Looking to find out exactly what the CISM is and are trying to see if you should get it or go after the CISSP instead? Hopefully this post will help you get better incite in to what exactly the CISM is vs the CISSP. Information Systems Audit and Control Association (ISACA) offers Certified Information Security Manager (CISM) certification to the security professionals, capable of aligning the information security with the business objectives of the organizations. CISM holders mostly take care of the Information security matters of the organizations from management perspectives, such as developing and overseeing the security policies, standards, and best practices. The certification is considered a global standard of achievement for the individuals working on the managerial positions in information security departments. Also, if you want to see the same information about the CISSP you can see that post here.
CISM Fast Facts
- Introduced in 2002
- Globally accepted standard of achievement
- Accredited by ANSI under ISO/IEC 17024:2012
- Named among top security certifications
- More than 30,000 CISM credential holders worldwide
Who Should Earn CISM Certification
CISM certification ensures that the individuals have a profound understanding of the Information security and the business objectives. The enterprises and organizations look for professionals who can design effective information security strategies, policies standards, and procedures. CISM holders are highly regarded for such key positions as CISM validates the following capabilities of the individuals.
- How to approach the IT security of the organizations more from a business perspective than IT perspective.
- Deep understanding of the industry-specific regulations, the emerging risk, and the ability to manage risk.
CISM suits the individuals working or looking for the following key jobs in the industry.
- Information security managers.
- Chief information officers
- Information security consultants.
- Information Technology (IT) consultants.
What is CISM Eligibility Criteria
CISM requires at least five years of information security work experience with a minimum of three years of work experience in the field of information security management. The three years’ experience must be in three or all four domains included in the job practice analysis areas of ISACA. The job practice analysis areas include the following four domains.
- Information Risk Management.
- Information Security Governance.
- Information Security Incident Management.
- Information Security Program Development and Management.
The individuals can use the following credentials as substitution of two years’ work experience.
- CISA (Certified Information Systems Auditor) Certification.
- CISSP (Certified Information Systems Professional) certification.
- A post graduate degree in the field of Information Security, Information Systems, and Information Assurance or similar.
- Four years of university experience teaching the information security management
Similarly, the following credentials and documents can be submitted as one year experience substitution.
- Global Information Assurance Certification (GIAC) by SANS.
- Disaster Recovery Institute Certified Business Continuity Professional (CBCP).
- CompTIA Security + Certification.
- Microsoft Certified Systems Engineer (MCSE).
- Information Systems management experience (one year)
- General security management work experience (one year)
- Two years of university experience teaching the information security management.
Note: The above substitutions do not satisfy the three years Information Security management work experience requirement.
CISM Exam Criteria
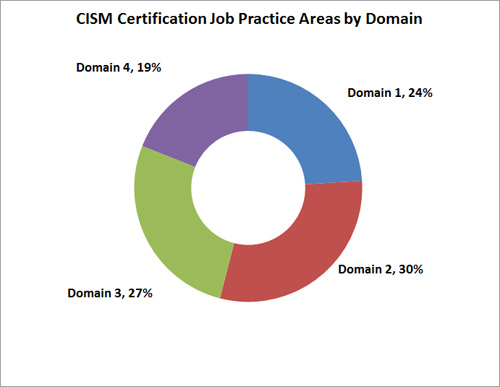
The current CISM exam format consists of 150 multiple choice questions to be solved in 4 hours. Following is a brief overview of ISACA’s domains covered in the exam.
Domain-1 Information Security Governance (24%)
The current CISM exam contains 24% questions about information security governance. The information security governance domain tests the capabilities of the individuals to design and maintain the information security strategies that must align with the goals and objectives of the organizations. The candidate must be able to develop and maintain effective security policies, standards, procedures, and guidelines aligned with the organizations’ business. The following information security governance domain knowledge can help in achieving the aforesaid job tasks.
