
How to Perform Malware Analysis Without Code Execution?
Securing networks and individual computing devices is a challenging task. We see a number of hardware and software based security

Securing networks and individual computing devices is a challenging task. We see a number of hardware and software based security
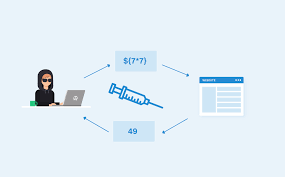
In this article, we will be going through how rendering engines can be vulnerable and give access to the system.

After gaining initial access to the systems, many attackers face the problem of having low privileges over the system. This

This video shows you step by step how hackers create pharming malware on Linux and will show you what you