Securing networks and individual computing devices is a challenging task. We see a number of hardware and software based security solutions used to detect and prevent cyber-attacks. Firewalls, Intrusion Detection Systems (IDS), Intrusion Prevention System (IPS), Antivirus (AV), etc. are some common security practices adopted to ensure the security of digital assets. Despite the use of security tools and strategies, attackers manage to penetrate networks and devices using malicious software (malware). Cybersecurity experts capture these malwares and analyze them in order understand their behavior and know the intentions of malware creators. This practice is commonly known as malware analysis. There are two main types of malware analysis namely static and dynamic analysis. In this tutorial, we will explain static malware analysis through practical examples by using different static malware analysis tools.
Static Malware Analysis
Static malware analysis is a process of analyzing malware without execution. There are different ways to perform static malware analysis. The most common method is the signature-based malware analysis. This practice is commonly used by AV solutions. AV developers create signatures of different malware and load them into AV database. When AV solutions encounter suspicious files, they create file signatures and compare the results with the existing signatures record. If there is a match, the AV solutions mark the suspicious file as malware. VirusTotal is one such example of static malware analysis repository where security researchers upload the suspicious files/URLs to see if they are classified as malware by different Antivirus tools.
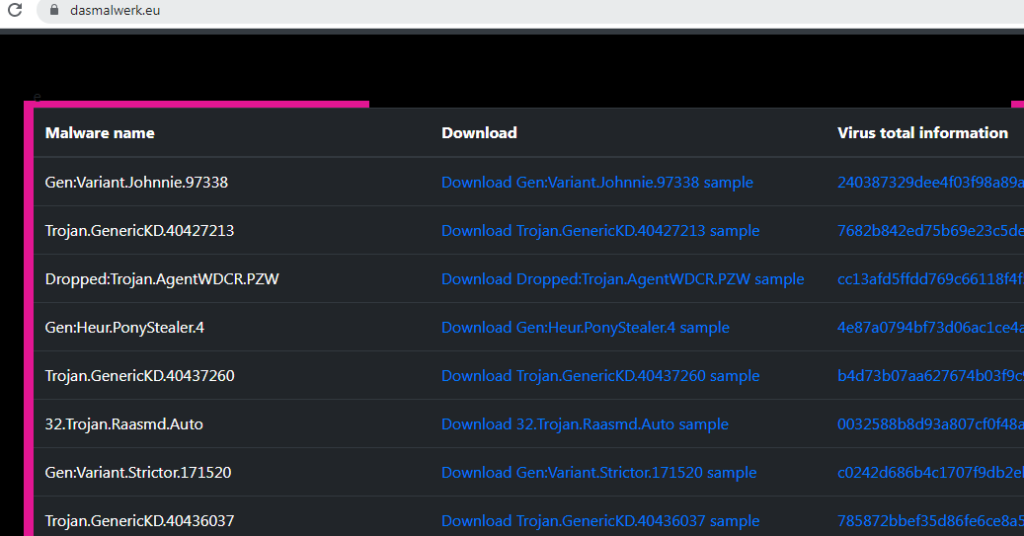
We can demonstrate the signature-based analysis by downloading a live malware artifact in a Virtual Machine (VM). In this tutorial, we use Windows 7 virtual machine running in Virtual Box. There are multiple malware samples available online at different servers. Dasmalwarek.eu is one such malware repository that allows downloading malware for educational purpose. If we open Dasmalwarek.eu web page, we see a list of malware with download links.
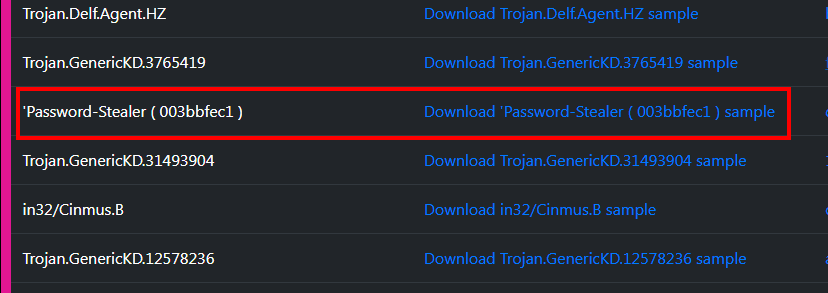
We can download any malware to perform the analysis. For this tutorial, we download Password stealer malware sample as shown in the following screenshot.
