Offensive Security is an online provider of information security training and certifications. The founders of Offensive Security are also the creators of Kali Linux. The certifications offered by Offensive Security team are highly regarded in the field of Information Security. Following is a brief overview of the premium cyber-security certifications offered by Offensive Security team.
Offensive Security Certified Professional (OSCP)
OSCP is a trusted Information security certification offered by Offensive Security. The certification validates the core penetration testing (ethical hacking) knowledge and skills of Information security professionals. The OSCP holders are considered capable of performing the following tasks.
- Identifying and exploiting network vulnerabilities
- Identifying and exploiting web vulnerabilities, such as XSS, SQL injection, and file inclusion (LFI/RFI) vulnerabilities
- Simulating cyber-attacks to point out the weaknesses in cyber-defense systems
- Writing new scripts/codes for penetration testing
- Modifying/editing the existing penetration testing codes/scripts
OSCP Exam
Those who are interested in taking OSCP exam must complete the prerequisite Penetration Testing with Kali Linux (PWK) course. It is an online, self-paced course offered by Offensive Security team. Latest hacking tools and techniques are taught to the registered students with access to the virtual labs for practicing the tutorials. The PWK course covers the following topics.
| Information Gathering Techniques | Vulnerabilities Scanning |
| Win32 Buffer Overflow Exploitation | How to Use Exploits |
| Linux Buffer Overflow Exploitation | Privilege Escalation |
| Transferring Files | Web Attacks |
| Remote and Client Side Attacks | Port Redirecting and Tunneling |
| Password Attacks | How to Bypass Antivirus and Firewalls |
| How to Use Metasploit Framework | Penetration Testing Breakdown |
Source: https://www.offensive-security.com/documentation/penetration-testing-with-kali.pdf
The skills of examinees are tested using virtual networks, containing various targets with different configurations. The candidates are given 24 hours to perform different penetration testing tasks, such as scanning targets, finding vulnerabilities, gaining access, escalating accounts’ privileges, and maintaining access. A penetration testing report containing detailed notes and screenshots of the findings is submitted by each candidate at the end of exam period. The candidates are assessed and awarded on the basis of submitted penetration testing report. Those who pass the OSCP exam are informed through email with the credential proof. Offensive Security does not issue the digital version of the OSCP to the successful candidates.
Offensive Security Certified Expert (OSCE)
OSCE is one of the most challenging certification offered by Offensive Security. The individuals who possess OSCE certification are considered capable of performing the following tasks.
- Identifying hard-to-find vulnerabilities, such as Address space layout randomization (ASLR) issues
- Finding coding errors and security flaws through fuzzing
- Doing analysis, correction, and modification of exploitation codes
- Writing powerful scripts that can bypass antivirus software
OSCE Exam
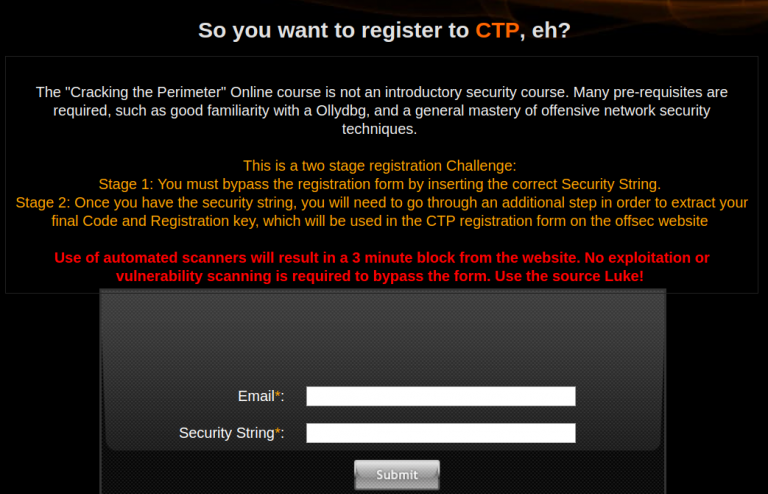
Cracking the Perimeter (CTP) is the prerequisite course before going for OSCE exam. CTP is an online, self-paced advanced level penetration testing course designed for penetration testing experts and security professionals. Since it is an advanced level course, the interested students (certification candidates) must have prior understanding of Windows exploitation techniques, OllyDbg, shellcode encoding, Metasploit framework, and Linux OS. Registration for CTP online course is not a straightforward process. Candidates are required to complete an online challenge of bypassing the registration formalities.
