In a digitalized world, cybercrime can take place from any direction. The ethical hacker insights report proves that fair and square.

Tens of thousands of ethical hackers band together to fight cybercrimes and help keep peace in cyberspace. Ethical hackers worldwide use their skills for the greater good as we speak. They are helping build a safer digital environment.
It became tough to keep the software, hardware, and data intact. Cyber terrors put the weakest links to the test in a world where information is the. Large organizations and enterprise bodies are also continuously suffering from cybercrimes. It is easy to say that there is not enough cyber talent to protect the global digital environment, and the current ones we have are doing their best and passing the nights sleepless.
The Ethical Hacker insights report reflects the current state of cybersecurity, provides a briefing on ethical hackers, the younger generation’s involvement, mentions some actual numbers, etc. The use of consecutive and singular moving examples throughout the article will help you see the enormous picture and better comprehend the ethical hacker insights report.
According to Infosecurity, where they have a community of 35,000 active hackers, a push for motivation is undoubtedly the key. Businesses often talk about faceless security specialists hunting for bugs on their browsers. Still, the ethical hacker insights report is more than that.
Due to the organization’s mistake of not giving proper security support, 32% of the occurrence gets missing from the log, and the weak links stay unbarred to damage.
History of Hacking
The ethical hacking scene has not always been what it is today. In fact, in prior times, ethical hacking was also considered a crime regarding how much safekeeping companies wanted for their data in papers. So regardless of the intent, it raised criminal charges against ethical hackers. Gradually, we understood that the laws and regulations we govern needed a reshape.
Lawmakers have the power to govern computer use and how ethical hacker’s skills are used. As the world marched forward, the hacking scene started to grow. However, clashing with authority figures who failed to understand the system had its toll. Decision-makers finally sought out the bright, intelligent young professionals who can do a lot to cover vulnerabilities.
Several news agencies reported the worrying jump in hacking attempts and vulnerabilities of particular companies. The history is a resembling reminder of how the scene changed for something better. According to HackerOne, 45% of the bug bounty programs are not only for tech companies but for other sectors.
Unveiling Ethical Hackers
The unveiling is quite interesting as it gives proper insight into where hackers are from, what motivates them and how they keep a line between good and evil. It is a topic that gains further interest as most of us interested in cyber security can resemble quite a bit.

Most ethical hackers tell us they tried to inform businesses about crucial vulnerabilities to no avail. Companies make a terrible mistake here. They get confused between good intentions and bad and spam it as negative interaction.
Vulnerability disclosure policy (VDP) is crucial, but due to insufficient routine, it becomes particularly apparent. A gradual build-up of an ethical hacker’s profile proves significant worth to companies. It offers them the transparency to trust them more. Taking in numbers, accepting external reports, and having a mindset to fight against cybercriminals validate VDP.
Hacker-powered security programs are increasing globally. Latin America had a 41% growth over the previous year. On the contrary, the federal government sector grew 214%. A significant margin if we all can agree.
In the past year, HackerOne paid out 511 individuals bounties of $10,000 in the critical security sector, which increased four times from the year before. Vulnerability bounty increased nearly 50% in just a year, even though many companies prefer to pay as low as possible and gain as much in return.
Critical Learnings for Ethical Hacker Insights Report
86% of hackers believe they should report a vulnerability and notify the company instead of making money. Another 55% agree that their professionalism should serve better in the tech world.
The idea of crowdsourcing ethical hacking is a great motive. It motivates individuals to carry on learning and do good for the world. On the other hand, finding vulnerabilities becomes a much slower process where targeted attacks are practiced.
Lawmakers today are introducing newer legislation to drive hacker-powered security. US, India, and Canada have some of the top earners in hacking. Over 50 hackers earned more than $100,000 in the previous year, and half a dozen suppressed $1 million in total rewards.
The European Commission (E.U.), U.K.’s National Cyber Security Center, Singapore’s Ministry of Defence, U.S. Department of Defence, Marine Corps, and the Air Force also utilizes ethical hackers for defense and strengthening critical points.
According to the Hacker-Powered security report 2019, a vulnerability is discovered every five minutes. Every 60 seconds, a hacker partners with their organization. It is at least 1,000 interactions each day. The HackerOne community has more than 450,000 registered hackers who constantly look for vulnerabilities missed by standard defense protocol. 90% of them are under 35, reflecting how young the community is. They play a crucial role for organizations of all types.
