Jok3r is a web + network security assessment framework capable of automating many penetration testing tasks. The framework identifies network and web vulnerabilities and exploits the security flaws where possible. Jok3r performs these tasks by rendering the functionalities of integrated open-source penetration testing tools and scripts. The penetration results are stored in a database that can be accessed through an interactive shell.
Network Security Assessment
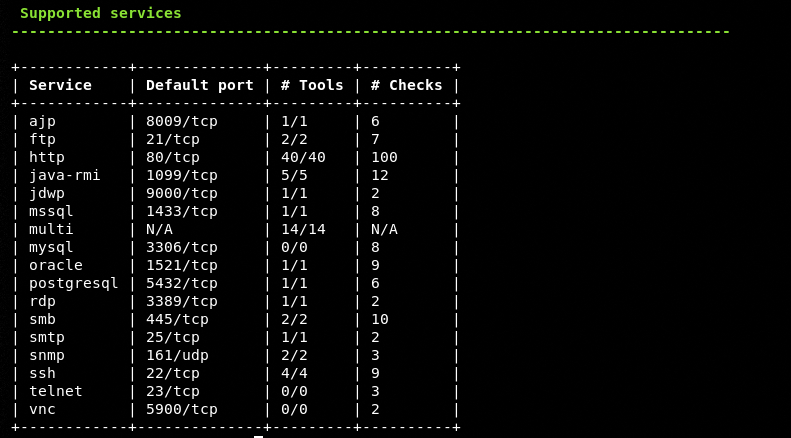
Jok3r has a number of network security assessment features, such as reconnaissance, vulnerabilities scanning, CVE lookup, and brute-forcing Product name, and version information detected during reconnaissance is further used to check Common Vulnerabilities and Exploits (CVE) by searching online CVE databases. The vulnerabilities scanning process is further extended to auto-exploitation attempts by the framework. Jok3r has a network brute-force attack feature that allows the framework to utilize features like dictionary attacks and customized wordlists options to check default/common network services credentials. A post-authentication of passwords is performed to verify the discovered credentials. Jok3r supports the majority of the common TCP/UDP services like HTTP, SMB, VNC, FTP, Oracle, MySQL, PostgreSQL, and MS-SQL to perform security assessment tasks.
Web Security Assessment
The web security assessment features of Jok3r include fingerprinting, vulnerabilities assessment, and server exploitation tasks. Fingerprinting includes tasks like identification of framework, programming language, Content Management System (CMS), web server, and JavaScript libraries. The framework scans common vulnerabilities related to CMS like WordPress, Drupal, Magento, Joomla, etc. Jok3r not only has the ability to scan web bugs but also has the tendency to automatically exploit most critical vulnerabilities.
How to Install Jok3r Framework
Jok3r framework can be cloned from Github using the following command. However, the installation process requires a lot of manual imports to fulfill all the dependencies.
git clone https://github.com/koutto/jok3r.git
The recommended method to install Jok3r is by pulling the Docker image using the following command. The Docker installation takes care of all the Jok3r dependencies and third-party scripts used by the framework.
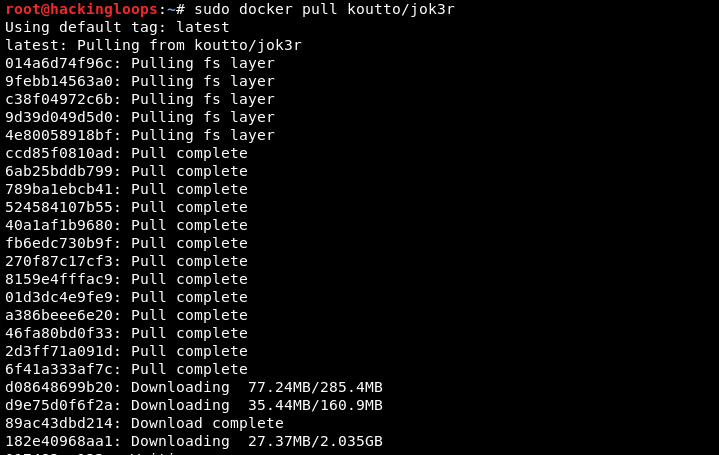
sudo docker pull koutto/jok3r
The pulling can take some time due to (8.7 GB) size of the Jok3r package.
How Jok3r Works?
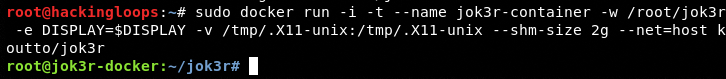
Once the image is successfully installed, use the following Docker container command to execute the framework.
sudo docker run -i jok3r-container
OR
sudo docker run -i -t --name jok3r-container -w /root/jok3r -e DISPLAY=$DISPLAY -v /tmp/.X11-unix:/tmp/.X11-unix --shm-size 2g --net=host koutto/jok3r
The above command can be dissected into the following details.
