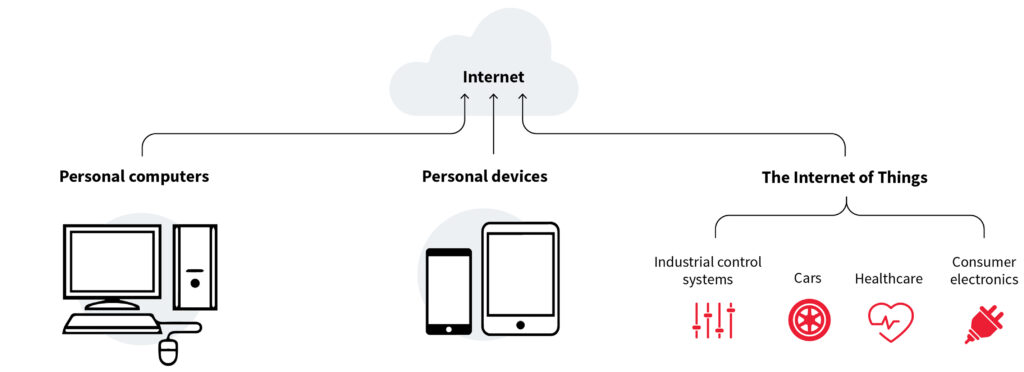
Before diving into IoT Security, it is important to know what is IoT and why we need it. IoT stands for Internet of Things. It is a system of interrelated computing devices assigned unique identifiers (UIDs) and the ability to transfer data over the network. This transfer is not dependent on any interaction (human-human or human-computer) rather it is completely automatic.
Adoption
With the speedy adoption of technology and involvement of the internet in our daily lives, we feel comfortable automating things and instructing/controlling them remotely. IoT provides an ecosystem in which each appliance is internet-facing.
Overview & Threat
These devices consist of sensors that sense the required parameter. They then send the measurement to some other device for some action. The devices may intercommunicate or send the data to a single entity. That single entity can then act based on received data. Now imagine, if any threat actor can change the readings, that could cause actions to be taken when not desired. This could be as simple as producing false results but also as disastrous to stake someone’s life.
IoT devices are widely in use in the health sector. One such example is a human heart monitor which will alert the doctor in case of any unwanted conditions. The attacker’s access to the device’s reading can cause severe consequences for the patient.
With the proliferation of these devices everywhere from our offices to our homes, it is important to make sure these devices are doing only their work, and not spying on us or taking commands from anyone else. IoT security is an important field that spreads over device security, network security, and much more.
Botnets
The 24-hour connectivity of IoT devices makes them an impressing target for hackers to recruit them into botnets. These botnets can then be used to launch attacks on other targets thus increasing the attack vector.
IoT devices only have limited power and memory. Combined, they can create a formidable army making a huge impact.
Bootloader
Bootloader, also known as the bootstrap loader and boot program, is a special program that is responsible for locating and loading all the required files and starting the Operating System. The files include kernel, filesystem, and other important programs as well.
Universal Bootloader (U-Boot) is a popular open-source bootloader. Various devices, platforms, and architectures use this.
Many vendors don’t update the bootloaders. This can enable the attackers to hack the IoT devices with legacy bootloaders and use them for attackers’ gains.
QEMU
Embedded device bootloaders are very tricky to work with. For this reason, the researchers use QEMU to emulate the devices. QEMU often emulates IoT devices as well.
IoT Security Testing Types
IoT device attacks are in wild still now. It is important to have an idea of what are some security testing types for these devices. Following are some of the common types
- IoT Penetration Testing: In this methodology, the security professionals try to find and exploit the security vulnerabilities and loopholes in the IoT devices. This testing is not just about testing the IoT device only but also the whole IoT system.
- Threat Modeling: Threat modeling of IoT devices is the process of finding and identifying the risks and determining a model to give an insight into how the device may be breached. For instance, the camera may be hacked and then used to spy on the people and even get the recordings.
- Firmware Analysis: Firmware is just software or a program but the only difference is that it is used in embedded devices with dedicated functionality. Securing firmware is important so as not to let the device misbehave under critical conditions. For example, if a heart rate monitor that alerts doctors of unusual conditions is compromised, it could cause serious problems for the patient. Firmware analysis includes testing it for backdoors, buffer overflows, and many other security issues.
Software Attacks
- Detecting Open Ports & Poorly Protected Communication Ports: Attackers use port scanning tools to find open ports and the services running on them. Then attack the found service and exploit it. Mirai botnet was an attack on IoT devices that appeared in 2016. It spread through default telnet credentials for thousands of unprotected devices.
- Sniffing: IoT devices at most use wireless communication which makes them prone to wireless attacks. This includes sniffing the traffic and analyzing the radio signals. The attacker can then find credentials and sensitive information from unencrypted packets.
- Detecting Backdoors: During development, some configuration interfaces enable the developers and testing teams to test the product. If left insecure in production can lead attackers to take over the operations depending on the scope of the interface.
- Buffer Overflow: Buffers in embedded devices have relatively small memory. Due to this, the attackers can send malicious code into rewritten parts to set a backdoor and control the device eventually.
- Password Cracking: Most IoT devices still have their default credentials. Mostly, the username is the same as the password. Thus, this attack is common to crack the credentials using either brute force or dictionary attacks.
- Debugging: In IoT devices, debugging interfaces are often insecure. This can lead an attacker to gain direct control of the device bypassing all security protocols.
- Firmware Modification: Malicious updates to uploading the malware are possible by modifying the firmware. Moreover, memory dumping is possible which leads to malicious code injection. Execution of that by the device might serve a malicious purpose.
- Reverse Engineering: In software attacks, most of the time firmware is available on the manufacturer’s website. This can be used to disassemble and reverse engineer the code and modify it according to the needs. Injecting code into the device is set up for local testing.
Invasive Hardware Attacks
- Reverse Engineering: In hardware, the attacker gets the device and disassembles it to identify the components. These components then give valuable information about the target making it easy to choose the attack.
Non-Invasive Hardware Attacks
- Cryptographic Analysis: Embedded systems implement AES or RSA to make secure communication. But an attacker can use the auxiliary channel attack to find the secret and decrypt the traffic.
- Memory Dumps: Many microcontrollers use a native memory dump function. This function is often insecure. Attackers can dump the memory of the connected devices through USB, SPI, and JTA ports.
Best Practices
- Make hardware tamper-resistant
- Provide firmware updates/patches
- Specify procedures to protect data on device disposal
- Use strong authentication
- Use strong encryption and secure protocols
- Specify Destroy method if the device gets a breakdown