Ethical Hacker Insights Report by Geography
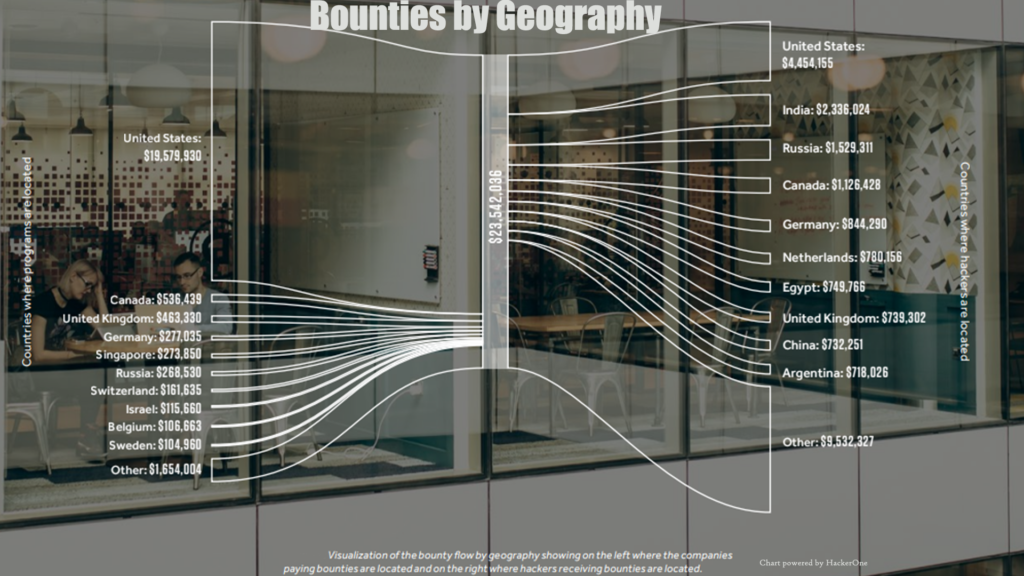
Each year, the hacker-powered security programs are growing. Each region is spectating at least 30% growth. Latin America is in the lead with 41%, North America (34%), EMEA (32%), and APAC (30%) are in the following. US-based organizations pay about 83% of all hacker bounties around the globe, and the stats are pretty similar to last year. In 2017, U.S. hackers earned 19% of all rewards, followed by India (10%), Canada (5%), and Germany (4%). In Canada, the growth margin was a staggering 148%.
Ethical Hacker Insights Report by Industry
The bug bounty and adoption program also changed with industry growth. Tech adoption calls for improvement fifth year in a row where almost all industry types have joined the venture. The federal government seems to have the most significant year-over-year growth at 214%, followed by automotive (113%), telecom (91%), consumer goods (64%), crypto & blackchin (64%).
Also, 60% of bug bounty programs are limited to technology companies. In contrast, internet services, software, financial services, and media make up for the rest. It is truly a fascinating time to spectate the growth of ethical hacking.
Recent ransomware attacks also inspired growth for local government. Ransomware attacks became critical threats in Texas, Baltimore, Atlanta, Utha, and Lake City, Florida. Security operations are carrying a heavy load to protect critical infrastructures.
See also:
- 10 Best Cyber Security Schools in 2022
- 30 Best Cyber Security Master’s Degree Programs in 2022
- Gray Hat Hackers and Why They Stand Out
- How To Get Into Cyber Security For Beginners
- How to become a Digital Forensic Expert: Reversing Cyber Threats
Jeff Massaimilla, chief cybersecurity officer at General Motors (G.M.), said, “To improve the security of their connected systems, every corporation should have a vulnerability disclosure policy that allows them to receive security submissions from the outside world.”
On the contrary, the U.S. Department of Justice former Deputy Attorney General Rod J. Rosenstein briefed, “All companies should consider promulgating a vulnerability disclosure policy, a public invitation for white hat security researchers to report vulnerabilities. The U.S. Department of Defense runs such a program. It has been very successful in finding and solving problems before they turn into crises.”
Conclusion
As the world evolves towards more advanced tech, cyber threats are growing. Today we see too many automated threats which are more advanced than manual ones used before. Through proper ethical hacking channels, empowering businesses and organizations should get the priority it deserves. Even though skill shortage and budget constrain remain, we ought to make the best of it.
On the bright side, more and more companies are seeking help from ethical hacking communities as a means of support.
Individuals new to the cybersecurity concept and who want to learn more should benefit from the previously provided links for a career in ethical hacking and getting into cyberspace properly.
Businesses and organizations that are still stranger to the ethical hacking community should seek out the current and up-and-coming generation of information security talent to keep their digital assets safe.
Feel free to spread the information on your social.

