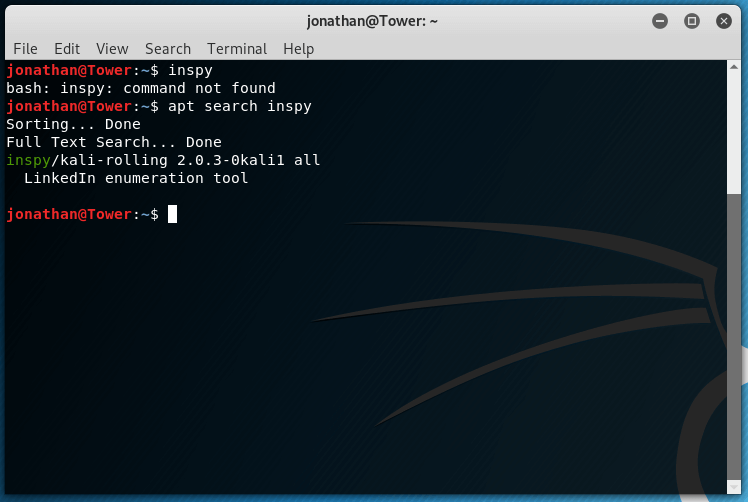
Information Gathering Using Kali Linux for Penetration Testing Information Gathering is a crucial step in penetration testing . Ideally the penetration testing begins with Information and needs a lot of effort at this step . In this tutorial we will explore some of the tools used for Information Gathering that are available in Kali Linux . Build and Verify an Email Address List using Harvester Here we will be using the tool called Harvester . Harvester Builds a list of email addresses for users at the target organization. The list of email addresses will then be verified to confirm they are valid. Start by … [Read More...]
Featured Articles
Editorial Picks
Latest Blog Updates
 Loading...
Loading...What is Penetration Testing ? All You need to Know
What is Penetration Testing ? Penetration testing is using the tools and techniques of malicious attackers to find and exploit weaknesses in a system in order to improve the defensive capabilities of the system. Penetration testing requires curiosity, cleverness, and a willingness to push the limits of what is possible. Legal Issues in Penetration Testing There is still a lot of legal grey area with regards to hacking as evidenced by the Weev and Aaron Schwartz cases. Generally, only the owner of a system can legally perform penetration testing against that system. Conducting a penetration test against any … [Read More...]
PowerSploit : Quick Shell for Penetration Testing
PowerSploit : Quick Shell for Penetration Testing While penetration testing , sometimes all we want is a shell and no meterpreter or other RAT functionalities . This can be due to plenty of reasons : only shell access is less noisy , more chances of evading the Anti virus engines , less chances of inappropriate exploitation during pentest and so many more . This Tutorial will get you the quick shell access you need during the penetration testing in the easiest way . For this we will be using Powersploit . PowerSploit mainly uses Powershell for Windows Exploitation . But how to use Quick Shell for Penetration … [Read More...]
Ultimate Extension Spoofing Tutorial
Best Extension Spoofing Technique Tutorial Ultimate Extension Spoofing Tutorial. NO DOWNLOADS required !! NO external Tool Needed !! Change the extension of your .exe to .pdf .docx , .mp3 !! Real Method ..... !! This tutorial will show you how to make your .exe (or .com/.scr) files look like .jpeg/.mp3 or any other filetype (my favourite is .pdf and .docx)! By normally changing the extension to e.g .mp3, will corrupt your file, but with this exploit your file will still be executable! Also this is no FUD tutorial . This is just a technique to spoof the extension using the loopholes in windows . Here is a … [Read More...]
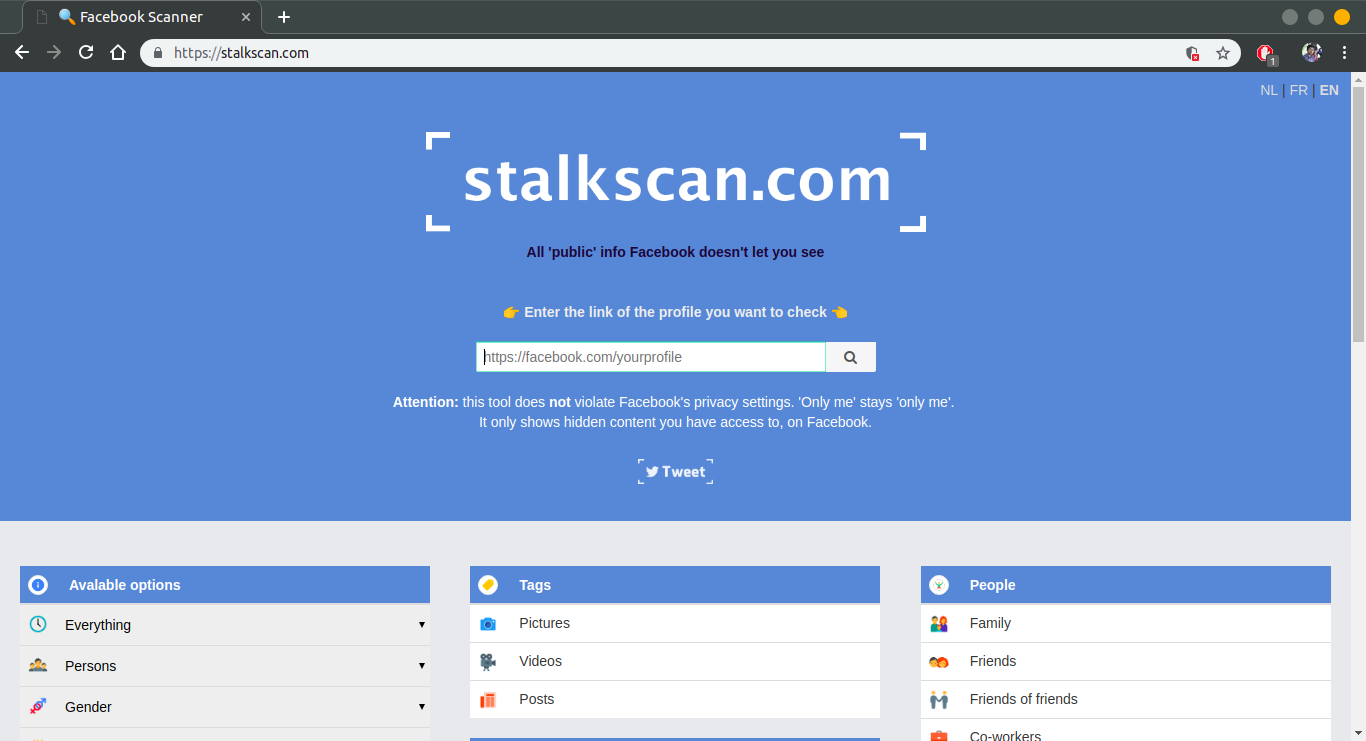
Google, Facebook May be Leaking your Data : Update
Google, Facebook May be Leaking your Data We are aware about the fact that most websites are tracking our location and saving our data and may be selling them that to third party. But the Question is that two top Brands Google Facebook are also doing that??? Let focus on research done by top Researcher Tim Libert, a privacy researcher at the University of Pennsylvania, reveals how serious this problem actually is. According to Libert's research, 9 out of 10 websites leak users' data to a third party, usually without the knowledge and the consent of the user. [box ENGINE="shadow" align="" class="" width=""]In … [Read More...]