Hello friends. In my previous article “How hack email account” I explained all the possible ways to hack an email account. In my previous phishing tutorial “How to hack gmail account or password” I have explained how to hack gmail account or password using the phishing technique. That phisher is now outdated and most free web hosting servers no longer allow the creation of text files. This tutorial covers the latest Gmail Phisher and introduces new free web hosting servers.
Note: This is for Educational Purposes only. Please don’t misuse it. You will be solely responsible for any misuse.
| How to hack Gmail account or password |
Let’s first review what phishing actually is:
What is Phishing?
Phishing in ordinary vocabulary is a word derived from the word “fishing.” Just as in fishing, we make a trap for the “fish” to get caught; in the case of Phishing, we make a trap to hack the user’s password. “Phish” basically means fake, things that are deviating from the original product. Technically, Phishing is a technique to hack a victim’s account passwords using phish or fake pages. While phishing, we send the fake page links to the victim in spoofed manner so that they will not be able to identify that the page is fake. Now, when the victim enters their credentials on the fake page, two different processes occur simultaneously. First it writes a log file with the username and password, and the second process redirects the user to the original website page with the username entered while displaying the password as incorrect.
How to recognize Phish pages?
There are two ways to recognize Phish pages and both depend on the awareness of the user. There are some additional ways also to protect yourself from Phishing but we believe that prevention is the better cure. If you know how it’s done then you will be able to recognize when it’s happening.
Ways to recognize Phish pages:
1. Check the address bar; if the URL you are visiting does not match the original website link then it’s a fake page.
2. If you are a great coder or understand HTML then you can easily revert the attack back and check the hackers log file. But if you entered your own details by mistake, it cannot be deleted. For this, you need to use IDM and run the website grabber. In the log files you can see all details of the accounts the hacker has hacked.
What new features are in this Gmail phisher?
A new phisher means new features. What do you think I have added?
The awesome new features are listed below:
1. Incorrect password shown page bug removed
Previously when the user logged in using phisher, it redirected to the original page and displayed the password as incorrect. In this new feature, I have utilized the cookies from the user’s login attempt; when the victim logs in using the fake page, they are actually logged directly into their own account, without showing the message that says “incorrect password.” Technically, this is a form of advanced Phishing called “Tabnabbing.”
2. Log File Contains More Information
Previously, the log file only contained the username and password of the victim. Now it contains all the cookie details, along with IP address of the victim.
Steps to Hack Gmail Account Password Online:
1. Download the Gmail Phisher (Click here to Download).
2. Extract the rar file and now you will get three files namely:
- Index.htm
- Isoftdl_log.txt
- next.php
3. Now go to Free Hosting website and register a new account on it.
4. After registering go to File Manager on the website and create a new directory. We suggest you name it something like Gmail, but choose whatever you would like.
5. Now double click on the directory to open it and then click Upload. Browse the three different files one by one from the three upload boxes and click on upload.
6. Now Open the Index.htm page and you will see your fake page. It should look identical to Gmail’s original page. Below is a snapshot of the Fake Gmail Page:
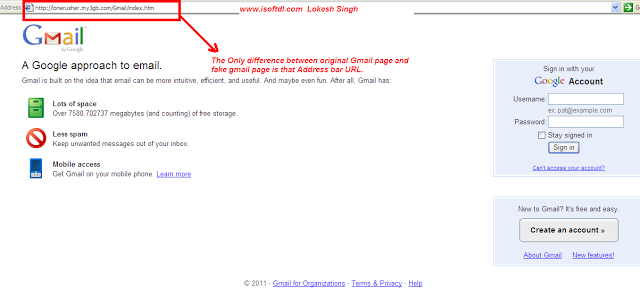 |
| How to hack Gmail account password online : Fake Page |
7. You can directly send the above URL to the victim, but it’s quite detectable. We need to spoof it so that it becomes difficult for the victim to recognize. For that, visit the domain maker website (click here to visit).
I also explained this in the previous article: Hack Gmail Account Step by Step
8. Now send the spoofed link in the mail to the victim as I explained in the post referenced above: Hack Gmail Account Step by step.
9. When the user logs in using the fake page, the data log file is written. It will look like this:
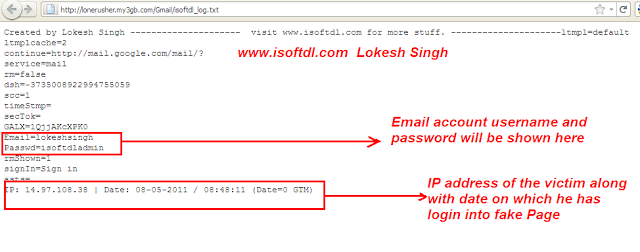 |
| How to hack gmail password : Log file |
10. That’s all friends. Now you have the user name and password of the victim.
To get our free books on hacking emailed to you, as well as more detailed information on Gmail hacking and other concepts, simply join our list.

kuwwat says
Break password
dipalimittal says
Password
Koonhart says
I what to hack gmail :sattawat748@gmail.com
madan says
hello lokesh, isend phishing page someone but he knew that phishing page and ty wrong creditional and use abusive word .how can hack his account by magic cookie and ip .plz tell me.
guruphotogallery says
where’s an download link
sahil says
i m not able to register webhosting website please explain