Vega is a GUI based open source tool used for analyzing vulnerabilities in web applications. The tool has two main functionalities i-e Scanner and Proxy. The scanner automatically fetches links from web applications to test the vulnerabilities. Vega uses two types of modules to perform the vulnerabilities assessment. These are called Injection modules and Response processing modules. The Injection modules include blind SQL injection, XML injection, HTTP trace probes, Local File Inclusion (LFI), Remote File Inclusion (RFI), Shell injection checks, HTTP header injection, OS command injection, blind XPath injection, Eval code injection, Cross Site Scripting (XSS) injection, Integer overflow, and Format string injection checks. Similarly, the Response processing modules contain Emails finder, Directory listing detector, insecure script identifier, cookie security module, Path disclosure check, HTTP Header check, File upload detection module, X-Frame Options Header analyzer, internal IP addresses lookup utility, Feed detection, Social security number (insurance number) detector, Form autocomplete checker, source code disclosure module, cookies scope detection, and empty response body module. Vega allows selecting the desired modules from the available lists to perform targeted penetration testing. The proxy feature allows Vega tool to intercept the browser’s request to the target web application server and the web server’s response.
Vega Installation
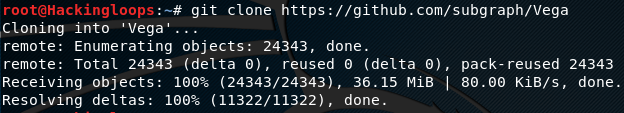
Vega is a Java tool that runs on Linux, OS X, and Windows operating systems. Vega source code can be cloned from Github repository. Before cloning the tool, install the Vega dependency using the following command.
sudo apt-get install libwebkitgtk-1.0
After installing the above package, clone Vega using the following command.
git clone https://github.com/subgraph/Vega
Vega Interface
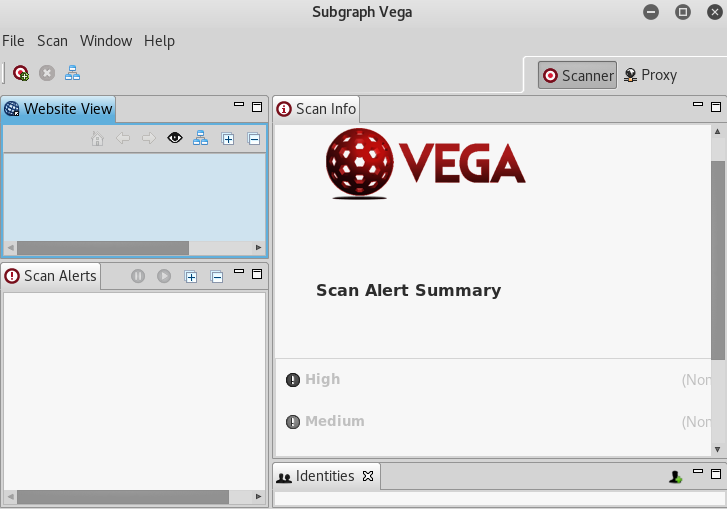
The following command opens Vega interface as shown in the following screenshot.
vega
Vega interface is divided into three sections. The top left section is called the Website View. It contains the domains and associated links that undergo the scanning process. Under the Website View section is the Scan Alerts section. It contains the list of vulnerable links found during the entire scanning process. The right sidebar, called Scan Info, shows the scanning progress and the number of vulnerabilities, divided into three categories, namely High, medium, and low. Scanner and Proxy tabs can be seen on the top right corner of the interface. Scanner is the default interface of Vega. However, we can switch between both by clicking the desired option.
How Vega Works
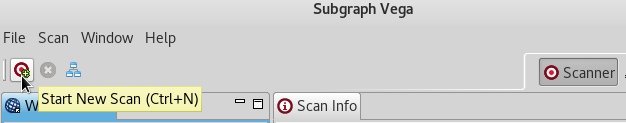
In order to scan a target web application, click on the Add button as shown in the following screenshot.
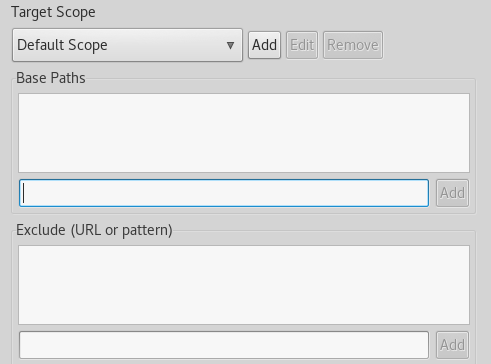
A window pops up with the target web application and target scope options. Enter the web address of the target application in the first field. The target scope option can be ignored at this stage. However, it is recommended to configure the scope as it allows setting base urls to refine the scanning process. Target scope also allows avoiding certain urls or paths during the application scanning.
