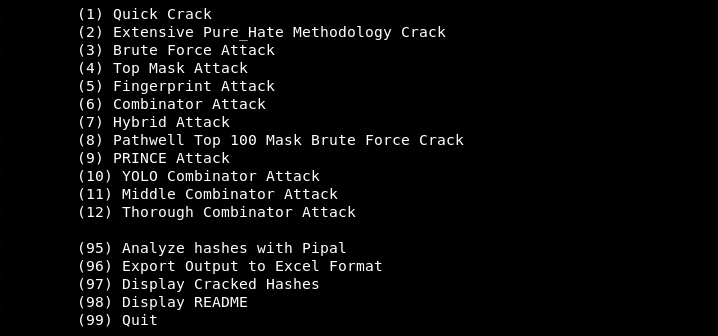
Hate_Crack is an optimization tool that automates the hash cracking processes followed by the Hashcat tool. Hashcat is an advanced password recovery tool that can crack over 200 highly-optimized hashing algorithms. Hate_Crack automates the Hashcat methodologies by providing the following modes of attacks.
Quick Crack
Quick crack is one of the fastest attack modes available in Hate_Crack. In quick crack mode, Hate_Crack performs the dictionary attack by utilizing all the available wordlists. The path to available wordlists is configured during the Hate_Crack setup process.
Extensive Pure-Hate Methodology
The extensive pure-hate methodology allows the attacker to run several attacks including brute-force, dictionary, top mask, fingerprint, combinator, and hybrid attacks.
Prince attack, YOLO Combinator, Middle Combinator, and Thorough Combinator are the other available attack modes in the tool.
Hate_Crack Installation
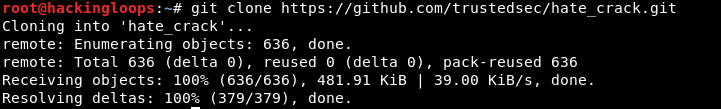
Before installing Hate_Crack, install the latest version of Hashcat. You can go through our Hashcat tutorial to follow the Hashcat installation steps. Once Hashcat is up and running, clone the Hate_Crack tool by executing the following command.
git clone https://github.com/trustedsec/hate_crack.git
Navigate to the tool’s directory and change execution permission for the hate_crack.py file.
cd hate_crack chmod +x hate_crack.py
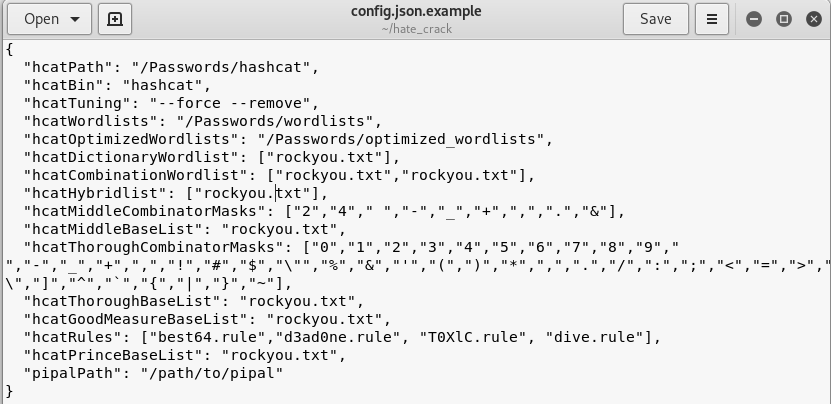
The next step is to configure the Hashcat binary and wordlists files paths in config.json file. The Hate_Crack directory has an example configuration file (i-e config.json.example) as shown below.
Create a config.json file and paste the content from config.json.example in config.json file. Replace the example Hashcat binary and wordlists files path with the system’s files path. The path to any file can be found by using the locate command. For example, we can find the Hashcat path using the following command.
locate hashcat
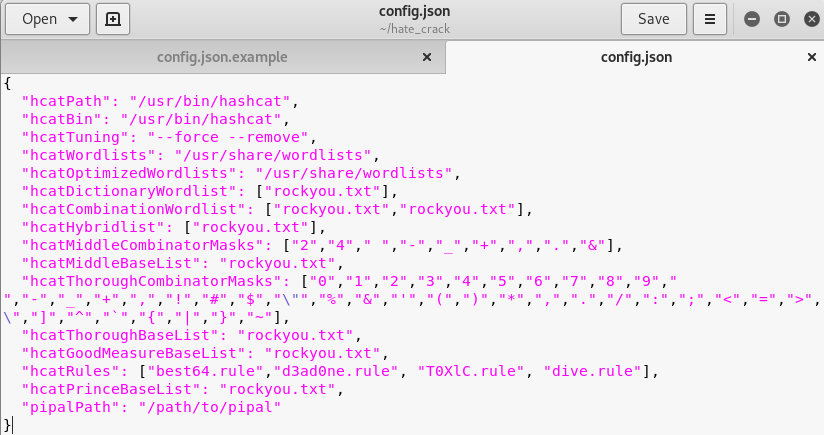
The following screenshot shows the config.json file configured according to our system’s Hashcat binary and wordlists files paths.
Note: If we don’t create config.json file, Hate_Crack automatically creates one with example data during the initial execution of the tool.
