability Maturity Model (C2M2)
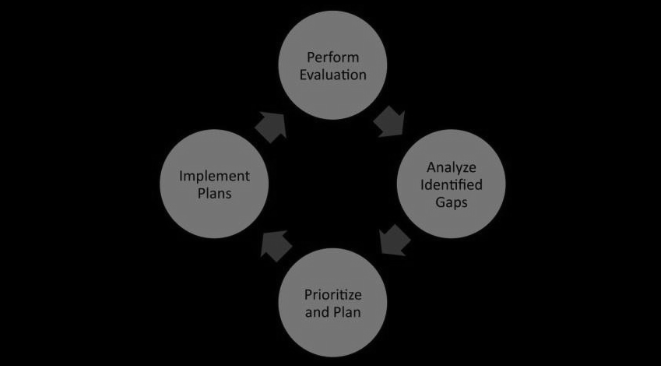
C2M2 is another credible cyber-security framework that can be used to benchmark the cyber-security capabilities of organizations. The main objective of C2M2 is to evaluate the cyber-security posture of organizations in terms of policies, processes, and procedures. Organizations can evaluate themselves against the model to identify cyber-security gaps. The organizations can then define their preferences to address the identified gaps. The following figure describes the recommended approach for using the C2M2 model.
C2M2 Model Architecture
C2M2 evaluates the organization’s cyber-security capabilities in 10 different domains. The desired results within a domain are termed as ‘objectives’. The metrics used to evaluate the cyber-security practices of organizations are called Maturity Indicator Levels (MILs).
C2M2 Domains
C2M2 currently covers the following cyber-security domains.
- Risk Management
- Identity and Access Management
- Cyber-security Program Management
- Threat and Vulnerability Management
- Workforce Management
- Asset, Change, and Configuration Management
- Situational Awareness
- Event and Incident Response, Continuity of Operations
- Information Sharing and Communications
- Supply Chain and External Dependencies Management
Maturity Indicator Levels (MILs)
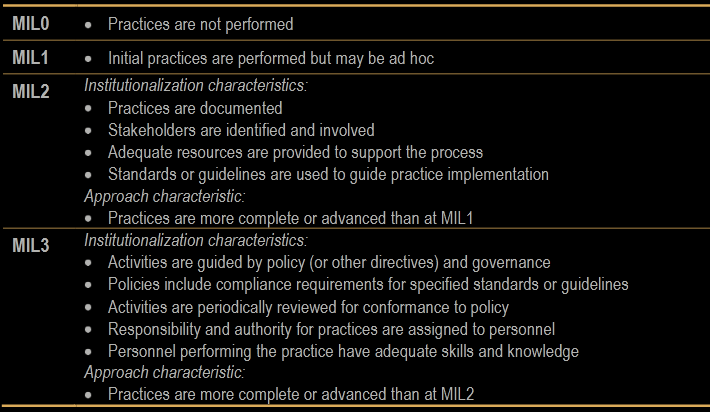
There are four Maturity Indicator Levels defined by C2M2 to measure the cyber-security approach (approach progression) and practices (institutionalization approach) followed by organizations. These are MIL0; MIL1; MIL2; and MIL3. MILs are applied independently to each domain to ensure the thorough evaluation of organizations for each domain. The following figure shows a summary of MILs characteristics.
Reference: https://www.energy.gov/sites/prod/files/2014/03/f13/C2M2-v1-1_cor.pdf
Conclusion
There are many cyber-security reference models available to evaluate the cyber-security maturity level in an organization. Organizations can follow these reference models to identify gaps, prioritize the risks, and make plans to rectify the cyber-threats.