Wifi-Pumpkin is an open source framework that can simulate wifi attacks by creating fake wireless networks. The framework is capable of analyzing the traffic passing through these fake networks. The types of attacks that can be launched with Wifi-Pumpkin include Rogue Access Points, ARP Poisoning, phishing attack, Windows update attack, DNS proxy attack, de-authentication attack, image capturing, Wifi Probe request, and DHCP starvation. Wifi-Pumpkin has built-in modules to launch these attacks.
Wifi-Pumpkin Installation
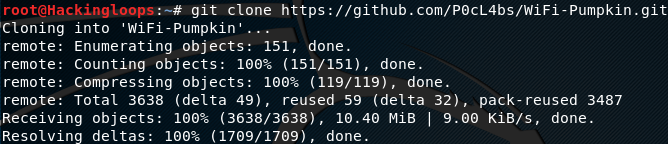
Wifi-Pumpkin is a python tool that has been tested with Kali Linux, WifiSlax, Ubuntu, Pentoo, and Parrot OS. The tool requires at least python 2.7 to run. In order to install Wifi-Pumpkin, clone the tool from Github using the following repository link.
git clone https://github.com/P0cL4bs/WiFi-Pumpkin.git
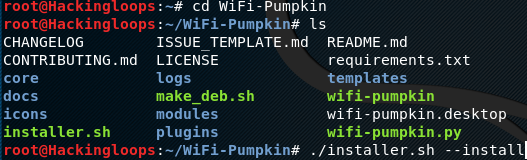
Move on to the Wifi-Pumpkin directory to install the tool as follows.
cd WiFi-Pumpkin chmod +x installer.sh sudo ./installer.sh --install
How Wifi-Pumpkin Works
Wifi-Pumpkin is a GUI framework that comes into view by typing the following command in the terminal.
wifi-pumpkin
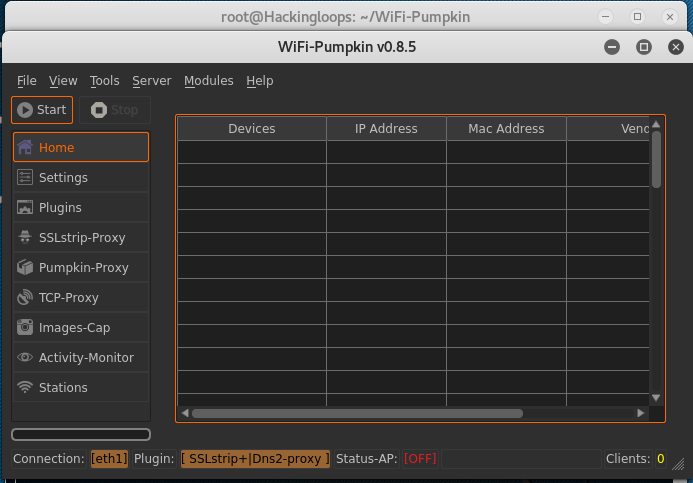
The command opens up the Wifi-Pumpkin GUI. Wifi-Pumpkin interface is populated with different options as shown in the following screenshot.
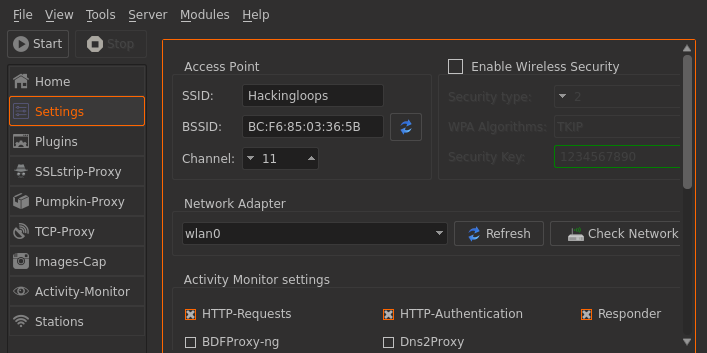
In order to use Wifi-Pumpkin as rogue Access Point, we need to create one by configuring the framework using the settings tab from the interface. The setting options are divided into different sections, such as Access Point (AP) setting, wireless security setting, network adopter setting, activity monitor setting, and DHCP setting. In the AP section, enter the desired name as a Service Set Identifier (SSID). Users in the vicinity see this SSID as an Access Point to connect.
