
How Sifter stacks and Automates Useful Penetration testing tools
There are many open-source penetration testing tools available to perform security auditing. The security professionals can get these tools from

There are many open-source penetration testing tools available to perform security auditing. The security professionals can get these tools from

Forced browsing is a type of web attack where the adversary tries to access web resources that are not referenced
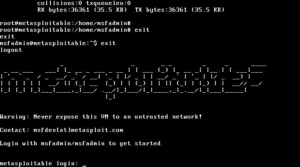
The Rapid7 Metasploit community has developed a machine with a range of vulnerabilities. Metasploitable 2 VM is an ideal virtual

Penblood is a web information gathering and vulnerabilities assessment tool. It can help penetration testers in mapping the attack vectors.