The -e DISPLAY=$DISPLAY -v /tmp/.X11-unix:/tmp/.X11-unix syntax is used to enable GUI applications like web browsers etc.
The –shm-size 2g show the shared memory size. The memory is kept higher in order to avoid applications crash during the scanning or reporting process.
The –net=host enables sharing of host’s interface. The setting is required to create reverse connections or perform tasks like getting a reverse shell.
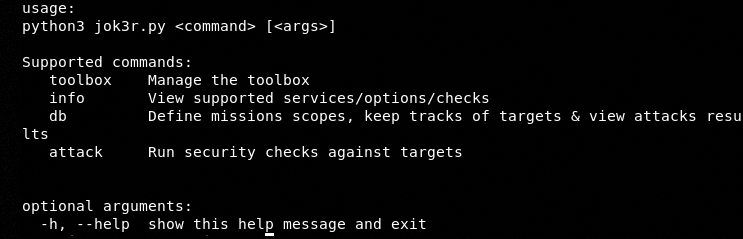
The following help command shows the framework’s usage options.
python3 jok3r.py--help
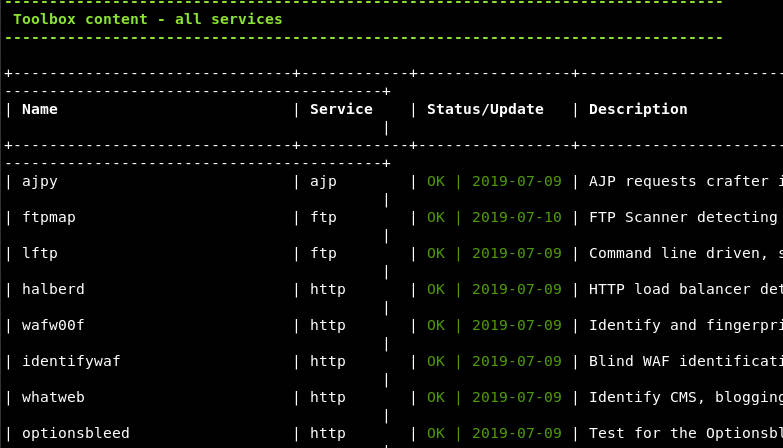
Jok3r framework is loaded with a number of scanning and exploitation tools that can be explored using the toolbox command.
python3 Jok3r.py toolbox --show-all
The above command displays all the available penetration testing tools, services, status, update history, and one-liner description about available tools.
The information about the supported services can be extracted using the services’ information command.
python3 Jok3r.py info --services
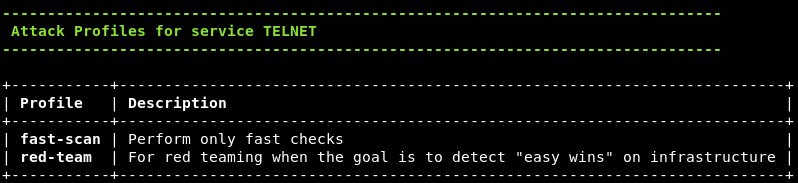
Similarly, we can check the available attack profiles for each supported service in the following manner.
python3 jok3r.py info –attack-profiles <service name here>
Example: Attack Profile for Telnet
Web Security Assessment Example
Jok3r framework stores all the penetration testing results in a local database that can be accessed through an interactive shell. In order to start the scanning process, we need to enable the local database using the following command.
python3 Jok3r.py db
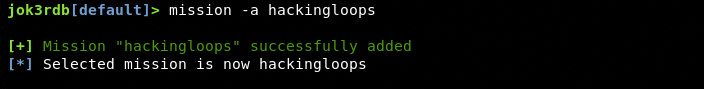
After enabling the database, the next step is to create the workspace, also called the mission, to record the scanning tasks. This can be achieved using the following command.
mission –a <mission name here>
For example:
mission –a hackingloops
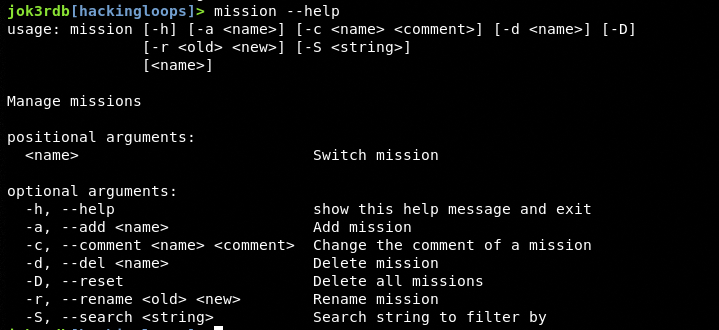
Other mission-related parameters can be viewed using the mission help command.
