Quasar is a penetration testing framework used for information gathering purpose. The framework can gather web related information, email address data, phone numbers record, credit cards’ bank information, ports record, and IP geo-information. The website information that can be collected with Quasar includes DNS record, WHOIS data, GeoIP information, subnet information, website status (up/down), and robots.txt information. The email address checker facility is used to find out usernames, domain (service provider), MX record availability, SMTP status, and nature of email service (whether it is free or premium). The phone record checker facility offered by Quasar is capable of finding valuable phone number related information, such as number validity, country code, country name, location, phone number carrier, and line type (mobile or landline number). Credit cards’ BIN checker is another noteworthy feature of Quasar. BIN (Bank Information Number) are first 4 to 8 numbers on Credit Cards that provide valuable information like issuing country, brand, credit card type, schema, and card length.
Quasar Installation
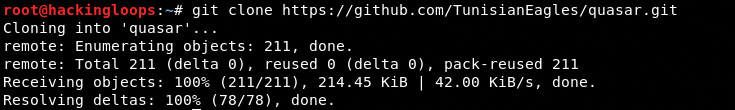
In order to install Quasar, clone the framework from Github using the following command.
git clone https://github.com/TunisianEagles/quasar.git
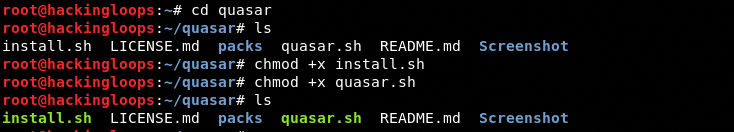
Navigate to the framework’s directory and change file permission for install.sh and quasar.sh files as shown in the following commands.
cd quasar chmod +x install.sh chmod +x quasar.sh
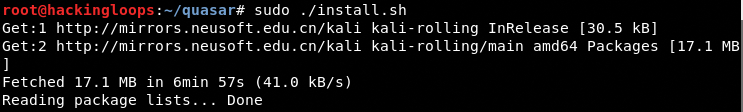
Finally, run the install.sh file to complete the installation process. All the dependencies are installed and checked by the framework during the installation process.
Quasar Working
In order to run Quasar, type the following command in the terminal.
./quasar.sh
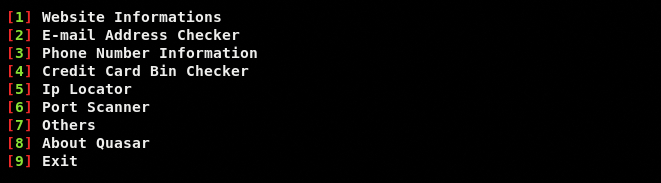
The above command opens Quasar’s main menu as shown in the following screenshot.
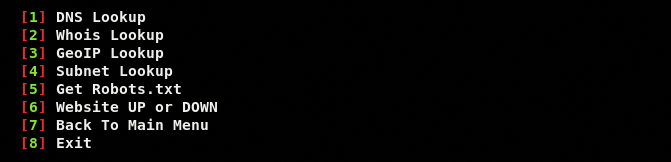
The menu lists all the information modules. Each module can be explored by typing its sequence number in the terminal. For instance, we can explore web information about a specific domain by typing the sequence number of website information module (i-e #1) in the terminal. By selecting web information module, another sub-menu appears on the screen as shown below.
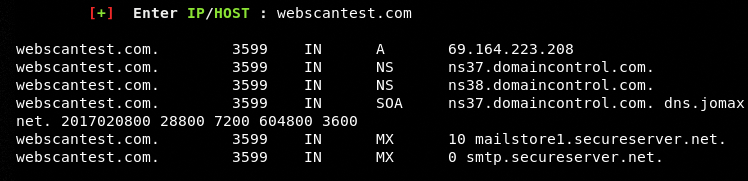
Each sub-menu option can be explored by referring its sequence number in the terminal. For example, we can check the DNS record by mentioning its sequence number (i-e #1) in the terminal. The results are shown in the following format.
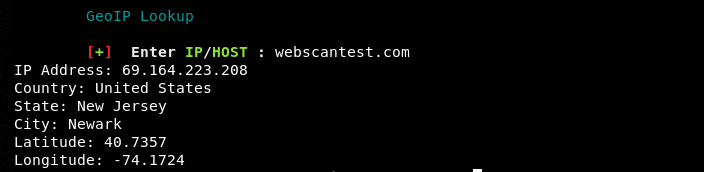
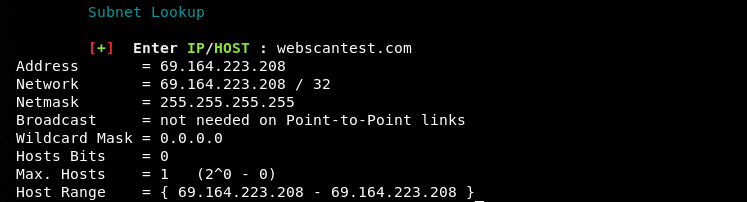
The other web related options like WHOIS record, Geo IP lookup, and subnet information can be obtained in a similar way.