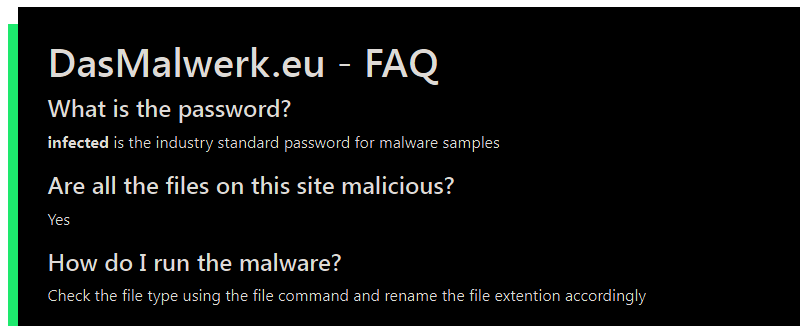
The downloaded artifact is a password protected Zip file. The password (password: infected) is mentioned in the FAQ section of Dasmalwarek server.
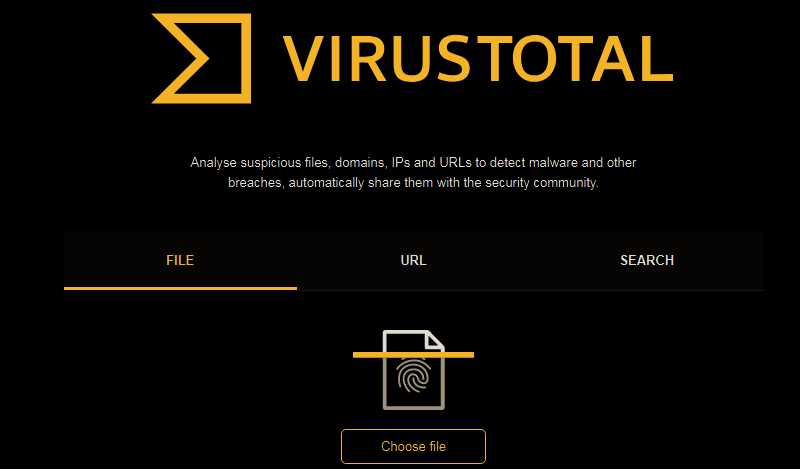
After extracting the malware sample, open the Virustotal using the following link.
https://www.virustotal.com/gui/home/upload
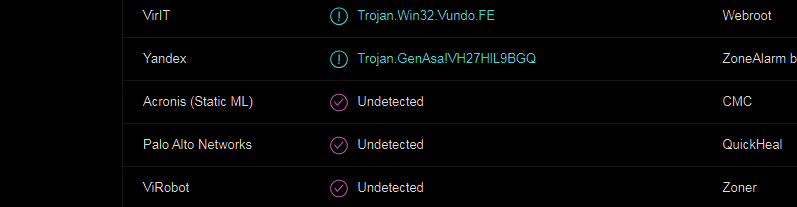
Upload the sample malware file to the Virustotal and wait for the results. As we can see in the following screenshot, a large number of Antivirus solutions detected the sample file as malware.

It is also important to note that some Antivirus tools did not declare the sample file as malicious. This is due to non-availability of malware signature in their database. At this stage, we can conclude that signature based static malware analysis is not enough.
The other important static malware analysis option is to pierce the malware file and explore its code. As we know the malware code is a set of instructions that may contain libraries, function calls, IP addresses, URLs, email addresses, and a lot of other interesting information. From libraries, we can guess the functionality of the malware without executing it practically. The function calls can tell us the malicious intent of the malware developer. The IP address and URLs can give a hint about the bad server or command and control center of the malware. Similarly, the IP address can be the destination server where malware wants to send the data. To see the malware code, we require a tool that can extract the malware code. The Microsoft Sysinternals suite offers a tool called Strings that can be used for this purpose. The tool can be downloaded from the following link.
https:// learn. microsoft. com/en-us/sysinternals/downloads/strings
After downloading, unzip and place the Strings executablefile in Windows’ System32 folder.
