Remember the movie the Matrix and the character Morpheus? He helped guide the other good characters in the movie and really helped bring all the good things that happened together. Well, the tool Morpheus for pentesting is similar to that in that it makes use of some great other tools and brings out the best in them.
Morpheus is an open-source penetration testing tool that follows MAN IN THE MIDDLE (MITM) attack approach. The tool makes use of different back-end technologies like Ettercap, TCPKill, Msgsnarf, and Urlsnarf to launch a MITM attack and manipulate TCP/UDP data. Morpheus can automatically perform the following penetration testing tasks.
- Harvest Https/Http credentials
- Hosts discovery
- Hosts fingerprinting
- Firewall filtering
- Side-jacking attack
- Sniff network traffic
- Redirect network traffic
- Launch Denial of Service attack
- Payload injection in web pages
- Data manipulation
Although there are pre-configured filters available in Morpheus to launch the aforementioned attacks, we can edit or write our own filters to modify the functionality of the tool according to our requirements.
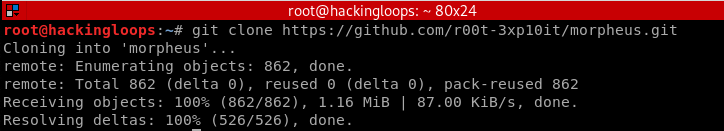
Morpheus Installation
Clone Morpheus using the following command
git clone https://github.com/r00t-3xp10it/morpheus.git
Navigate to the tool’s directory and run the following command to complete the installation process.
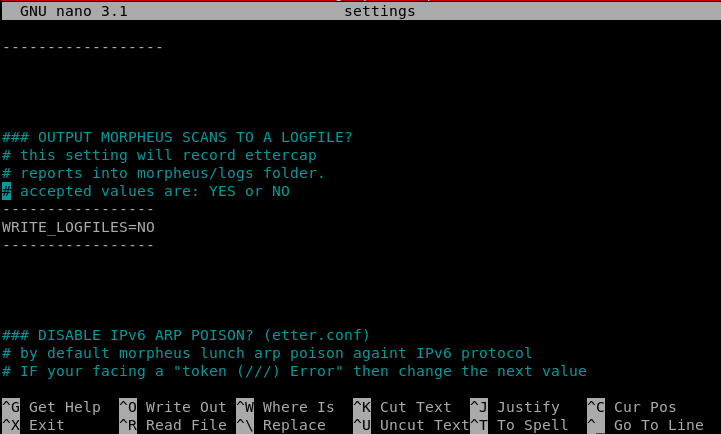
cd morpheus chmod -R +x *.sh nano settings
The nano settings is an optional command for modification in global configuration/settings of the tool.
As mentioned above, Morpheus makes use of some backend applications to carry out different tasks. Therefore, it requires the following packages to function properly.
apache2,ettercap, nmap, zenity, driftnet, dsniff, sslstrip-0.9, dns2proxy ,
How Morpheus Works?
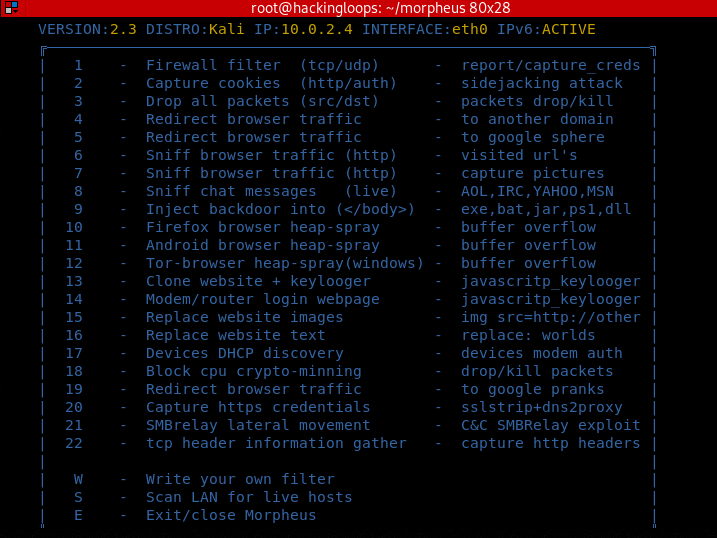
Running the following command in the terminal loads Morpheus tool and all the available modules as shown in the screenshot.
sudo ./morpheus.sh
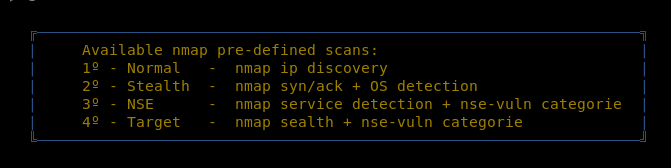
The above screenshot shows all the possible attacks that Morpheus can perform. We can test a few to demonstrate its working. For example, to launch the network scanner, type the Scan’s index number (letter S) in the terminal. Provide the necessary information like IP, range, etc. Morpheus supports four different scan modes i-e (i) Normal, (ii) Stealth, (iii) NSE, and (iv)Target.
