Among many cyber terminologies, the risk manager is one of the crucial ones. Let us tell you why. Becoming a cyber risk manager in 2022 helps identify, quantify, and manage potential risks on the overall system fit for today’s tech-centered world.
To maintain a risk-free business, a risk manager is a no-brainer. Yet some companies find it challenging to hire a risk manager due to their lack of effort of going the extra mile. Cybersecurity specialists filling in the qualifying positions are suited to do their job fine. Still, a risk manager is needed to keep a sharp overall lookout.
Table of Contents:
- What is Cyber Risk Manager?
- Skills & Certifications for Cyber Risk Manager in 2022
- Cyber Risk Management Framework
- What is the Purpose of Risk Manager?
- Risk Manager Career
- Recap
What is Cyber Risk Manager?
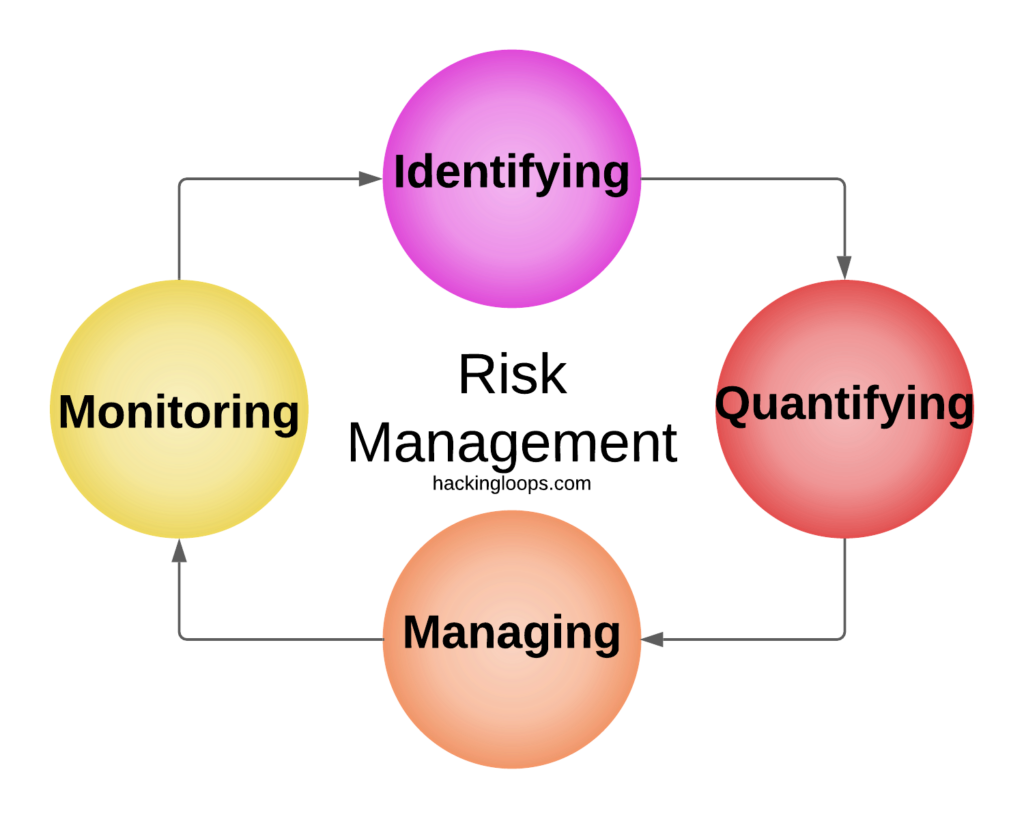
A cyber risk manager has various tasks under their wings regarding cyber security. Any part of cyber risk assessment is part of cyber risk manager. The governance circling the title involves monitoring the network, identifying risks, analyzing risk, and evaluating the task at hand.

Once the evaluation is complete, the risk manager must prioritize the options to tackle first. The cybersecurity team handles the operation and works against potential threats.
Phishing attacks, ransomware, social engineering, DDoS, logging, along protecting valuable company information from going to the wrong hands are part of the title. It may seem like much, and you may ask why a cyber risk manager has to do all that.
The cyber risk manager helps develop a plan to tackle the issue rather than debugging loopholes. The IT or cyber team’s task is to work on the pre-made schedule. It makes the process more straightforward in a professional way.
Skills & Certifications for Cyber Risk Manager in 2022
A cyber risk manager comes into play with a wide array of services. Questions arise because debugging is not the only perk with cyber security experts. But their experience is reflected in the thinking process to tackle the issue.
Landing the dream job has never been easy, and it shouldn’t be.
Why?
-Easy things don’t bring the same level of satisfaction that the challenging route provides. It is the same for pretty much everything. Let’s not get off track now.

There are plenty of job opportunities regarding risk management; you’ll find a few notable mentions below.
If the risk manager piqued your interest, then chances are some of the skills we are about to point out here are already on your basket.
Having a bachelor’s or master’s degree often helps—specifically, one in computer science-related fields. Having a degree means you’ve undergone the structural measures for a great professional career.
Though any specific degree area could pull off a risk manager career, it helps to have something relating directly to the field. Information technology, cybersecurity, information science, and engineering are notable mentions.
However, certification is a game-changer. In Hackingloops, we got you covered in that section too. Check Cyber Security Certifications Compared | Which Is Best.
Certified Information Systems Security Professional (CISSP), Certified in Risk and Information Systems Control (CRISC), Certified Information Security Manager (CISM) are some honorable mentions for you to check.
There is also a wide array of technical skills related to risk management. Understanding cyber security measures are extraordinary; an outlook on business management gives additional benefit. Also, there are a few frameworks that will help in becoming a cyber risk manager in 2022.
Cyber Risk Management Framework
A few standardized presets are kept in place as the ideal solution for cyber risk management, which we call a cyber risk management framework. Understanding them is vital as it helps build the portfolio suited for industry standards.