C:\Windows\System32
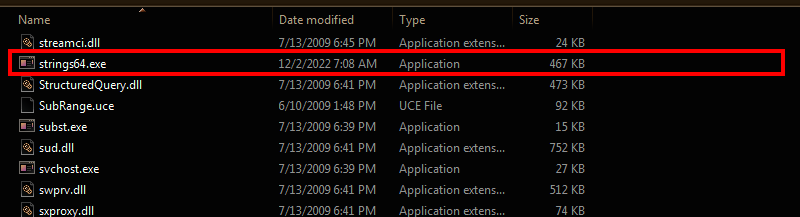
Note: There are two main Strings files (Strings.exe and Strings64.exe) in the downloaded folder. We have placed the Strings64.exe file since we are working in 64 bit Windows operating system. Now we can open the command prompt and run the Strings tool by typing the following command.
strings64
The command prompt executes the Strings tool and displays all the parameters that can be used during the static analysis of malware sample.
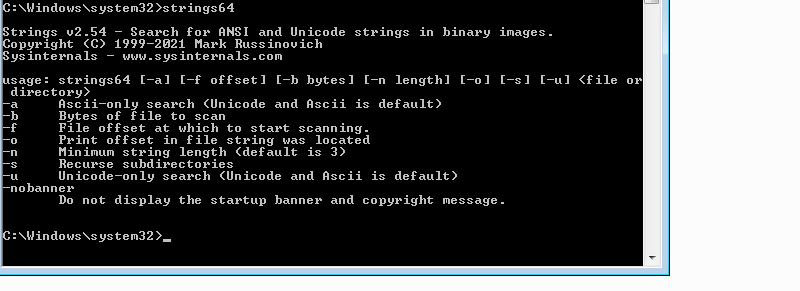
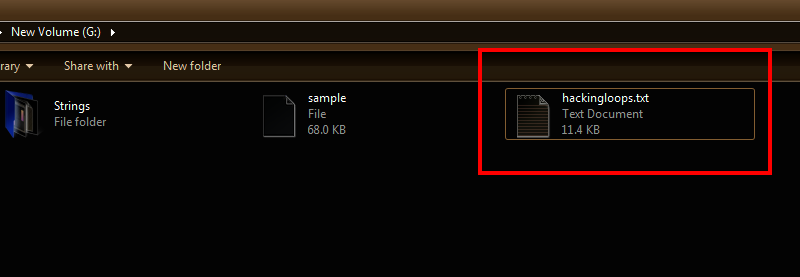
We can decide how many bytes to scan using -b parameter since there can be thousands of bytes in a malware code. We can refine the search by limiting the tool to search only ASCII or UNICODE characters. Using Strings tool, we can also mention the minimum number of characters (string length) in the code. Lets assume we want to analyze the code with all ASCII and UNICODE characters with minimum Strings length (-n) of 5 characters. We also want to copy the strings in a text file (e.g. hackingloops.txt). This can be achieved using the following syntax.
strings64 -n 5 (file path and name here) > (output text file path and name)
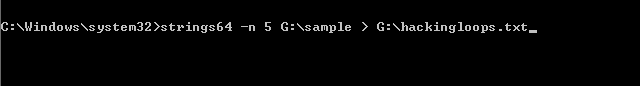
The above command creates a text file in the defined directory with the pre-defined length of strings.
