Katana Framework (KTF) is a multi-dimensional Python Framework that supports a number of open-source penetration testing scripts. These scripts or modules can be classified into the following three categories.
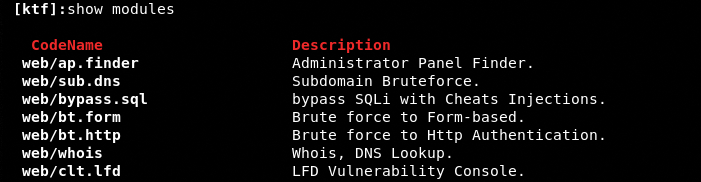
1) WEB MODULES
The web-related scripts include the following information gathering and vulnerabilities assessment modules.
- Login/admin console finder
- Subdomain lookup tool
- WHOIS information gathering utility
- DNS explorer
- Form and authentication-based bruteforce tester
- SQL and Local File Disclosure (LFD) vulnerabilities checker
2) NETWORK MODULES
The KTF contains network modules with the following scanning and offensive properties.
- LAN hosts scanning
- Ports scanning
- HTTP traffic sniffing
- DNS spoofing
- ARP poisoning
- ARP DOS attacks
- Web DOS attacks
3) MISCELLANEOUS MODULES
Besides web and network-scripts, there are some miscellaneous modules in the Katana framework that can perform the following penetration testing tasks.
- Metasploit payloads generation
- FTP, SQL, SSH, and POP3 protocols bruteforce
- Images forensics
- RAR and ZIP extension files bruteforce
- Wi-Fi DOS and phishing attacks
HOW TO INSTALL KATANA FRAMEWORK?
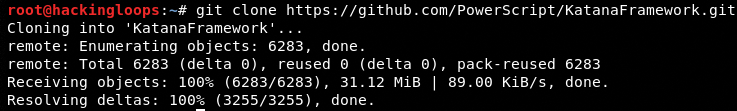
Katana Framework can be installed either by downloading the installation package from Sourceforge or cloning the source files from the following Github repository.
git clone https://github.com/PowerScript/KatanaFramework.git
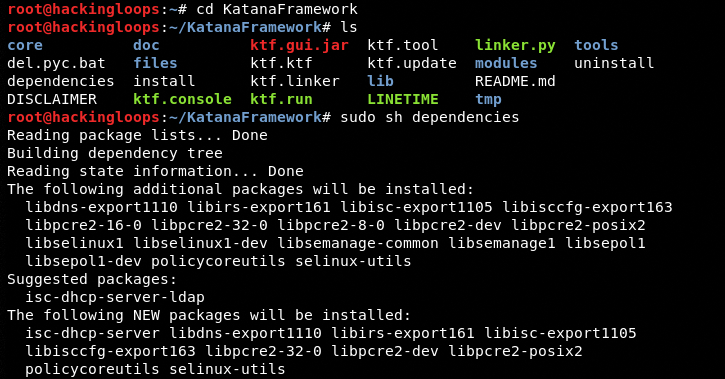
The missing packages/libraries can be installed using the following dependencies commands.
cd KatanaFramework sudo sh dependencies
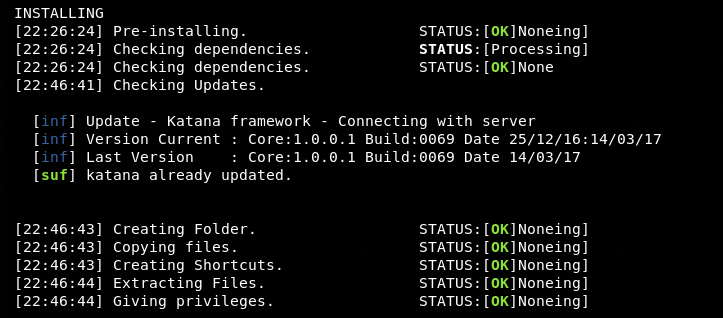
Once all the dependencies are fulfilled, run the following command to complete the installation process.
sudo python install
HOW KATANA FRAMEWORK WORKS?