- Knowledge of different techniques helpful in devising the robust information security strategies. Examples include SWOT (Strengths, Weaknesses, Opportunities, Threats).
- Knowledge of information security from business point of view i-e knowledge of functions, procedures, and practices that can be used to align the information security with the business model of the organizations.
- Deep knowledge of different information security governance frameworks.
- Knowledge of organizational information security policy development factors, such as organizations’ structure, culture, risk tolerance, and regulations.
- Knowledge of the factors that can influence the enterprises’ business goals, e.g emerging technologies, social media, third-party impact etc.
- Knowledge of interpreting and utilizing information security metrics like Key Risk Indicators (KRIs) and Key Performance Indicators (KPIs).
Domain-2 Information Risk Management (30%)
The 30% questions in the CISM exam comprise of knowledge about Information risk management. Information risk management domain validates the candidates’ abilities to assess risk and vulnerabilities, analyze the ongoing threats, and recommend or implement the appropriate measures to avoid, mitigate or transfer the risk completely. The candidate reports the potential impact of assessed risk on the organizational goals with the senior management to develop an understanding at different management levels. The following domain knowledge is required to perform the important tasks that fall in the information risk management category.
- Knowledge of information vulnerabilities, threats, and their evolving nature.
- Knowledge of methodologies used for risk assessment and threat analysis.
- Knowledge of the methods used in prioritizing the threats and response options.
- The candidate should know how to design a classification model for information asset that must align with the business objectives.
- The individuals must have the knowledge of information security controls, risk treatment options (whether to accept, avid, mitigate, or transfer the risk), and cost/benefit analysis.
- Knowledge about how to integrate the information security risk management techniques into processes, procedures, and policies of the organizations.
Domain-3 Information Security Program Development and Management (27%)
Information security Program Development and Management (ISPDM) domain contributes 27% in the CISM exam. The ISPDM domain shows the strength of the candidates in developing and maintaining the Information Security programs. These programs identify, manage, and protect the assets of the organizations and enterprises while staying aligned with the information security strategies and business goals. The individuals working in the ISPDM domain possess the following domain knowledge.
- Knowledge of recognized standards, best practices, and frameworks used for developing and managing the information security programs.
- Knowledge of methods used in aligning the information security programs with other business tasks.
- Knowledge of methods used for identifying, acquiring, and managing the internal and external resources’ requirements.
- Knowledge of methods used for integrating the information security requirements into processes like change management, access management, and audit processes.
- Knowledge of designing and testing the information security controls’ effectiveness.
- Knowledge of methods used for incorporating the information security requirements into legal documents like contracts and agreements.
Domain-4 Information Security Incident Management (19%)
The 19% CISM exam portion contains questions about information security incident management. The information security incident management domain evaluates the candidates’ skills of detecting, investigation, responding to, and recovering from information security incidents. The following domain knowledge is required to perform information security incident management tasks.
- Knowledge of incident management best practices.
- Knowledge of incident response plans, Disaster Recovery Plans (DRPs), Business Continuity Plans (BCPs), and the relationship of incident response plans with the later (DRPs and BCPs).
- Knowledge of methods used for incidents containment to minimize the impacts.
- Knowledge of the resources that can be used to detect, log, analyze, investigate, and document the security incidents.
- Knowledge of the incident response testing techniques, and metrics to evaluate their performance.
Note: Above is a general overview of the job responsibilities and the desired domain knowledge to accomplish those tasks. The tasks and knowledge statements can be found in detail on the official ISACA platform.
CISM Renewal
CISM is renewed after a period of three years. The CISM holders must submit annual reports with 20 Continuing Professional Education (CPE) credits. A 50 minutes CPE activity is considered as 1 hour CPE credit. A total of 120 CPE credits are required over a period of 3 years. Following are some options for earning CPE credits.
- Attending the seminars, conferences, workshops, and chapters organized by ISACA.
- Attending the seminars, conferences, and workshops organized by recognized organizations other than ISACA.
- Self-study courses.