CyberScan is an open source network penetration testing toolkit that can perform various forensics and network scanning tasks, such as data packet analysis, packet decoding, pinging networks, ports scanning, and gathering geographical data for a given IP address. CyberScan is capable of sending, capturing, and decoding data packets. The toolkit can decode Ethernet, IP, TCP, UPD, and ICMP headers. The decoded packets can give valuable insight about the network. The same packets can also be forged to launch different types of network attacks. The toolkit can perform different types of ping operations, such as ARP, ICMP, TCP, and UDP ping. The ARP pinging is the fastest way of finding the live hosts in the network. Port scanning is another utility added in CyberScan’s arsenal to scan either all or specific range of ports of target hosts. The IP-to-Geolocation feature of CyberScan gives detailed geographical insights about the target.
CyberScan Installation
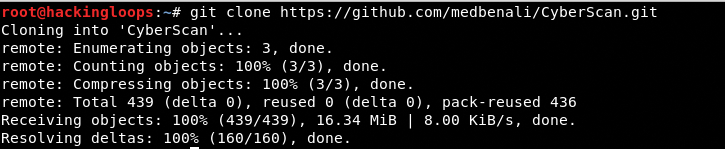
CyberScan is an open source, Python toolkit that is supported by all major operating systems including Windows (XP/7/8/8.1/10), Linux/GNU, and MacOSX. There are no defined pre-requisites for CyberScan. The toolkit can be cloned from Github using the following command.
git clone https://github.com/medbenali/CyberScan.git
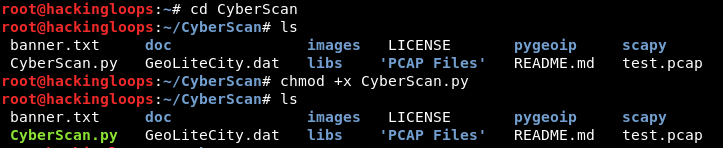
After downloading the source code, navigate to the toolkit’s directory and change file permission for CyberScan.py file using the following commands.
cd CyberScan chmod +x CyberScan.py
How CyberScan Works
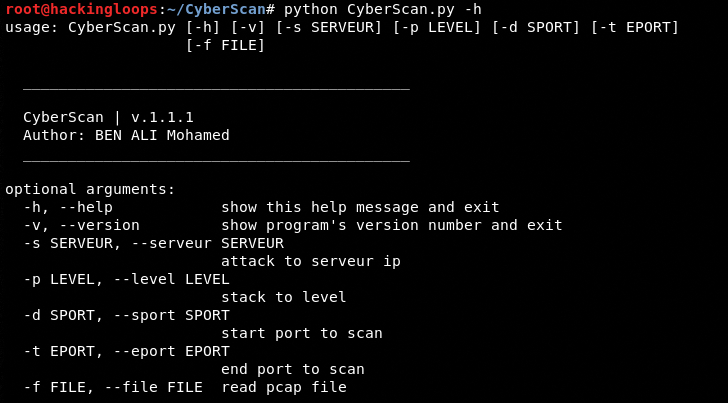
The following help command shows all the mandatory and optional arguments accepted by CyberScan.
python CyberScan.py –h
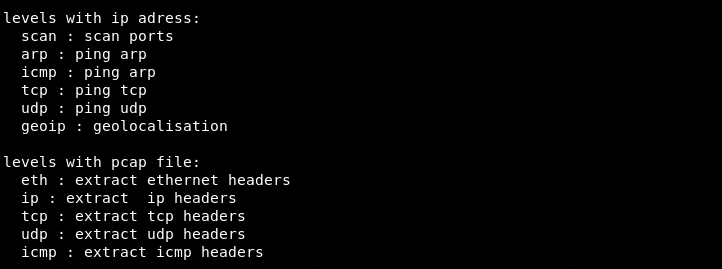
CyberScan has defined two sets of protocols for IP and packet capturing operations. The scan,arp,icmp,tcp,udp, and geoip protocols can be used in IP Address related operations, whereas the eth, ip, icmp, tcp, and udp can be used in packet capturing and analysis tasks.
Network Ping Operation
As mentioned earlier, CyberScan can perform different types of ping operations like ARP, TCP, UDP, and ICMP. The format is depicted in the following command.
python CyberScan.py –s <IP Address range> -p <protocol>
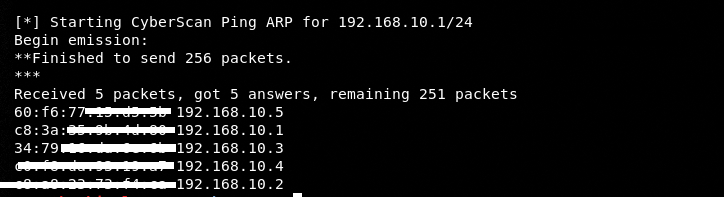
The <IP Address range> field can be replaced with the desired IP address range and the <protocol> with ARP,TCP, UDP, or ICMP protocol. For instance, we can look for live hosts in our local IP address range (192.168.10.1/24) using the ARP protocol in the following format.
python CyberScan.py –s 192.168.10.1/24 -p ARP
In the above command, /24 means the first 24 bits (192.168.10) represent the network address while the last 8 bits (1-254) represents the hosts address. The toolkit searches for the live hosts in the given range and presents the results in the following format.