How Hate_Crack Works?
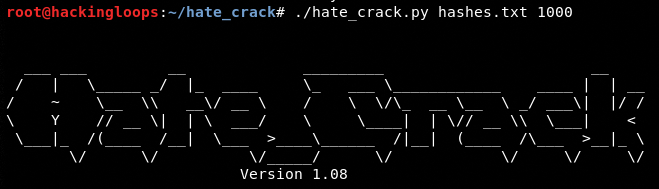
The following command starts the Hate_Crack tool with all the available attack modes.
./hate_crack.py <hash_file> <hash_type>
The <hash_file> needs to be manually set up in the tool’s directory. The <hash_type> is the code that tells the type of hash to be cracked. The complete list of hash codes can be found here: https://hashcat.net/wiki/doku.php?id=example_hashes.
NTLM Hash Example
Let’s assume we have the following NTLM hash.
B3EC3E03E2A202CBD54FD104B8504FEF
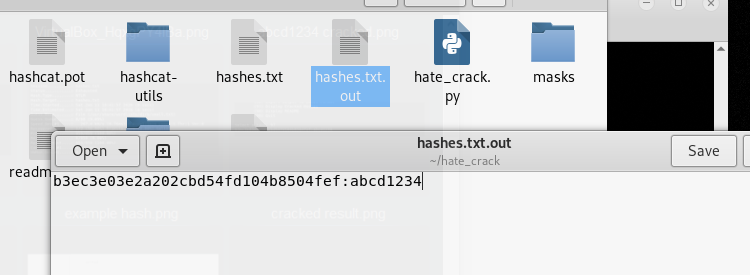
In order to break this hash, we copy the hash code in a file called hashes.txt. The code for NTLM type is 1000. The above Hate_Crack execution command takes the following shape.
./hate_crack.py hashes.txt 1000
The above command runs the Hate_Crack tool and gives the attack options in the following manner.
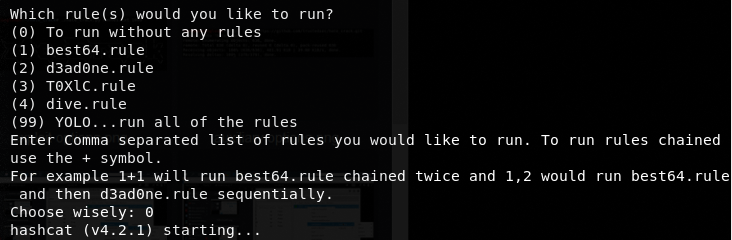
We can select any number to launch the attack. For instance, we can select the Quick Crack attack mode by typing its sequence number in the list (i-e 1). Hate_Crack supports multiple sets of rules that can be followed during the Quick Crack attack mode. We can either ignore or select multiple rules. Let’s continue without following any rule for the current example.
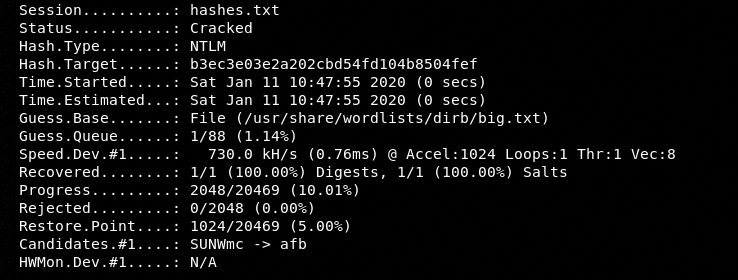
Hate_Crack runs different sessions in order to crack the hash. The Cracked status means the tool has successfully cracked the hashed string.
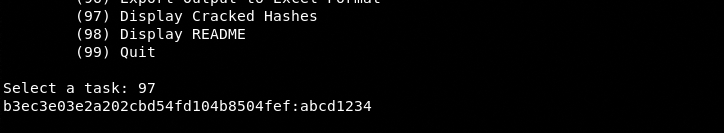
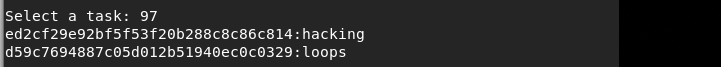
We can view the cracked hashes on the screen by typing the display code (i-e 97) in the terminal.
The tool also generates a new file in the directory that contains the successfully solved hashes.
We can provide a list of hashes to the tool. The results are displayed on the screen in the following manner.
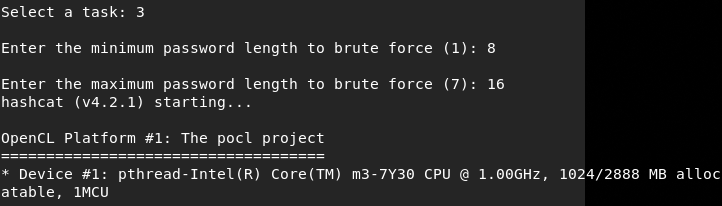
Similarly, we can also select different attack modes by typing their respective sequence numbers in the terminal.
Summary
Hate_Crack makes the Hashcat job easier by automating the cracking tasks. Multiple attack modes and the availability of different optimizers enhance the capabilities of the Hate_Crack tool.