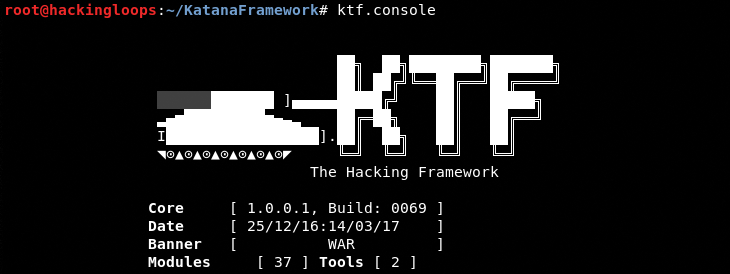
Operating the Katana framework is a fairly simple process. Execute the ktf.console file to load the root console of the framework.
ktf.console
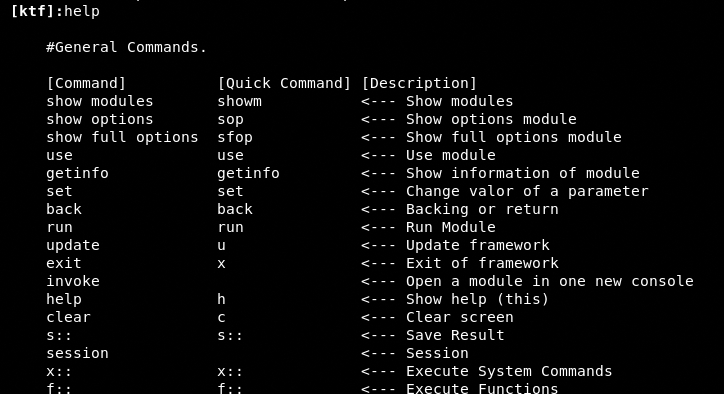
Typing the help command in the console displays all the following modules, functions, and parameters supported by the tool.
KTF Parameters
KTF Functions
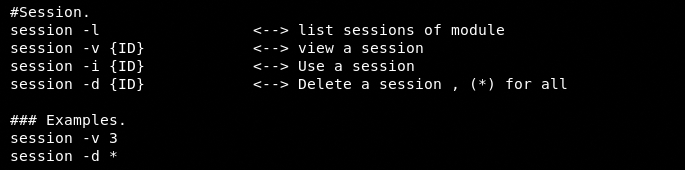
KTF Sessions
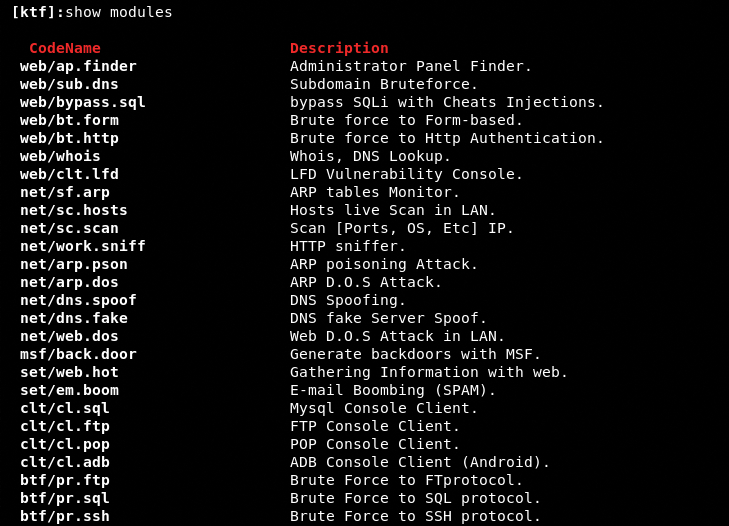
The following command displays all the inbuilt and integrated modules related to web, network, and miscellaneous functions.
show modules
We can run these modules using the following module execution command format.
use <module name>
USAGE EXAMPLES
In order to analyze the working of the Katana framework, we have tested some of the modules and functions supported by the framework.
WEB MODULE EXAMPLE
The KTF has support for the following web-based modules.
