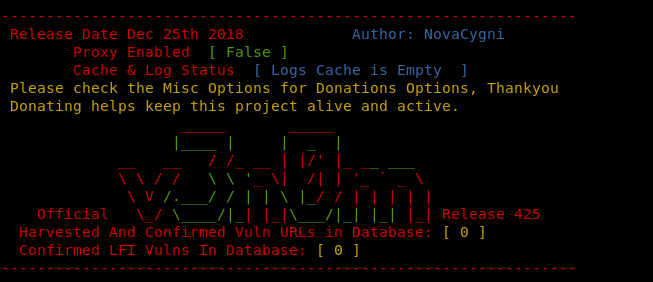
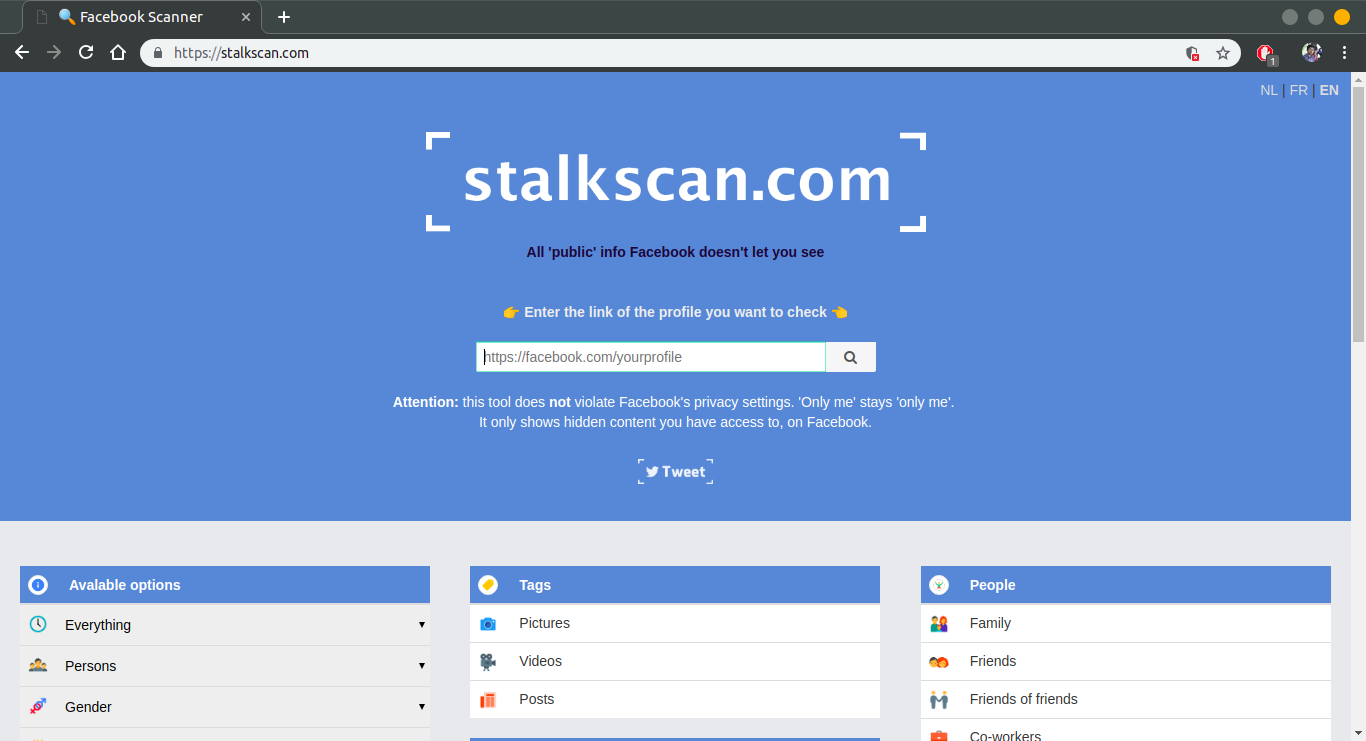
5 Ways to Ensure Security of Networks : Twenty-four hours a day, seven days a week, 365 days each year – it’s happening. Whether you are awake or asleep, in a meeting or on vacation, they are out there probing your network, looking for a way in. A way to exploit you; a way to steal your data, a place to store illegal content, a website they can deface, or any of a hundred other ways to mess with you for the simple joy of it all. And they can do this with relative ease, even in an automated fashion, with simple tools that are readily available to all. So friends lets learns how to ensure security of networks using … [Read More...]





 Loading...
Loading...