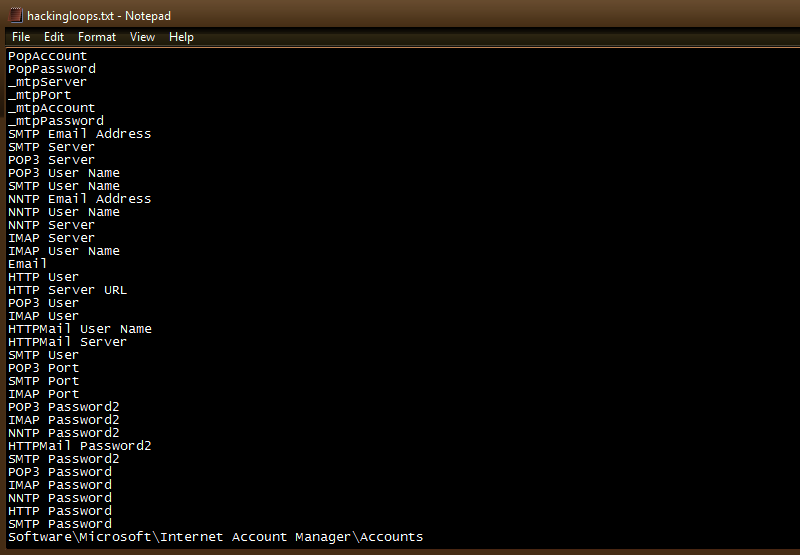
As a malware analyst, we can go through the captured data and look for different strings like libraries, URLS, emails, IP address etc.
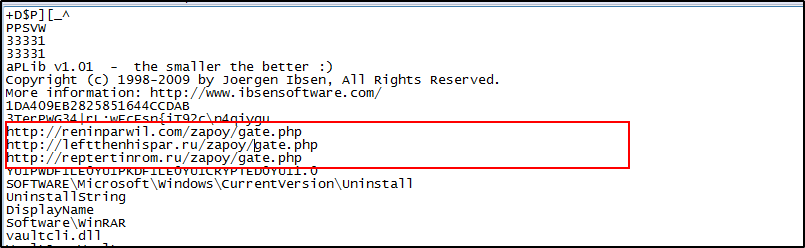
We can start with DLL libraries and the functions called by the program. The DLL libraries and functions are valuable indicators that can tell us the program’s functionality and goals. For instance, the sample malware calls the openvault function from vaultcli.dll library. This library and function indicates that the malware can be a password/data stealer. The advapi32.dll indicates that the malware can access the service manager and update/modify/delete/add the registry keys. The Crypt32.dll library indicates the use of cryptographic functions by the malware.
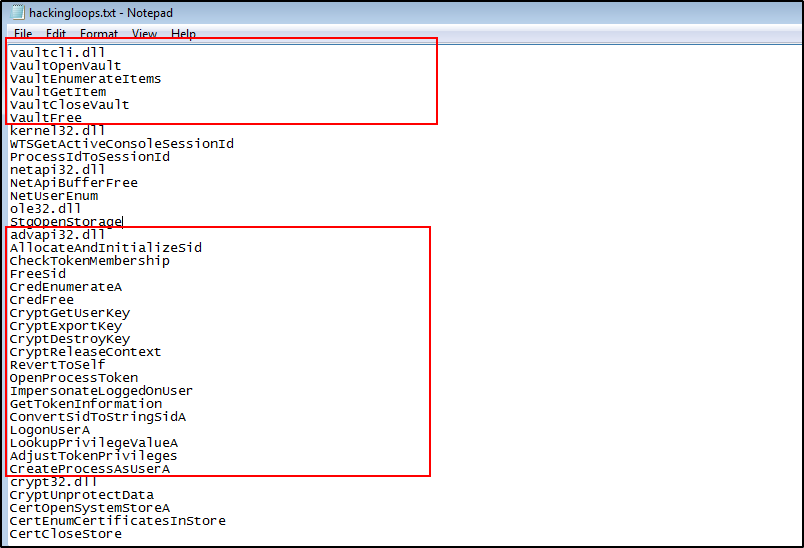
After exploring the dynamic link libraries and functions, we can search for IP address/URLS to see if the malware has interaction with some command-and-control center (C2C).
We can also search for different communication protocols. If there are any communication protocols like SMTP, POP3 etc. found in the malware code, there is a strong possibility that malware might need internet connection and network access to show its true behavior. In that case, we should provide fake internet and network resources to the malware.

Conclusion
Static malware analysis provides very useful information about the functionality and objectives of malware. Researchers can draw assumptions about the malware artifact by just looking through different piece of codes. However, static malware analysis can be a challenging task. The malware creators often use the legitimate libraries to hide the malware objectives. It has been observed that many malware codes are packed and they do not provide any hint about the malware binaries. Expert malware developers often use ordinal values instead of function names to make the static analysis more difficult.
