Quantum Computing -A Threat to Future Cybersecurity?
The current Cybersecurity architecture is based on cryptographic algorithms implemented all over the world. Authentication, digital signatures, encryption, electronic transactions,
The current Cybersecurity architecture is based on cryptographic algorithms implemented all over the world. Authentication, digital signatures, encryption, electronic transactions,
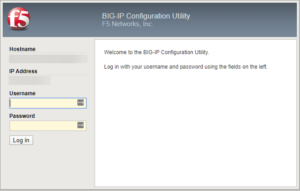
In a recent security update, the F5 networking equipment has been found vulnerable to Remote Code Execution (RCE) attack. The

The Equifax data breach is one of the deadliest cyberattacks in the modern times not only in terms of affected
Security is more important today than it has ever been in human history. It seems every week there are several