A database can be defined as the organized set of data that can be stored and retrieved electronically from the Database Management System (DBMS). The database is the key asset in any organization. It is also one of the key targets of hackers. There are a number of security incidents reported in the past where hackers managed to breach the large data set of the respective organizations. In 2016, hackers got access to personal details and secret credentials of 1 billion YAHOO users; in 2017, EQUIFAX, a US credit bureau, faced a cyber-attack that compromised personal and financial details of 147 million consumers; in 2018, 162 million users’ record including secret credentials of DUBSMASH was stolen and shared on Dark web. DUBSMASH is a video messaging service with millions of consumers; In April 2019, personal information and passwords of 540 million Facebook users were exposed; in 2020, the security researchers discovered that the LiveJournal blogging service is running a beached database with around 26 million compromised login credentials. All these incidents indicate that the database is the most sensitive and lucrative target that requires serious Cybersecurity defense measures.
UNDERSTANDING DATABASE FROM SECURITY PERSPECTIVE
It is literally impossible to secure the database without understanding the key concepts of database management. According to Verizon’s 2020 Data Breach Investigation Report, human errors including misconfiguration of databases was one of the key factors of data breaches. Therefore, it is important to understand how the database works, how it is created or modified, and what security checks are required in order to secure the database from cyber-attacks. In this tutorial, we shall cover how to create an environment where we can practice database commands to explore the database working.
CREATING THE DATABASE ENVIRONMENT
There are different types of databases that we shall cover in the upcoming database series. The current working environment is being set up for the relational database. In the relational database model, the data is stored in the form of rows and columns. The rows are termed as ‘tuple’ and columns are known as ‘attributes’. Together they form a table called ‘Relation’. In order to create a relational database, we require the following two basic tools.
1) Relational Database Engine
2) Database editor
RELATIONAL DATABASE ENGINE (SQLite)
Relational Database engine or the Relational Database Management System (RDBMS) is the program that manages the database record. It allows users to insert data, retrieve data, modify data, or even delete the data from the database with the help of instructions (commands). There are different RDBMS available that can be used as a Database engine (Db engine) to practice the database commands. However, we have selected the SQLite mainly due to the following reasons.
- SQLite is server-less, unlike other Db engines that operate as a standalone server. Hence no configuration is required other than installing the SQLite engine
- Database is stored in a cross-platform single disk file
- A very small source code with all necessary Db features
- SQLite is a cross-platform engine that is supported by all major operating systems
SQLite LINUX INSTALLATION
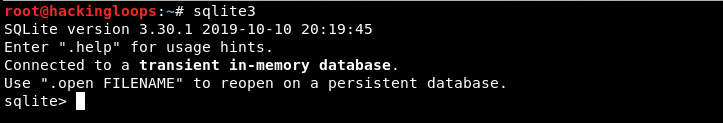
SQLite comes as a preinstalled package in many Linux OS. The installation can be confirmed by typing the following command in the terminal.
sqlite3
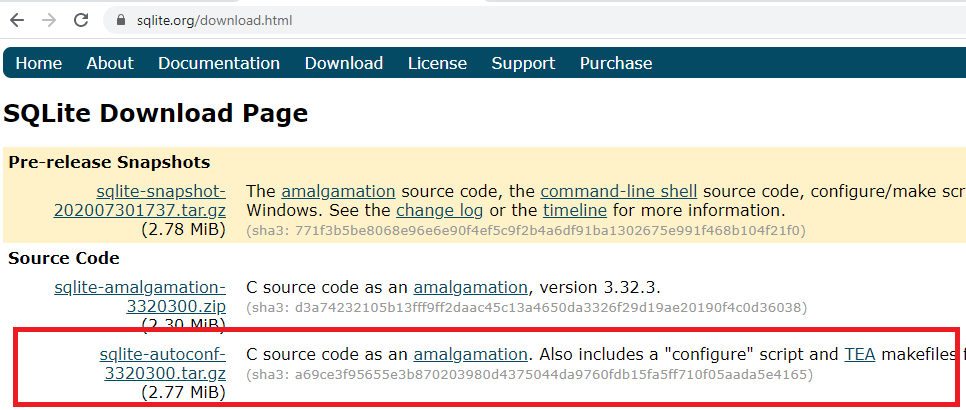
If the package does not exist, it can be downloaded from the following SQLite repository.
sqlite.org/download.html
To install the Linux version, we need to download the following highlighted source code file.