Those who fail in solving the online challenge are considered ineligible for course registration and OSCE certification. The CTP course covers the following topics in detail.
| Introduction | The Web Application Angle |
| Cross Site Scripting Attacks | Directory Traversal |
| The Backdoor Angle | Backdooring PE files under Windows Vista |
| Advanced Exploitation Techniques | Dealing With Vista |
| Cracking the Egghunter | The 0Day Angle |
| Windows TFTP Server | HP Openview NNM |
| The Networking Angle | Bypassing Cisco Access Lists |
| GRE Route-Map Kung Fu | Sniffing Remote Traffic |
Source: https://www.offensive-security.com/documentation/cracking-the-perimeter-syllabus.pdf
Those who successfully complete CTP course can take OSCE examination. OSCE is a 48 hours online exam that tests the advanced level penetration testing skills of the candidates in a virtual environment. The examinees are required to submit a report of their findings and accomplished tasks. The candidates are informed through an email about the results and issuance of OSCE certification.
Offensive Security Web Expert (OSWE)
OSWE certification is designed to validate web applications penetration testing skills of the individuals. The OSWE holders are considered expert in performing the following penetration testing tasks.
- Auditing web applications codes
- Finding web application vulnerabilities
- Launching pre-written web exploits
- Writing new exploits for web applications
- Compromising sanitization filters
- Performing chain attacks through multiple vulnerabilities
OSWE Exam
Advanced Web Attacks and Exploitation (AWAE) is the prerequisite course before applying for OSWE exam. AWAE is an online course that covers web application security and penetrating testing techniques. Since AWAE is an advanced level course, the interested individuals should have prior understanding of web attack vectors, knowledge of file permissions, clear concepts of writing and editing codes, expertise in programming languages (such as Python, Perl, and PHP), and knowledge of web proxies like Burp suite. AWAE course covers the following topics in detail.
| Cross Site Scripting | Cross Site Request Forgery |
| Session Hijacking | Data Exfiltration |
| SQL Injection | .NET Deserialization |
| Evading File Extension Filters | Evading File Upload Permissions |
| Bypassing REGEX | Bypassing Character Constraints |
| Postgre SQL | Hashes |
| Comparisons | .Net Assemblies Debugging |
Source: https://www.offensive-security.com/documentation/awae-syllabus.pdf
OSWE exam consists of virtual network containing web applications and operating systems. The candidates are given 48 hours for fingerprinting web applications, finding web vulnerabilities, and exploiting them. The report submitted by each candidate at the end of exam evaluates the successful exploitation of hosts by the examinees. The OSWE results are announced and dispatched through emails.
Offensive Security Exploitation Expert (OSEE)
OSEE is an advanced level exploits development certification that validates users’ knowledge and skills to develop effective exploits through research, reverse engineering, and code assembly/disassembly. OSEE holders are acknowledged for performing the following tasks.
- Creating custom shell codes
- Developing sophisticated exploits
- Performing precision heap sprays
- Exploiting Windows Kernel drivers
- Evading Data Execution Prevention (DEP) and Address space layout randomization (ASLR) securities
OSEE Exam
Offensive Security offers Advanced Windows Exploitation (AWE) course to all the candidates interested in OSEE certification. AWE is a pre-requisite course for OSEE that is taught live at Black Hat USA in Las Vegas. Those who cannot make it to the Black Hat USA can opt for In-House training sessions offered by Offensive Security. It is highly recommended to have windows exploits, debuggers, and Python scripting knowledge before taking the AWE classes. Topics covered in AWE course are listed below.
| NX/ASLR Bypass Techniques | Function Pointer Overwrites |
| Precision Heap Spray | EMET Mitigations Techniques |
| Windows Kernel Exploitation Techniques | Kernel Pool Exploitation Techniques |
Source: https://www.offensive-security.com/information-security-training/advanced-windows-exploitation/
OSEE exam consists of virtual labs having systems with specific vulnerabilities. The candidates are given 72 hours to find the vulnerabilities and develop the exploits. A documentation report is required at the end of exam to evaluate the performance of each candidate.