Word / Excel Exploits using Metasploit During Penetration Testing Metasploit is the favorite exploitation framework among the penetration testers . Metasploit can be used in a variety of penetration testing scenarios . One of the easiest way of spreading the exploit code through an exe file . But the major drawback in this technique is that the Antiviruses might catch the EXE as malicious as the AV engines more cautious for the PE files . So are the Targets now . The Good News : Metasploit comes with Exploits for the Word and Excel Too . This means that you can create malicious word / excel documents that can … [Read More...]
Featured Articles
Editorial Picks
Latest Blog Updates
 Loading...
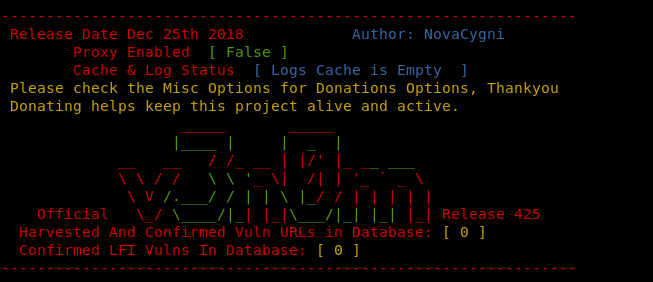
Loading...Finding SQLi Vulnerable Websites in a Web Server
Finding SQLi Vulnerable Websites in a Web Server SQL Injection (SQLi) vulnerability is not new and is one of the most dangerous vulnerabilities present in web applications . SQL injection is a very dangerous vulnerability and can lead to stealing of the data or even complete defacement of the website . If anyone is targeting your website , it is not essential that they do so by attacking your website directly . What they can do is to look for SQL Injection vulnerability on any of the websites on your server or your IP . Once the server has been compromised , the websites hosted on it can also be compromised . … [Read More...]
Execute JPeG Files As EXE : Only For Penetration Testing
Execute JPeG Files As EXE : Only For Penetration Testing While Penetration Testing , we come across scenarios where we need to social engineer in order to get the malware executed and test the strength of the organisation's employee's cyber security Awareness . Well here is a way to do so . What if we could get a Jpg extension file executed as an EXE (PE : Portable executable) . The good news is , yes this is possible . Here is a tutorial will show you how to create JPG files that will act like EXE (PE) files. #Disclaimer : Please don't perform Un-Authorized penetration testing . It's Illegal . Any … [Read More...]
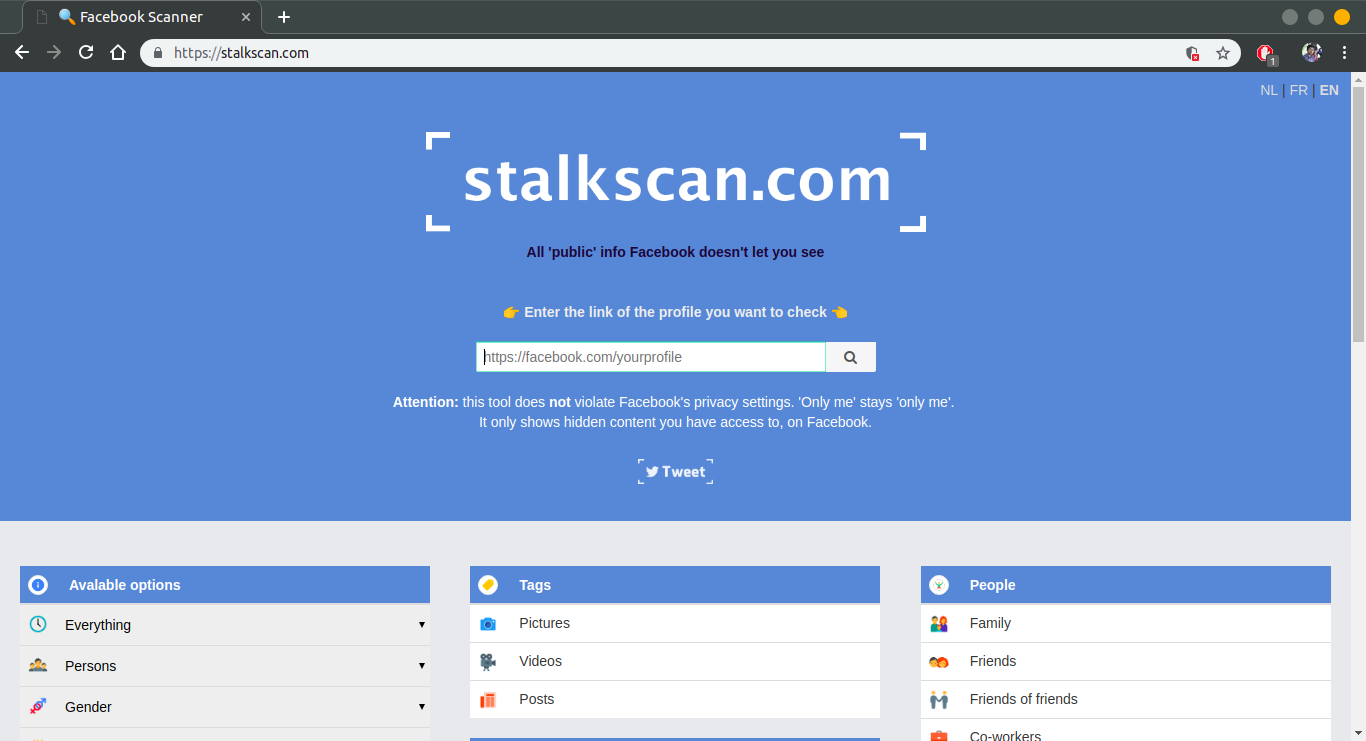
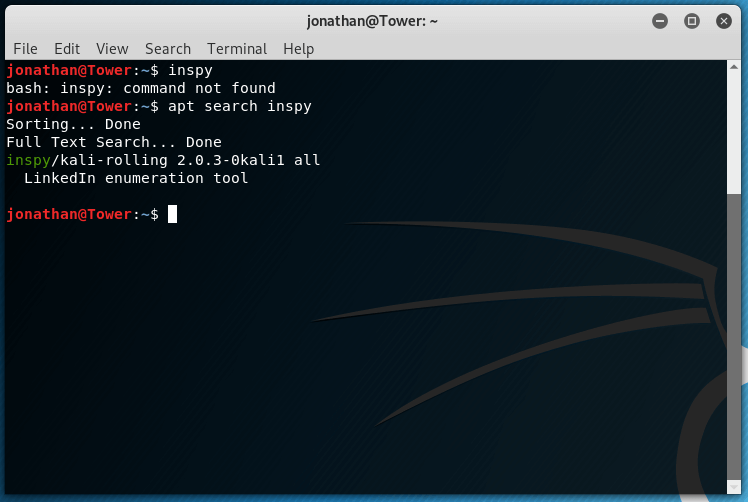
Profiling a Website for Penetration Testing
Profiling a Website for Penetration Testing Website Profiling is the first critical step in the penetration testing and helps to build initial foundation for the testing . Many penetration testers choose to do this via computer; they use exploits and methods to gain information about the website (this is a key process in penetration testing . I've found through my times that it's often more efficient for higher profile targets to use the humble telephone. In this tutorial I'm going to detail the process of gaining information about your website, both through the phone and the computer. 1 - Analyzing your … [Read More...]

Hackingloops Turn Social – Hackers First Social Networking Website
Hey Friends, it's your friend Lokesh, owner of Hackingloops. I would like to thank all of you for support you have provided to make Hackingloops into a success. This motivates us to do something new and today with all your support we have added new features to Hackingloops. Hackingloops now allows you to interact with other Hackers, share tutorials with other users, write forums and much more. So Hackingloops has opened a completely new Social Networking Platform for Hackers. Features added to Hackingloops - Hackers First Social Networking Website: Register on Hackingloops and create your profiles.(Click … [Read More...]