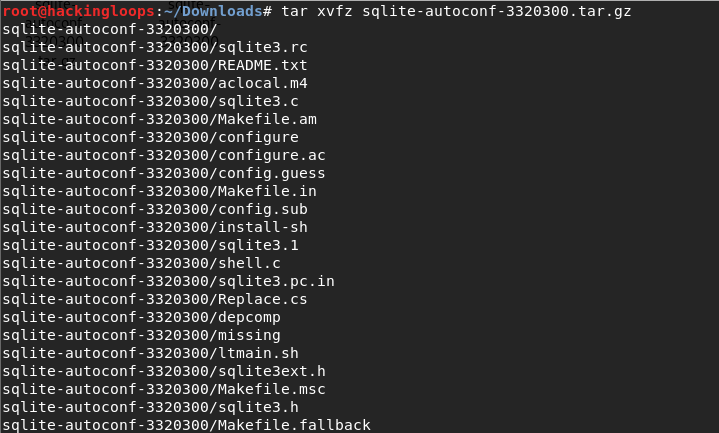
When the download is completed, extract the package using the following command.
tar xvfz sqlite-autoconf-xxxxxxx.tar.gz
[Note: xxxxxxx represents the latest release version which is currently 3320300]
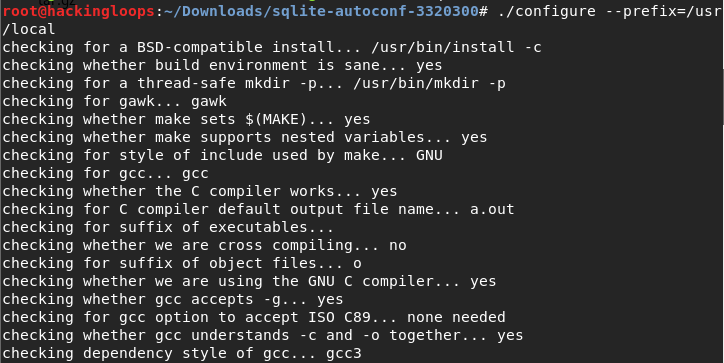
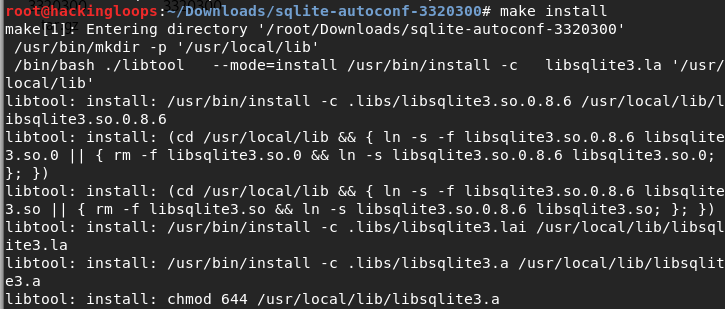
In the next step, run the following commands to complete the SQLite installation process.
cd sqlite-autoconf-3320300 ./configure --prefix=/usr/local
make make install
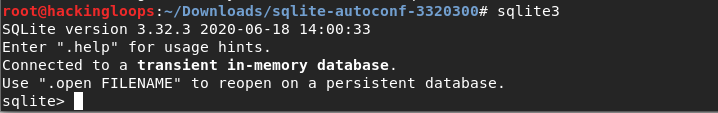
After the installation is completed, run the following command again to confirm the SQLite package installation.
sqlite3
DATABASE EDITOR (SQLite STUDIO)
Although SQLite comes with a pre-built Command Line Interface (CLI) which is enough to write and execute SQLite commands, we require a GUI editor that should display the Db commands and results in the same window. There are different GUI editors available to interact with SQLite, we have opted for the SQLite STUDIO, which is an open-source GUI editor for SQLite and other relational database management systems.