Let’s suppose we want to find the admin panels on the following test web application.
webscantest.com
We can use the web/ap.finder module for this purpose. The following command loads the admin panel finder module in the console.
use web/ap.finder
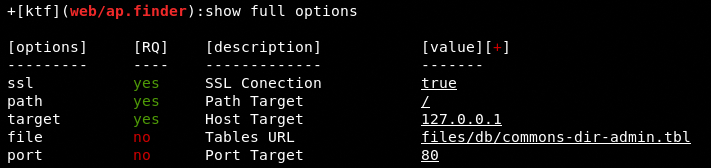
The show options or show full options command displays all the required and optional parameters used to run the module.
show full options
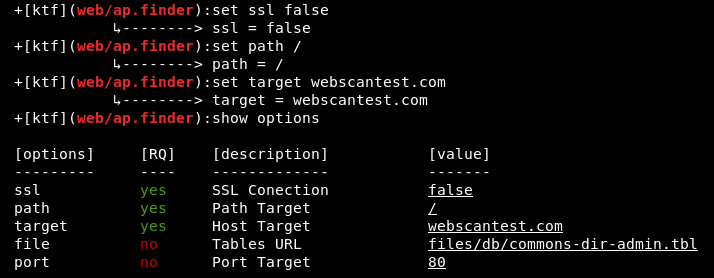
As we can see in the screenshot, the SSL, Path, and Target are the mandatory parameters. We can set values for these parameters using the following set commands.
set <parameter> <desired value>
The SSL parameter must be set to true or false depending on the availability of the certificate. Since the target test domain does not have a valid SSL certificate, we can set the SSL flag as false.
set ssl false set path / set target webscanttest.com
After setting all the required options, we can execute the module using the run command.
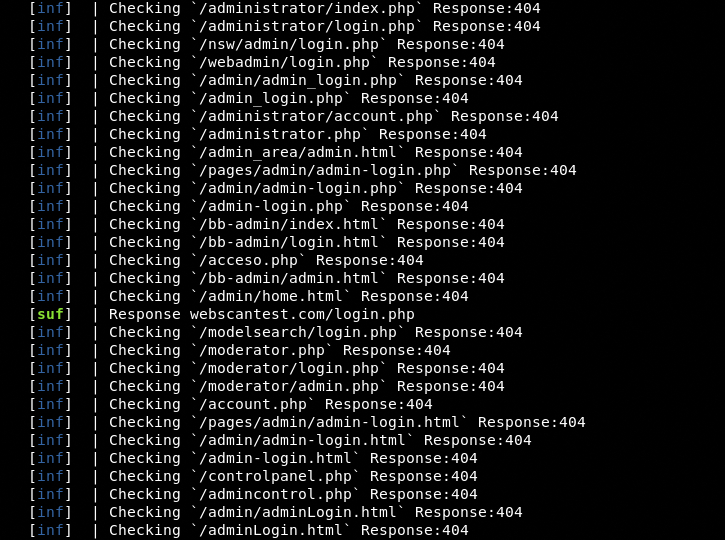
run
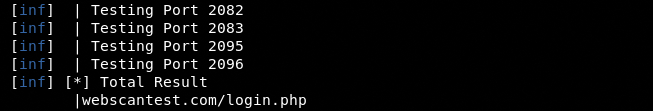
The module launches the bruteforce attack to find all the possible login pages on the target web host.
The successfully retrieved pages/results are displayed in the following format.
NETWORK MODULE EXAMPLE
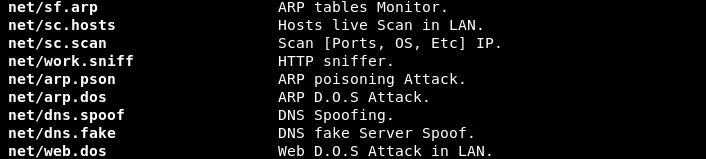
The following image presents the Katana’s network-related modules.