The Wireless security section allows enabling or disabling the security key for the Access Point. In most cases, this option is kept unchecked in order to allow anyone to connect to the Access Point. The network adopter section shows all the available network adopters to use. It is important to note here that Wifi-Pumpkin requires both, Ethernet cable and Wifi adopter to operate. Activity Monitor setting offers options like server responses, HTTP-requests, and HTTP-authentication features. The Activity Monitor utility captures the traffic based on these settings.
The final section in the settings tab is the DHCP setting. It allows IP class selection, lease options, IP range, and broad casting settings.
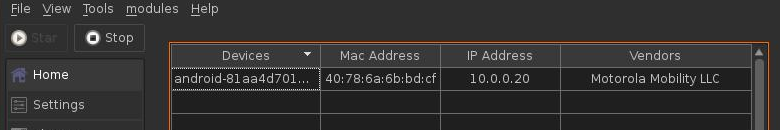
Once the framework is configured, click the start button on the interface in order to start broadcasting the rogue Access Point. The details about the connected devices to the rogue AP can be seen in the Home section as shown in the following screenshot.
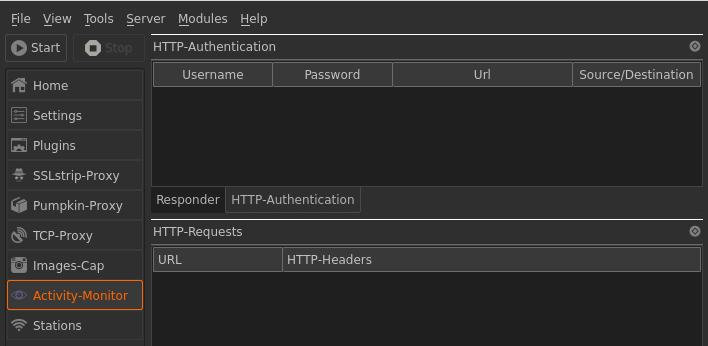
The users’ activity can be monitored in the Activity Monitor window. Wifi-Pumpkin can steal and record the sensitive information like login credentials in the Activity Monitor section.
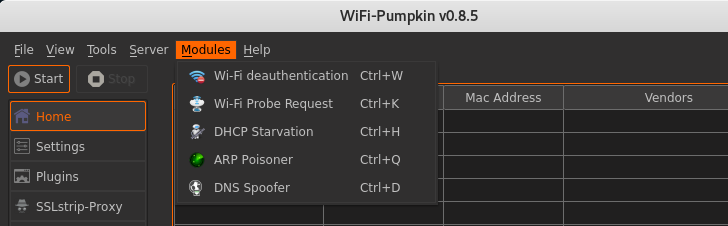
Besides, stealing credentials through rogue Access Points, Wifi-Pumpkin can be used to launch other aforementioned attacks through the available modules as shown in the following screenshot.
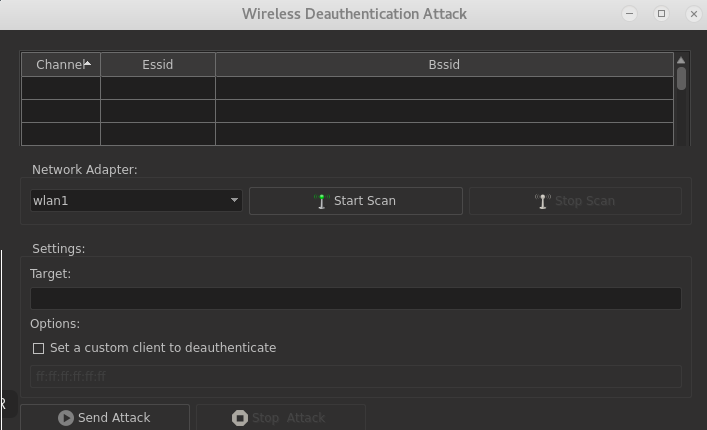
Selecting the desired module loads the attack options associated with the selected module. For instance, if we select the Wifi-deauthentication module from the list, the deauthentication attack options pop up on the screen, as shown in the following screenshot.
Starting the deauthentication attack against the selected target device disconnects the victim from the legitimate Access Point. The attack is useful in scenarios where the goal is to capture the wifi security keys of other wireless networks by creating evil twin access points. The users, after getting de-authenticated, are forced to enter the wifi keys before they are redirected to the legitimate wifi networks.
Conclusion
Wifi-Pumpkin is a decent framework that can simulate different wireless network attacks during the penetration testing. Such attacks are useful in analyzing the users’ behavior in organizations with strict internet connectivity policies.