Our communication infrastructure, industries, businesses, and even our lifestyle are dependent on the internet. There are around 4.57 billion people who use the internet today. The internet uses and benefits are countless. Search engines like Google, Bing, and Yahoo provide billions of online resources to help people in their quest. However, these resources are merely 5% of the total internet. 95% of internet resources are not accessible through ordinary search results. Such resources either require privileged accounts or special browsers for access. These internet resources are termed as the deep and dark web. In this article, we will explore the dark web; how it is different from the deep web; common examples, and how the dark web can help in threat intelligence.
WHAT IS DARK WEB?
The dark web is the dark or hidden part of the internet that does not appear in search engines like Google, Yahoo, and Bing. Special proxy software like Tor-browser can be used to access. The sites have usually nonsensical format with .onion extension. The Tor-browser helps users explore these domains anonymously. Some resources have only IP addresses instead of gibberish strings.
DARK WEB VS DEEP WEB
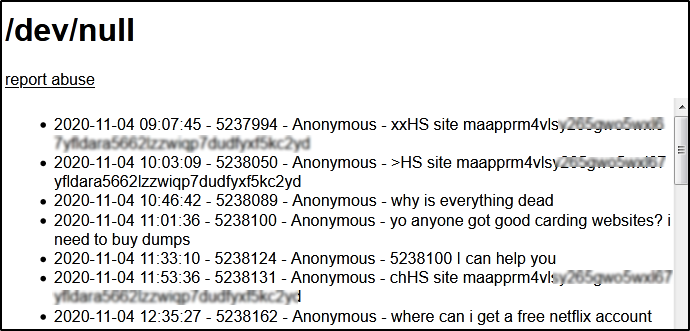
Many people confuse the term ‘dark web’ with the ‘deep web’. In reality, both are different. The term ‘deep web’ is a broader concept. Anything that is online but not accessible through common search results comes under the domain of ‘deep web’. The content of personal emails, social media private messages, and membership forums are a few examples of the deep web. The deep web content may not require Tor like browser to access the resources. The term ‘dark web’ is a subdomain or subset of the deep web hosting resources that are mainly used for criminal activities. People use the dark web mostly for illicit goals, such as buying, selling, or sharing stolen credit cards, emails, sensitive business records, private information, drugs, counterfeit money, etc. It is also unfair to attribute all the resources as unlawful or forbidden. There are many resources that are worth exploring.
DARK WEB EXAMPLES
Since the common search engines do not help with the content, there are specific search engines, forums, and services that can be used to explore the content or become part of the dark web using the Tor-like services. Though there are a number of illicit platforms that can be shared as examples, we are going to share only grey-list examples to understand the dark-web concept.
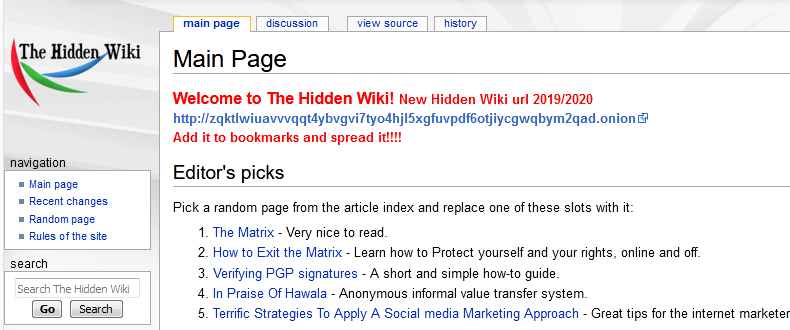
Hidden Wiki:
Dark Web Link: http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion/wiki/index.php/Main_Page
Hidden Wiki is also known as the Wikipedia of the dark web. The site provides links to a number of resources using the aforementioned link. The Hidden Wiki can also be used to search third-party hosted material. The users are advised to avoid clicking on any suspicious or irrelevant links gathered through the Hidden Wiki since the platform does not block dangerous resources from appearing in the results.
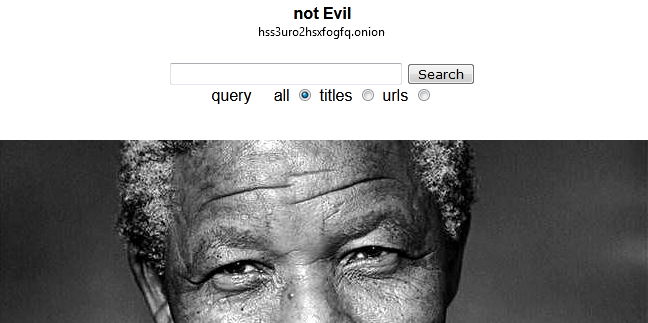
Not Evil:
Dark Web Link: http://hss3uro2hsxfogfq.onion
Not Evil is a popular search engine. Although it discourages unlawful content, some illicit sites still manage to get indexed in the search results.