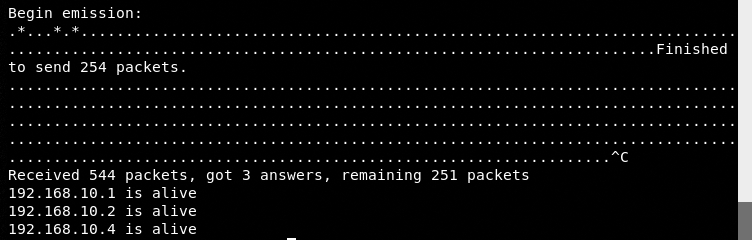
The TCP, ICMP, and UDP operations are considerably slower as compared to the ARP operation. We can use the ICMP protocol in the following format to find the live hosts in the network.
python CyberScan.py –s 192.168.10.1-254 -p icmp
The results are displayed in the following format.
Network Scan Operation
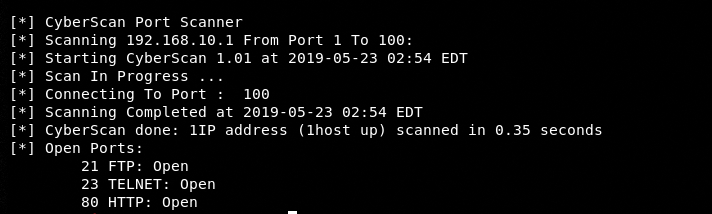
The network scan operation includes port scanning of the target hosts in the network. We can set an optional range to limit the port scanning operation. For instance, we can scan a range of ports between 1 and 100 for our target IP address 192.168.10.1 using the following command.
python CyberScan.py –s 192.168.10.1 –p scan –d 1 –t 100
In the above command, -p represents the scan operation, -d is the starting range of the desired ports to be scanned, and –t represents the end range. The results fetched by the toolkit are displayed in the following format.
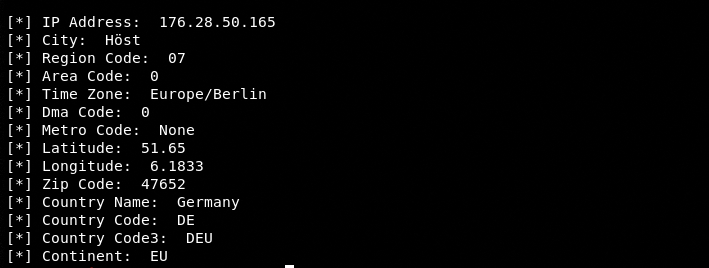
Geo-location Data Analysis
Geo-location data representation for the given IP address is another useful feature of CyberScan. The following command can be used to fetch valuable geo-location data for the target IP address.
python CyberScan.py –s <target ip address here> -p geoip
Data Packet Analysis
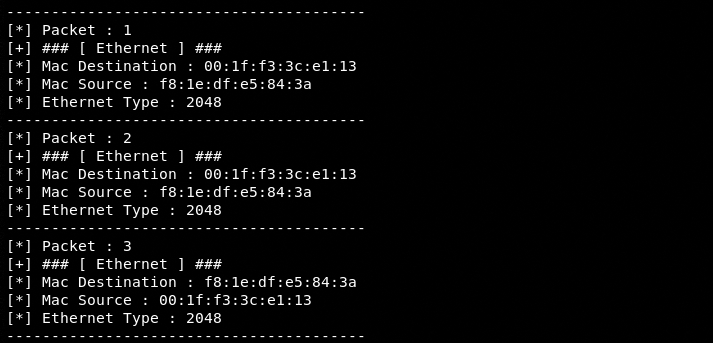
Data packet analysis is probably one of the most important features of CyberScan toolkit. The toolkit makes use of the test.pcap file included in the source code to capture and analyze data packets. CyberScan can decode Ethernet, TCP, UDP, IP, and ICMP headers of the captured packets. For instance, the Ethernet headers of the packets can be decoded using the following command.
python CyberScan.py –f test.pcap –p eth
Here –f represents the file to be read. In this case it is test.pcap file. The eth represents the Ethernet protocol. The results can be seen in the following screenshot.
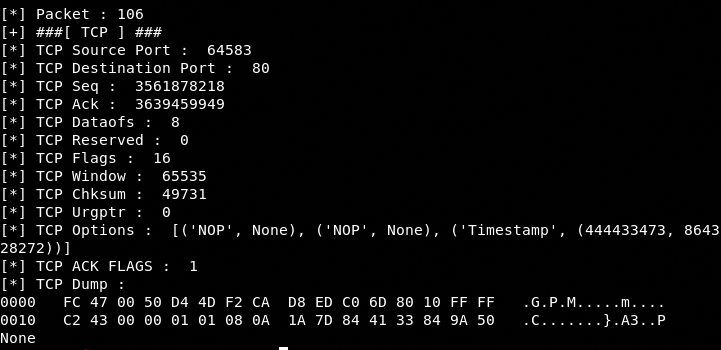
Similarly, we can look up for TCP headers using the following command.
python CyberScan.py –f test.pcap –p tcp
Summary
CyberScan is a decent network scanning and forensics toolkit. The packet capturing feature not only helps in unfolding the valuable network information by decoding the packets, but it also helps in offensive security measures.