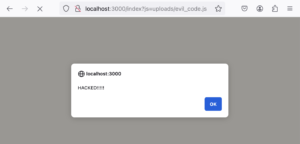
CSP vs XSS: How Content Security Policies block Cross Site Scripting
When it comes to web security, XSS is one of the most common vulnerabilities to find. It packs a big
When it comes to web security, XSS is one of the most common vulnerabilities to find. It packs a big

In this article, we will understand and perform Spiking and Fuzzing in detail. Before proceeding, disable Defender’s Real Time Protection

The most important task for an attacker, after gaining access to a target system or infrastructure, is maintaining access. And
In the initial attack vectors, we were able to compromise a user (Frank Castle). All this by gaining its hash