After successfully creating the mission, return to the main Jok3r menu using the quit option, and start the penetration process with desired attack options. The following command represents the basic attack syntax with all the services and attacks enabled.
python3 jok3r.py attack -t <target IP or URL here> --add2db <mission name here>
Consider the following example.
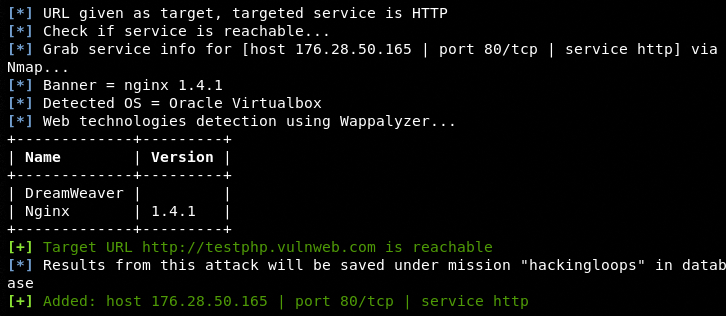
python3 jok3r.py attack -t http://testphp.vulnweb.com --add2db hackingloops
The framework initiates the scanning process by gathering the following information about the target host.
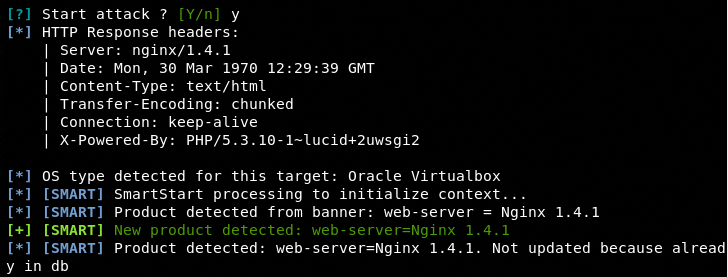
If the target host is reachable, Jok3r performs the HTTP headers check to extract valuable server, OS, cookies, and other technical information as shown in the following screenshot.
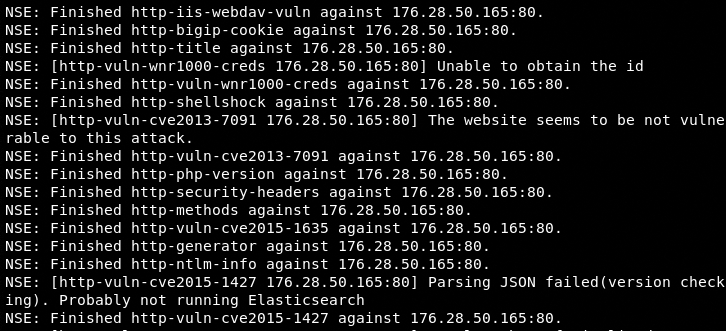
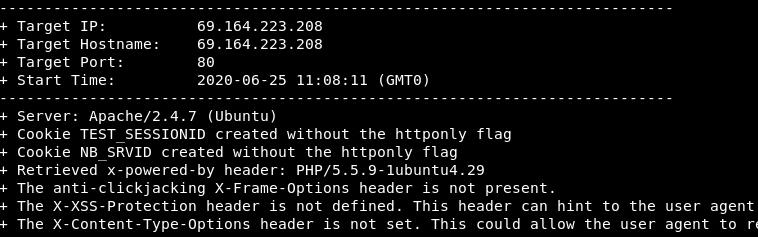
After performing the header response check, Jok3r runs a number of integrated scanning tools to find potential threats in the target host.
Similarly, we can specify specific attack options and services to customize the scanning process using the following command format.
python3 jok3r.py attack -t <target IP or URL here> -s <supported service here> --cat-only <selected attack/s> --add2db <mission name here>
In the above command, -s parameter is used to add the supported service for the penetration process. the –cat-only parameter represents the selected attack options. If we remove the –cat-only option, the framework runs all available attack options against the target host. The following command gives a more clear insight of the aforementioned command.
python3 jok3r.py attack -t webscantest.com -s http --cat-only vulnscan --add2db hackingloops
Note: We have selected an HTTP service and vulnerabilities scanning (vulnscan) option for our target host (webscantest.com). The scan results are to be stored in hackingloops workspace (mission).