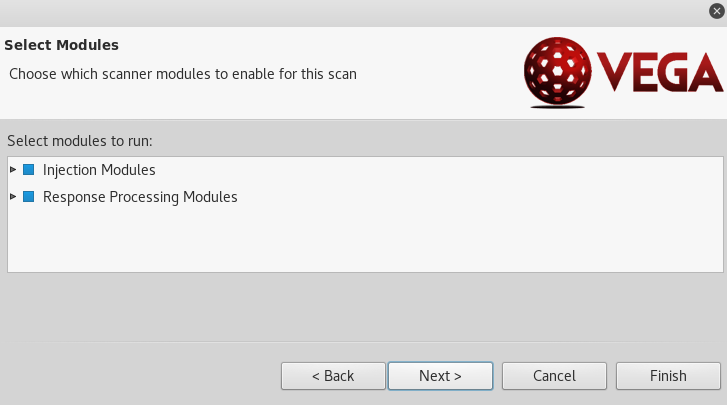
In the next step, select the desired modules from the Injection and Response modules categories. Both categories contain a number of modules as discussed earlier.
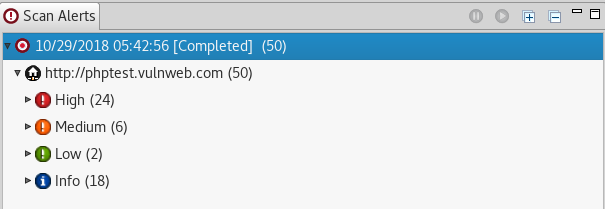
Once configured, Vega starts scanning the target web application according to the selected scanning modules. The details about the vulnerable links can be seen in the Alerts section, as shown in the following screenshot.
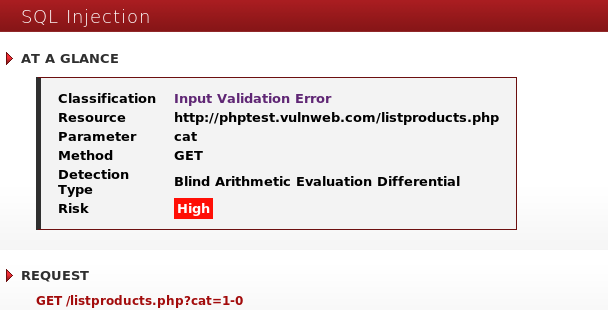
By clicking each link, the tool displays the details about the potential vulnerabilities. For example, if we click on link that is potentially vulnerable to SQL injection, the tool shows the parameters and the request method that can be used to exploit the vulnerability.
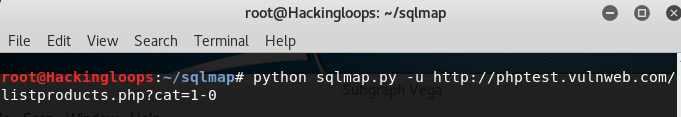
We can verify the vulnerability by testing the suspected link and parameter in another tool (e.g sqlmap).
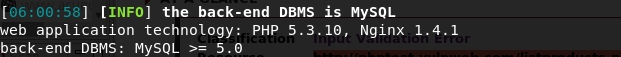
The vulnerability is verified by sqlmap, as we can see the database is detected in the following screenshot.
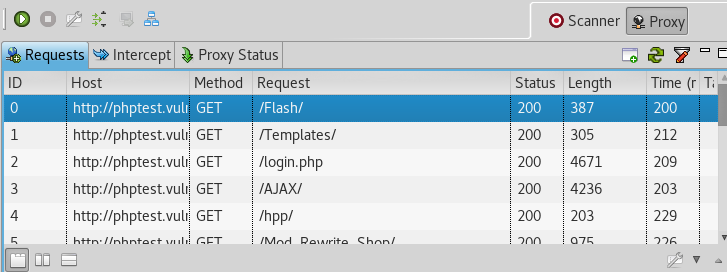
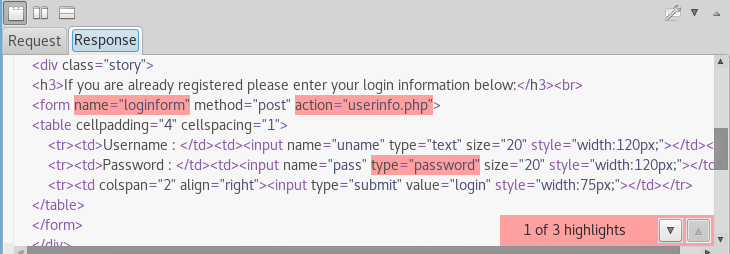
The same approach can be applied to the other vulnerabilities found by Vega tool. Apart from scanning feature, Vega can be used to record the request and response messages using the proxy feature. The proxy feature records request and response messages along with the status codes as shown below.
Summary
Vega is a simple to use GUI scanner that can detect high level vulnerabilities in web applications automatically. The tweaking options like target scope reduce the number of false positives to a great extent.