The risk management framework helps perform a risk analysis, measure the program’s problem-solving skills, and keep every other aspect in check. Similar to industry-standard features of other business products, a cyber risk manager relies on the framework.
NIST CSF
The NIST CSF framework, otherwise known as the International Institute of Standards and Technology Cybersecurity Framework, is one of the popular and primary ones.
The framework has utility as a structure and language for organizing and expressing compliance. Organizations’ cybersecurity requirements demand the NIST CSF framework to function correctly. Otherwise, ‘compliance with the Framework’ can be confusing.
NIST CSF provides end-to-end activities and structured outcomes of the five-core cybersecurity function. These are risk management, identifying, protecting, detecting, responding, and recovering.
DoD RMF
DoD RMF combines the Department of Defense and Risk Management Framework.
Six steps of the RMF framework are:
- CATEGORIZATION of information security system (FIPS 199/ SP 800-60).
- The second is the SELECT of security controls (FIPS 200/ SP 800-53).
- The third is the IMPLEMENT level, where security controls are taken a step further to SP 800 Series.
- The fourth step is ASSESS management, where security controls go through SP 800-53A.
- Fifth is the AUTHORIZATION step, where information systems follow SP 800- 37.
- Last but not least, the sixth step is the MONITOR of security controls under SP 800-53A.
These six distant features are packed under one set of tunneling, making DoD RMF one of the standard frameworks for the cyber risk manager.
ISO
The International Organization for Standardization (ISO) is a trendy framework, and its workability also remains in cyber risk management. The ISO 31000 Risk Management has a set of training courses and certifications. They provide an easy route to work, to complex corporate discussions, according to PECB.
Companies want leadership roles as risk managers for their operations. Mission integrity is achieved when ISO 31000 is followed and is the acceptable standard throughout the management.
FAIRTM
The Factor Analysis of Information Risk is a notable framework in the cyber risk manager role developed by The Open Group. The premier Value at Risk (VaR) model for cybersecurity is given a lot of priority in the framework. The non-profit professional organizations help companies and enterprise businesses advance towards a disciplined measure of cyber risk management.
Currently, the framework has more than 12,000 global members, with 45% of fortune 1000 organizations using it.
A few notable mentions in the cyber risk manager framework are the Internet Security Controls (CIS), Payment Card Industry Data Security Standards (PCI DSS), etc.
But remember, it’s the process that counts for the framework. So, applying your thoughts, knowledge, and expertise along with the relation of the framework will put you in a higher position than the rest practicing the essentials.
What is the Purpose of Risk Manager?
A risk manager in cybersecurity goes through several steps and makes it a seamless experience. Identifying certain risks that may pose a threat to the company in the future takes a bit of background. Eavesdropping the system and looking every nook and corner to find vulnerability takes advanced knowledge in cybersecurity.

A cyber risk manager in 2022 thinks like a veteran hacker, as the post requires prevention methods from those. Identifying cyber vulnerabilities which may or might exploit later down the road is kept under a scheduled structure.
Once the identifying process is complete, a risk manager analyses the occurrence. Also, giving coworkers data on the vulnerability and what kind of security issues it might pose.
In the cyber world, we define the risks by their type. It can be an acceptable risk or the priority risk. The acceptable risk is pre-determined, on which the organization or company has specialists positioned.
Another significant part of the post consists of a four-step process. They are treating the security controls by implementing security controls. Tolerating and making a decision for the long term and passing it on to the cybersecurity teams. Terminating the risk by entirely ending it and making sure the hole is covered so it doesn’t happen again. Lastly, the transfer protocol, on which a risk manager shares risk details with other parties.
If you put some thought into it and glimpse what we are trying to achieve, we will be in the same shoes. The process is essential, even though the result matters, a lot.
Risk Manager Career
Risk manager careers can differ from place to place. Employers might want the top officer in charge of maintaining the cyber team to work as the risk manager. Peer and subordinates include
- Cyber Risk Specialist
- Chief Information Officer
- Security Director
- Threat Intelligence Specialists
- Chief resilience officer
A degree in computer science or information security-related courses, along with certifications and years of experience, might land you the dream job you always wanted in cyber risk management. There is not enough talent to fill the void in cyberspace. It results in massive attacks, too strong for companies to handle. Thus, data loss, millions of dollars laundered online, and other complex threats occur.

On the flip side, it benefits a comfortable salary to manage expenses. Programmers who started early can benefit from their pre-gathered skills, putting them in an advantageous position for employment.
Glassdoor said the average salary for a cyber risk manager in 2022 could be $121,544/yr to $135,521/yr. ZipRecruiter reported an average of $105,574/yr or $51/hr. Comparably reported $199,550/yr U.S. average pay. As you can see, the field is full of opportunities and pays quite handsomely.
Let’s Recap
If you made it to this point, then we have nothing but gratitude and believe you can make it through the process of becoming a polished cyber risk manager in 2022. Among verities of job opportunities, the cyber market is one of the lucrative ones. It also guarantees a front-row seat on the cyber ongoings of the world.
We have a lot of articles regarding cybersecurity, courses, guides, how-to-tech articles to help you as much as possible in the journey.
Want to know about entry-level cyber security jobs and which are best to pursue? Check out this guide.
Have friends who could benefit from the information here? Feel free to hand them the link.