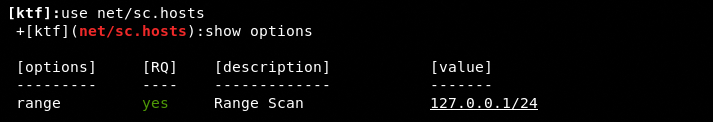
In this example, we use the net/sc.hosts module to find the live hosts in the local area network.
use net/sc.hosts
We need to define the LAN IP range using the following command in order to find the live hosts.
set range 10.0.2.1/24
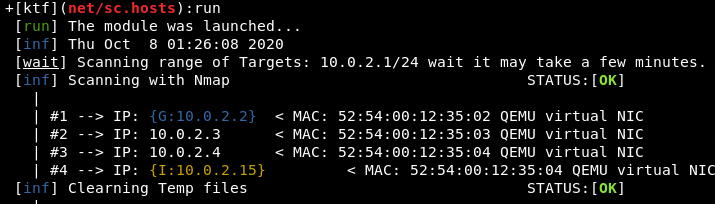
The run command triggers the module to fetch all live hosts in the network.
The module not only shows the live hosts but also gathers the MAC information of the live machines in the vicinity.
MISCELLANEOUS MODULES EXAMPLE
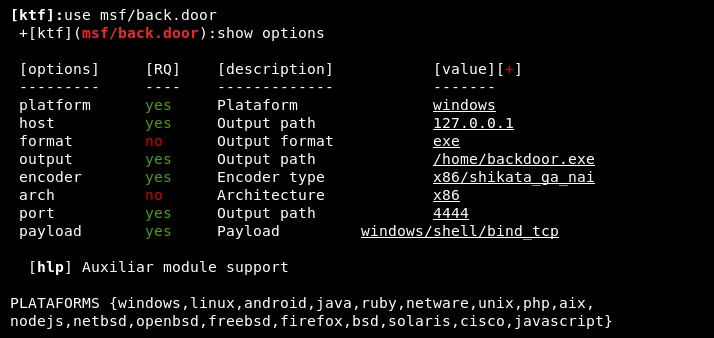
The selection and execution method for the rest of the scripts including the miscellaneous module is similar to the web and network modules. For instance, we can generate the Metasploit payload using the following MSF module.
use msf/back.door
The show options command displays all the available parameters and supported platforms to generate the desired payload.
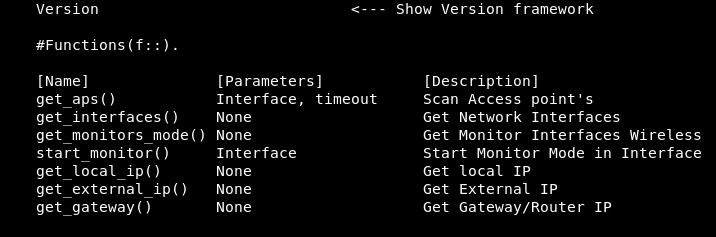
KATANA FRAMEWORK FUNCTIONS
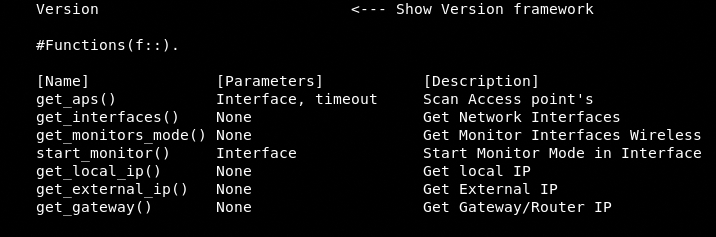
Besides modules, the KTF supports the following functions to perform miscellaneous activities.
We can run each function using the following syntax.
f::<function name>
For instance, we can find the internal IP address of the machine using the following function.
f::get_local_ip
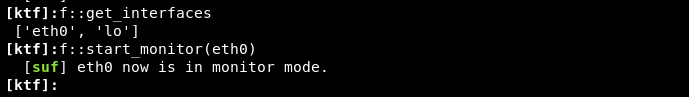
Similarly, we can find the network interfaces and put them in the monitoring mode using the following functions.
f::get_interfaces f::start_monitor_(etho0)
CONCLUSION
The Katana framework incorporates multi-dimensional penetration testing utilities in the form of some lightweight and robust third-party modules. The framework is focused on information gathering and vulnerabilities assessment of web and network domains. The framework can also be helpful in assessing the web and network security against various bruteforce and DOS attacks.