Geo IP Lookup
Subnet Record
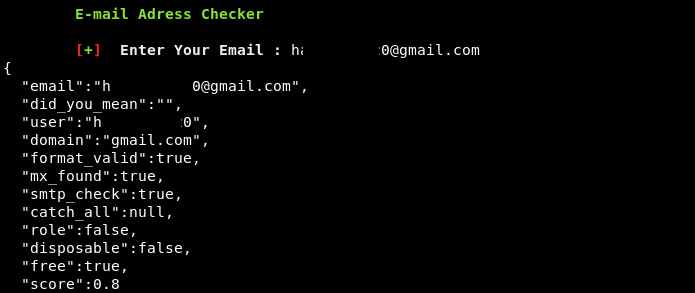
The process of exploring all the information gathering modules is similar to the web information module. We can select the Email address module by typing its sequence number (#2) in the terminal. The module asks for a target email address to fetch the record as shown in the following screenshot.
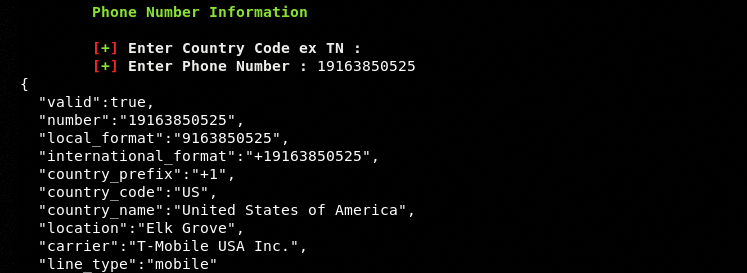
The phone number record obtained by Quasar framework can be seen in the following screenshot.
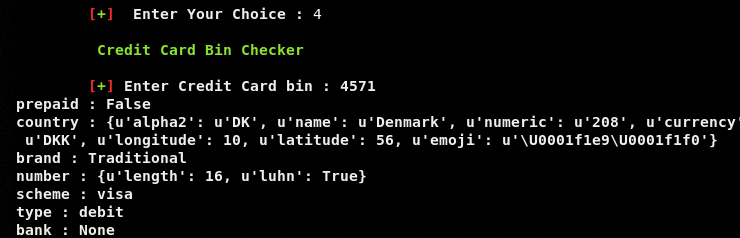
BIN checker is a unique information gathering feature of Quasar. The framework validates credit card issuer and related information as shown in the following example screenshot.
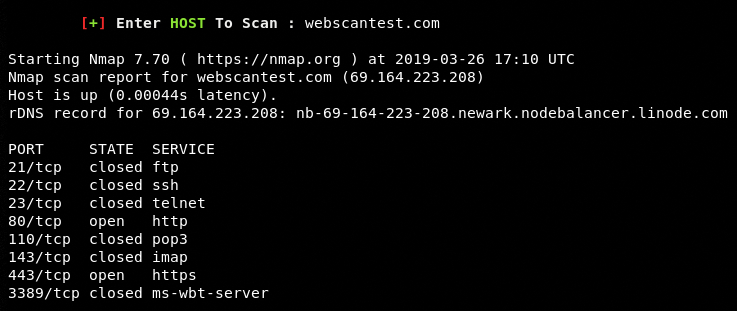
The port scanner module searches specific ports to learn about their status as shown below.
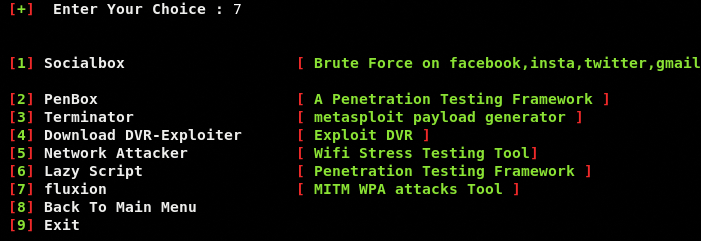
Apart from aforementioned utilities, Quasar can also run other tools mentioned in the Others category, listed in the main menu. The supported tools can be seen in the following screenshot.
Summary
Apart from websites information, penetration testers can use Quasar for finding useful information about emails and phone numbers. The integration of third-party tools like Fluxion and Socialbox with Quasar makes the framework more valuable.