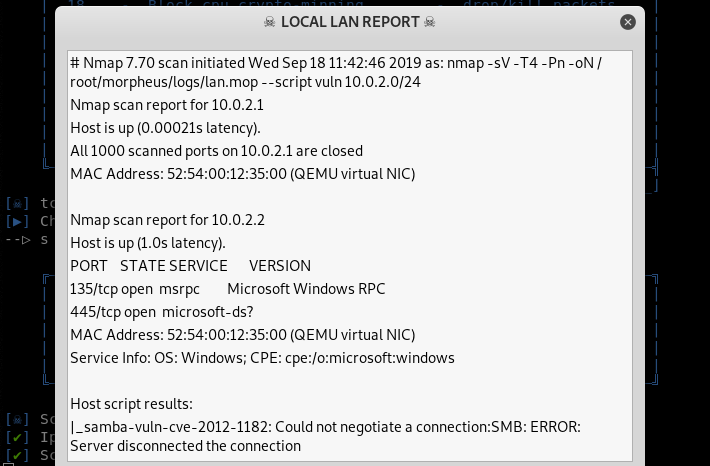
Once the pre-requisite information is fed into the tool, scanning starts automatically. The information like live hosts, open ports, and misconfigurations (vulnerabilities) are displayed on the screen as shown below.
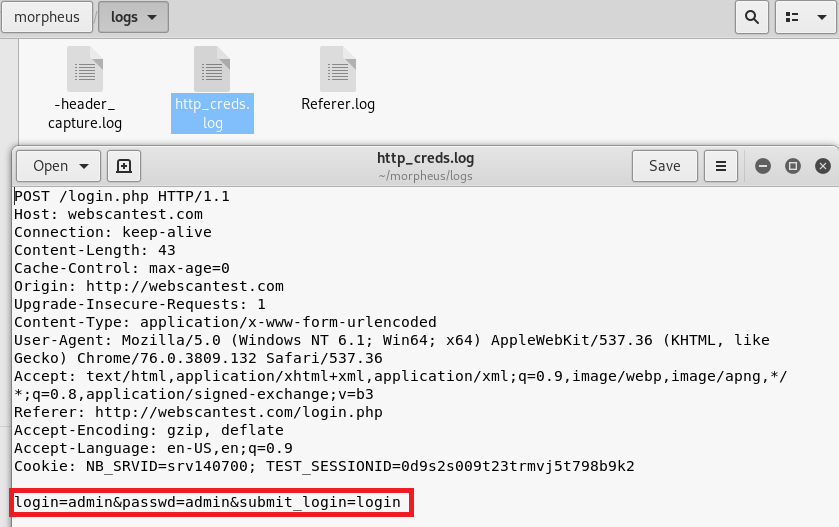
Firewall Filter is listed as the first module in the list that captures useful data packets and stores the results in logs folder in the directory. User credentials over any HTTP webpage are captured in plain text. The results are stored in files generated in the logs folder as shown below.
Apart from credentials, Firewall Filter captures a lot of other useful information, such as user-agent, session id, cookies information, encoding type, and POST/GET information.
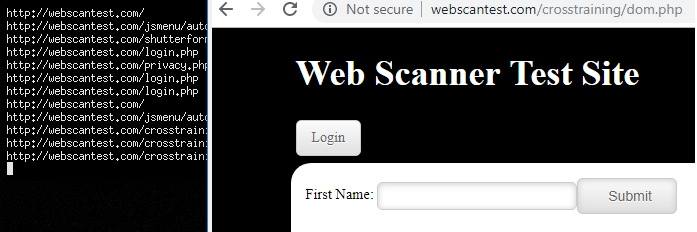
Sniff browser traffic (http) is another important feature of Morpheus that records all the URLs explored on target hosts. The URLs explored on the target hosts are displayed on the screen in real-time. We can also take screenshots of target hosts during the sniffing.