SQLite STUDIO INSTALLATION
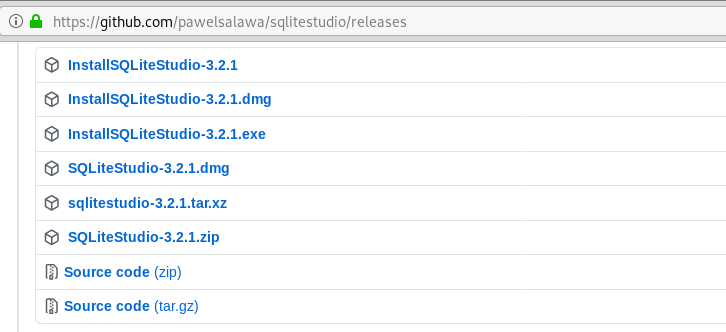
To install SQLite studio GUI, navigate to the following Github latest release page.
https://github.com/pawelsalawa/sqlitestudio/releases/
Select the desired version according to your OS. In our case, it is sqlitestudio-3.2.1.tar.xz.
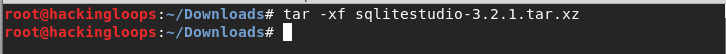
Download the package and extract the source code files using the following command.
tar –xf sqlitestudio-3.2.1.tar.xz
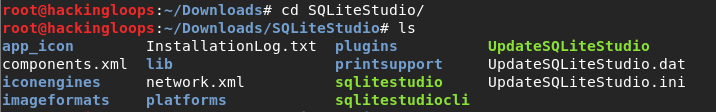
In the next step, navigate to the SQLite studio directory.
Locate and change the permission settings for sqlitestudio file if it is not already an executable file.
chmod +x sqlitestudio
Now open the SQLite studio GUI editor using the following command.
./sqlitestudio
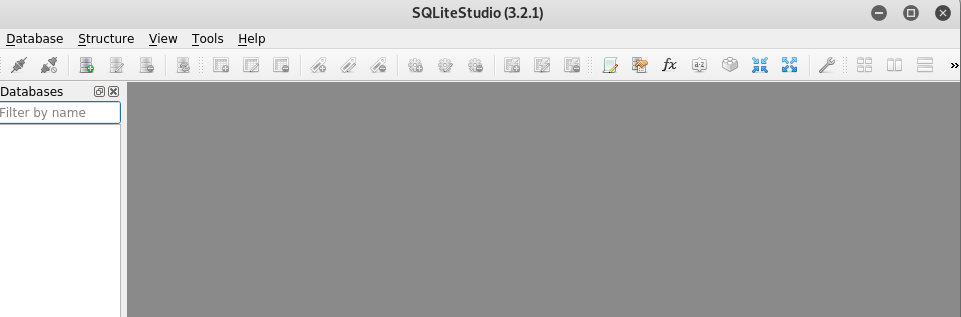
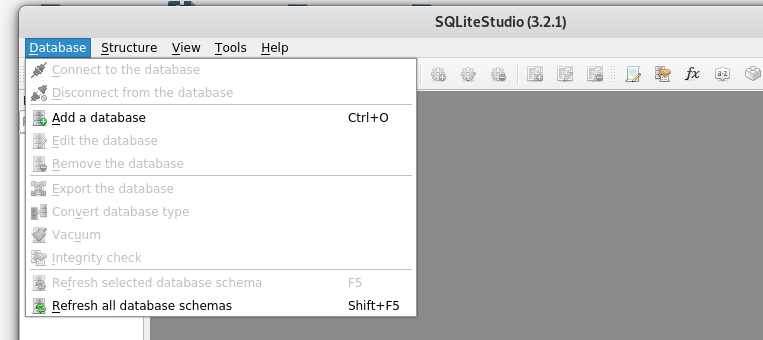
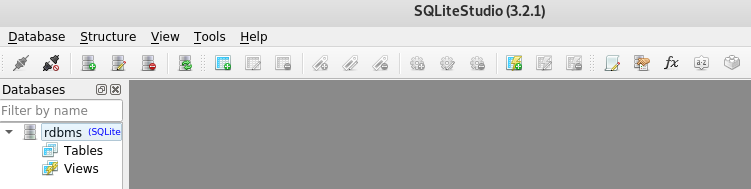
In SQLite studio, all the databases appear on the left sidebar of the dashboard. New database files can be imported or created from the top Database menu bar.
