XSStrike is a web applications penetration testing tool used for detecting Cross Site Scripting (XSS) vulnerabilities. The vulnerabilities analyzed by XSStrike include Reflected and Document Object Model (DOM) based XSS vulnerabilities. There are four backend functions that run XSStrike. These include parsers, payloads generator, fuzzing engine, and crawler. In order to launch an XSS attack on the target web application, the tool first does analysis of the target web application through custom HTML and JavaScript parsers. The payloads are then generated according to the response of the target web application. The fuzzing engine helps in crafting the best working payloads by aiding the context analysis of the target web application. If the target web application is vulnerable to DOM or reflected XSS attacks, the results are displayed along with the number of reflections and payloads information.
XSStrike Installation
XSStrike is a Python tool that requires the following packages to operate. The current version is supported by Python 3 and requires PIP3 to install the dependencies.
python-Levenshtein
prettytable
requests
tld
fuzzywuzzy
The fuzzywuzzy, requests, and tld packages can be installed by running the requirements.txt file from XSStrike directory. Rest of the two packages can be installed manually as follows.
pip3 install python-levenshtein
pip3 install prettytable
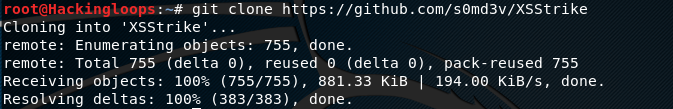
After installing the prettyyable and levenshtein algorithm package, clone XSStrike from Github using the following path.
git clone https://github.com/s0md3v/XSStrike
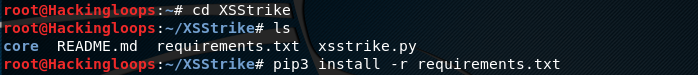
Move to the XSStrike directory to run the requirements.txt file in order to install the remaining above mentioned dependencies.
cd XSStrike Pip3 install –r requirements.txt
This completes the installation process
How XSStrike Operates
The following command executes XSStrike.
Python3 xsstrike.py
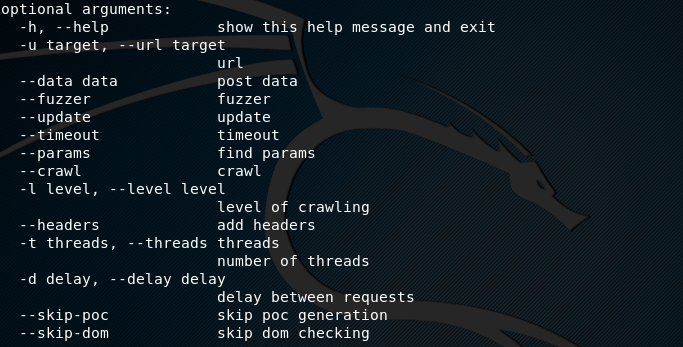
The help command displays all the available arguments that can be used during XSS scanning.
python3 xssstrike.py –h
DOM XSS Vulnerability Scan Example
XSStrike requires the following syntax and information to find out the XSS vulnerabilities in target web application.
python3 xsstrike.py –u <target web application>
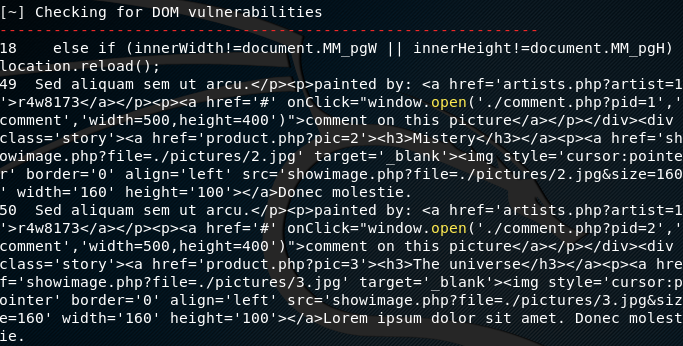
For instance, if we run XSStrike on a test web application, the tool searches for both, DOM and reflected XSS vulnerabilities, starting with DOM XSS.
python3 xsstrike.py –u http://testphp.vulnweb.com/listproducts.php?cat=1
The tool first searches for DOM XSS vulnerabilities in the associated nodes of the target web application. DOM is an interface that treats a web document as a tree structure with different nodes, where each node represents part of the document. If any vulnerability is found, it is displayed in the results.
Reflected XSS Vulnerability Example
If we scan the following locally hosted test web application, XSStrike send queries to find out if the target web application is potentially vulnerable to XSS attacks.
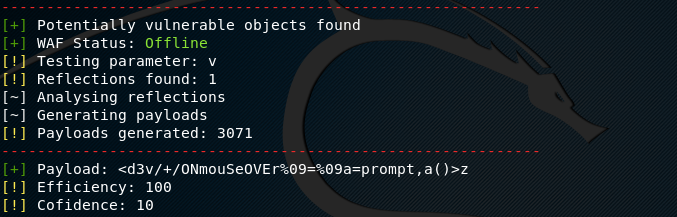
python3 xsstrike.py –u http://127.0.0.1/?v=2
The tool tests the parameters in the target web application and finds out the total number of reflections. After completing the context analysis, XSStrike generates the payloads and sends to the target web application to confirm the reflected XSS vulnerability. The working payload and its efficiency are also mentioned in the final results.
Conclusion
Reflected and DOM based XSS attacks are very critical in web applications. XSStrike has the tendency to find out both types of XSS vulnerabilities during the penetration testing process. The tool has some exciting features including multi-threaded crawling, Web Application Firewall (WAF) detection, WAF evasion, context analysis, handmade HTML and Java parsers, configurable core, and full HTTP support.