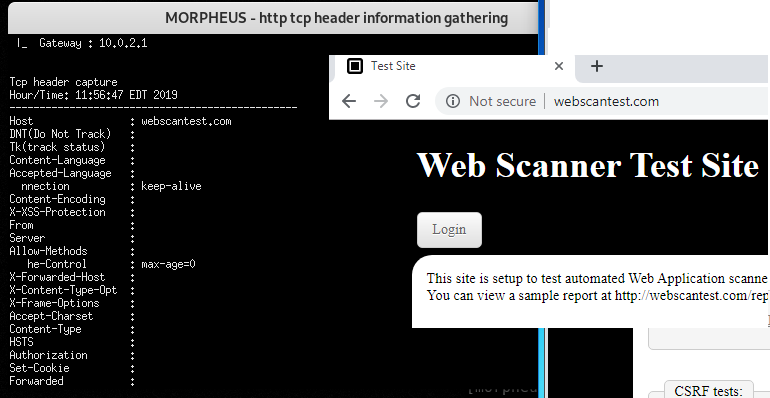
At #22 is the TCP Header Information Gathering module that captures and provides useful insight on TCP data packets. Following is an example screenshot of TCP header information captured while communicating with a test website.
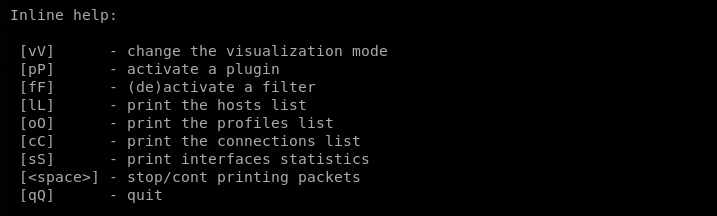
The process of utilizing other modules is similar to what we have demonstrated in the above examples. Inline help is an important Morpheus feature that we can call at any stage. Inline help allows penetration testers to change visualization mode, activate plugins manually, deactivate any filters, do host profiling, and other tasks shown in the following screenshot.
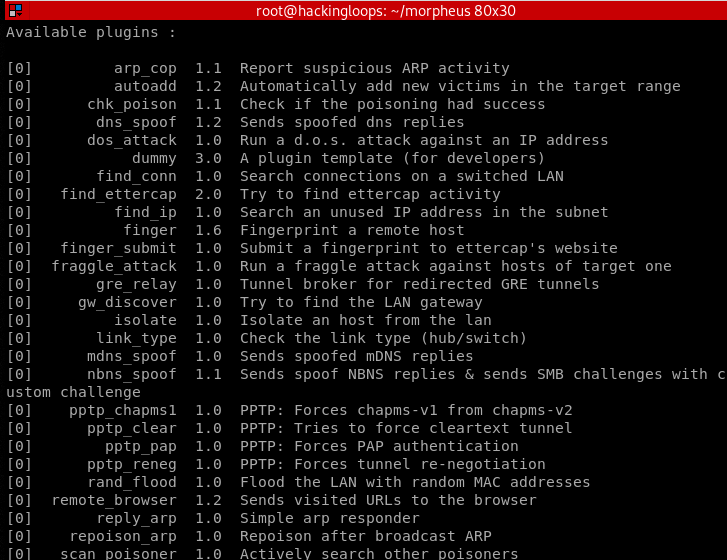
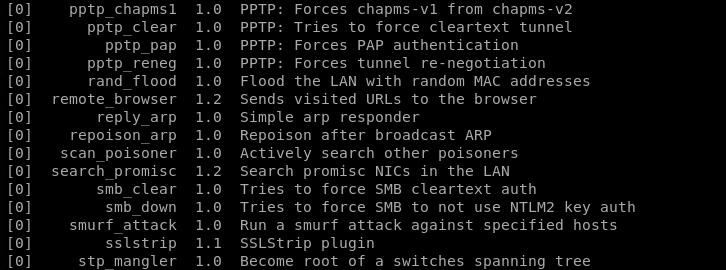
The following screenshots show the currently available plugins that can be manually activated from the command-line interface.
Summary
Morpheus is an important TCP/UDP data manipulation tool that can perform a variety of tasks like traffic sniffing, spoofing, hosts scanning, credentials stealing and performing cyber-attacks like payload injection and denial of service attacks. The tool is however less effective if HSTS (HTTP Strict Transport Security) feature is enabled on target hosts or there is a protection against ARP poisoning attacks.