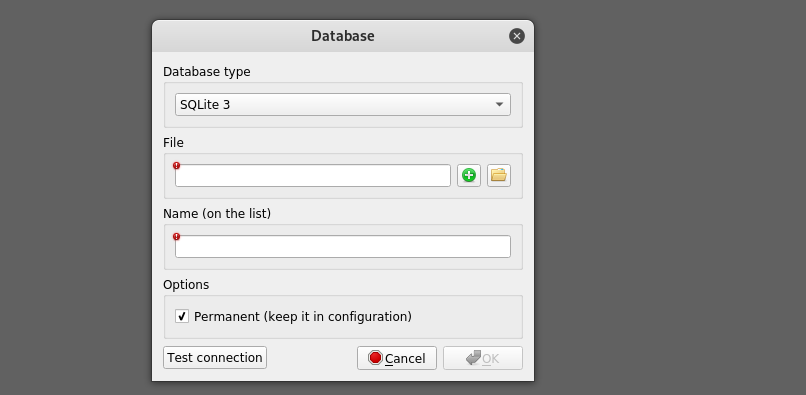
By clicking the new database option, the following window pops up on the screen showing database name and file path.
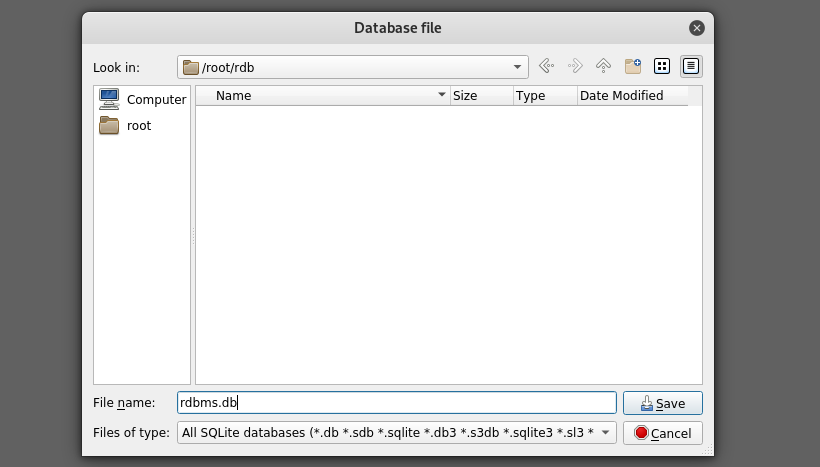
Since we don’t have any file to import, click on the green plus (+) sign to open a new window asking for the new database file name and location. For demonstration purposes, we have created an rdb folder and rdbms.db as our database file.
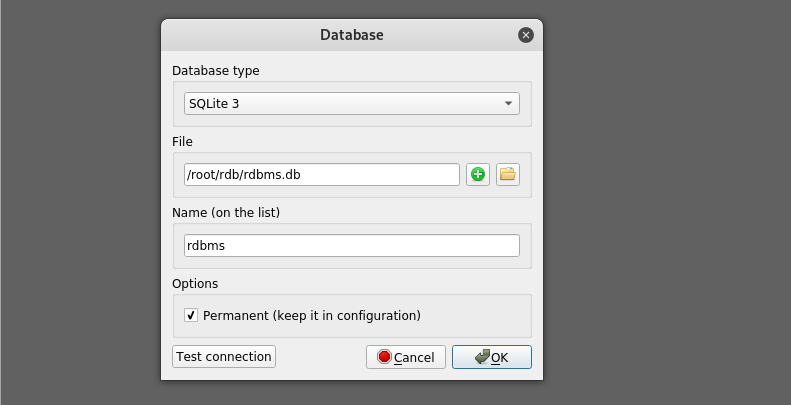
A confirmation window appears again on the screen showing the details about the database file name and path.
The newly created database file (rdbms.db) now appears in the left sidebar of the dashboard, as shown below.
New tables and data can be added to the created Db file. This concludes the basic working environment for relational database management systems. In the next tutorial, we shall cover all important relational database commands to get an idea about how the database works.
Conclusion
In order to understand what makes database vulnerable to cyber-attacks like database injections, it is important to know the working of Database Management Systems. Since the relational database is the most common model in use, we have deployed a relational database working environment to explain the database working which we shall cover in our next article. Stay tuned!