Database Access
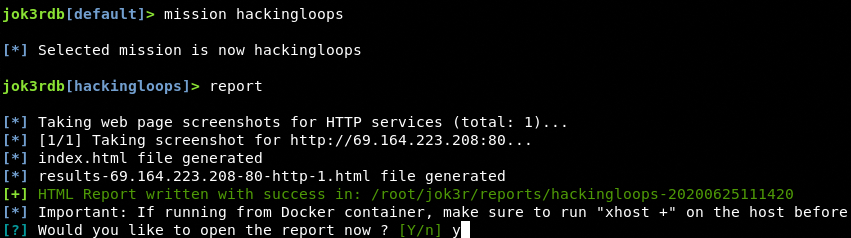
The scanning results can be analyzed by re-enabling the local database and accessing the defined workspace (mission) using the following commands.
python3 jok3r.py db mission hackingloops
We can either access part of the scanning information or generate complete scanning results in the form of an HTML report. The report can be generated by typing the report parameter in the terminal.
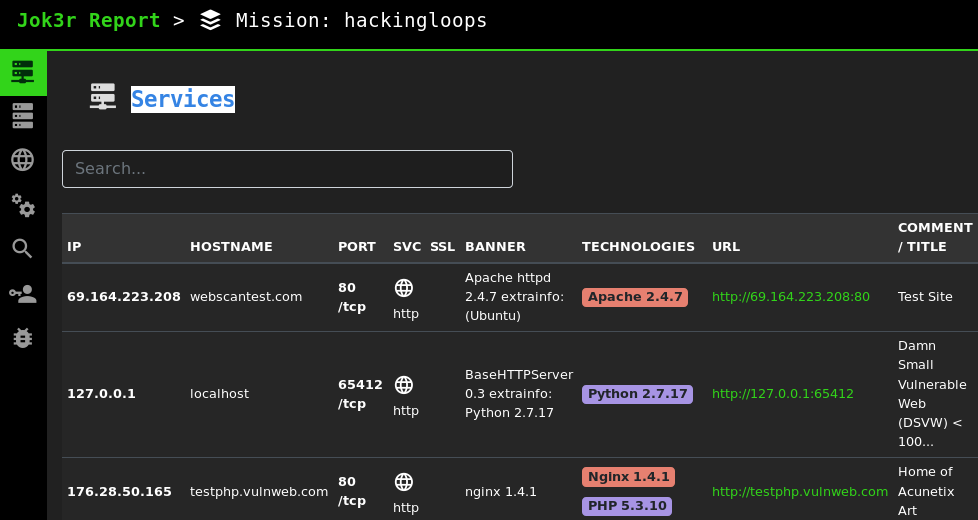
The report has an HTML interface showing all the scanned targets under a specific workspace.
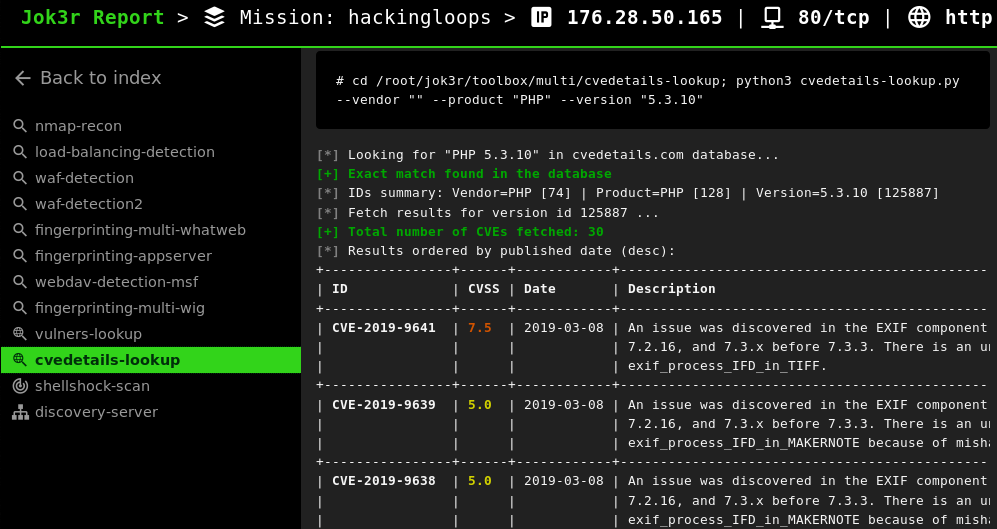
By clicking a specific target host, we can see all the scanning results as shown in the following screenshot.
Conclusion
Instead of relying on individual tools to perform security analysis, Jok3r can automate the Web and network penetration testing process by combining the functionalities of multiple tools. There is a wide range of scripts and supported protocols to run the framework against the majority of the existing cyber-threats. The framework is equally handy against web and network targets.