The Not Evil search engine also hosts a chat feature where users can participate in ongoing chats or create new discussion topics.
Although the users are anonymous, it is believed that the chat participants are mostly hackers, scammers, and people from law enforcement agencies.
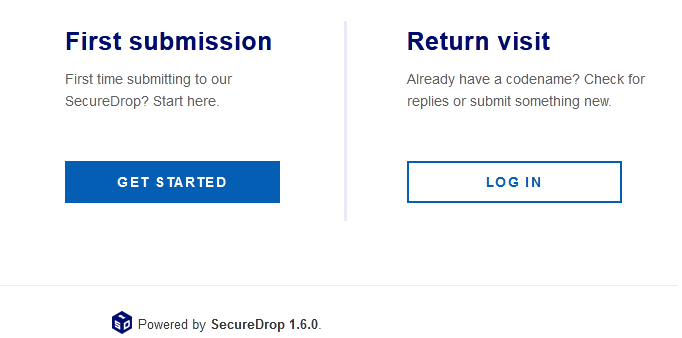
Secure Drop:
Dark Web Link: http://secrdrop5wyphb5x.onion/
Secure Drop is another dark web’s useful platform where people share classified news or information with others. The platform provides a safe environment for whistleblowers who want to share information or break news with journalists. Some popular magazines like Forbes and Reuters have their own Secure Drop URLs for similar purposes.
Forbes Secure Drop: http://t5pv5o4t6jyjilp6.onion/
Reuters Secure Drop: http://smb7p276iht3i2fj.onion/
ProtonMail:
Dark Web Link: https://protonirockerxow.onion/
ProtonMail is considered one of the most secure email services. It uses end-to-end encryption without logging any information to keep the communication secure. There is no need to share any personal data while creating a ProtonMail account.
HOW TO USE DARK WEB FOR THREAT INTELLIGENCE
The dark web is known for selling compromised data and illegal stuff online. Tokopedia, Homechef, Minted, and Styelshare are a few of the recent data breach examples with millions of records for sale. On the other hand, the dark web also provides an opportunity for researchers to expose critical Cyber-breaches. The following threat intelligence methodologies can greatly help organizations securing their business assets and improving the overall cybersecurity posture.
INVESTIGATING SALES OFFERS ON DARK WEB
A common approach to threat intelligence is to find potential sites and narrow down the search to get meaningful or actionable threat intelligence. The researchers should look for the following trade opportunities to unearth or hunt down the business-related cybercriminal activities.
1) Credentials and Access Trades: Passwords sales and privileged access deals are common. Cybersecurity professionals can look for the names or links related to the subject organization. If the name or links appear in dark web search results, the investigators can further refine the search process to see if the business-related secret credentials or access mechanisms are up for sale by the adversaries. Any compromised accounts or access mechanisms should be immediately blocked and rectified to cut down unauthorized access to the organization’s resources or services.
2) Potential Vulnerabilities Trades: Not all hackers offer access methods or secret credentials. Some adversaries sell the existing or zero-day vulnerabilities and leave the exploitation headache to the potential buyers. The professionals can spot such flaws through the dark web and apply immediate patching before someone else exploits such vulnerabilities.
APPLY DARK WEB SCANNERS
Extracting relevant data manually from the ‘dark sites’ is not an easy task. There is a variety of data to search in multiple dark web platforms. Web monitoring tools can scan the dark web sources to identify and mitigate potential Cyber-risk. An efficient dark web monitoring tool or service should be able to gather, identify, interpret, or analyze the following type of information available on the dark web.
- Accounts-related information (Usernames, social security numbers, phone numbers, email addresses, passwords, etc.
- Business-related information (domain-names, brand names, documents, plans, internal memos, etc.)
DEPLOY NETWORK MONITORING TOOLS
Network monitoring tools can be useful in identifying dark web traffic. Since Tor is the major browsing source, the intelligent monitoring tools can generate alerts for the traffic originating from Tor entry or exit points. A further investigation of the suspicious traffic can help the network administrators to take necessary security-related actions.
CONCLUSION
The dark web is the netherworld of the internet. The majority of activities and resources are unlawful. However, it is also a source of finding Cybersecurity flaws and data breaches. Referring to the dark web to discover security vulnerabilities and compromised data is sometimes more rewarding than relying on traditional Cybersecurity tools and vulnerabilities assessment approaches.